Recently, a sophisticated operation known as Arkanix Stealer, which surfaced on various dark web forums in late 2025. This particular malware stands out not just for its data-stealing capabilities, but for the clear fingerprints of Large Language Model (LLM) assistance in its code. This development marks a new era where the barrier to entry for creating complex cyber-threats is lower than ever before.
The Dual-Language Strategy: Python vs. Native C++ Payloads
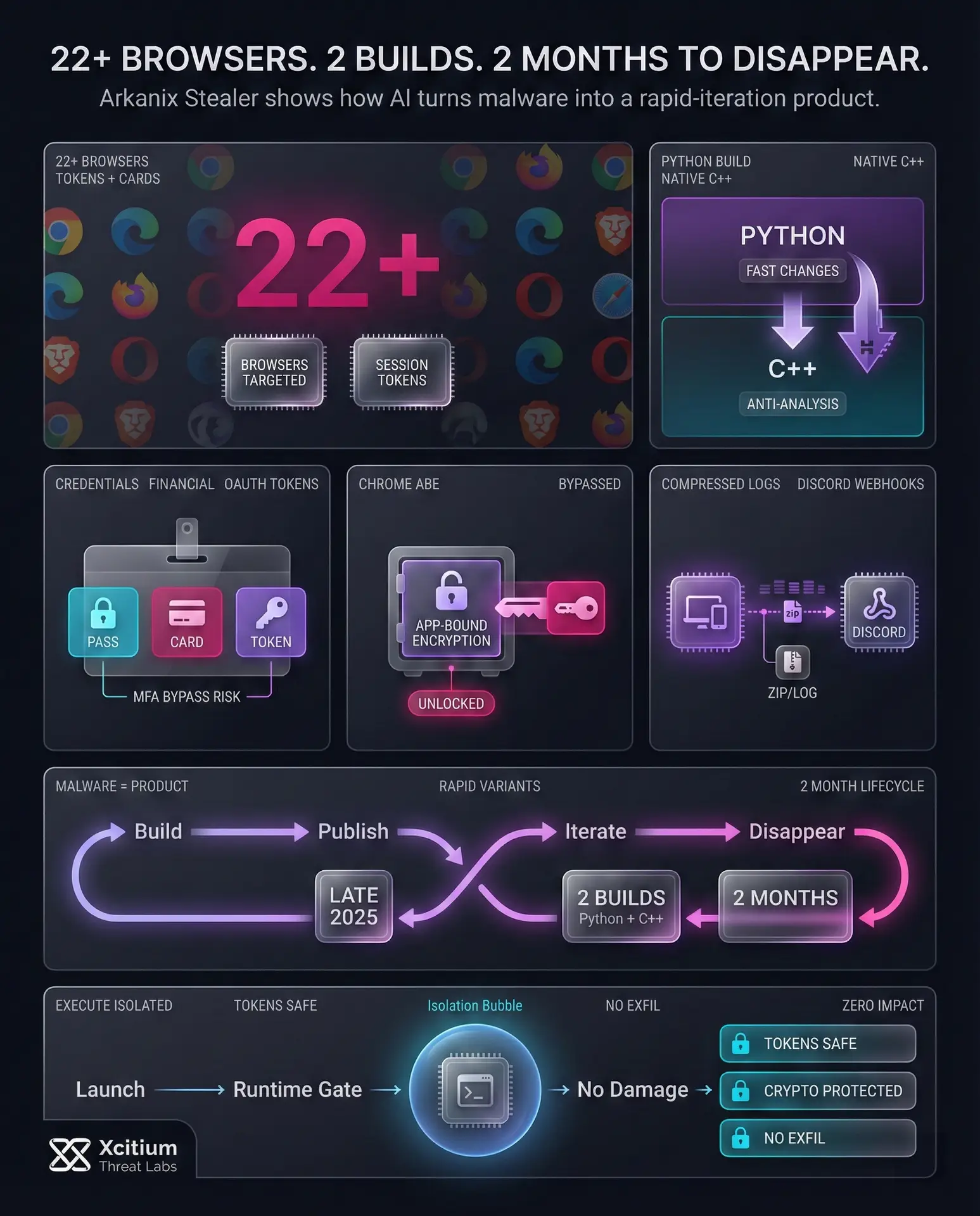
Arkanix Stealer followed a strategic approach of dual implementation to maximize the scope and efficiency of the malware. The primary level of Arkanix Stealer implemented a Python-based approach, which is often bundled through tools such as PyInstaller or Nuitka to avoid detection.
Additionally, it provided the flexibility of dynamically updating the configuration from the attacker’s panel. This enabled the malware to change dynamically in real-time depending on the specific goals of the campaign.
The premium version, on the other hand, provided a much more powerful native C++ payload with integrated anti-analysis code. This version used VMProtect to protect its code from security researchers and automated analysis systems.
Moreover, the native version included dedicated code-stealing modules for Remote Desktop Protocol (RDP) credentials and high-value gaming account data. The attackers could serve a variety of cybercriminals, from petty thieves to sophisticated attackers looking for particular corporate or financial data.
ARKANIX STEALER LIVE DEMO
Visualizing the technical lifecycle of AI-generated threats.
Arkanix uses Python-based bundling (Nuitka/PyInstaller) to slip past basic signature scanners.
Utilizes custom modules to decrypt Google’s “App-Bound Encryption,” making passwords readable.
Targets 22+ browsers simultaneously. Grabs session cookies to bypass Multi-Factor Authentication (MFA).
Compressed logs are sent to the attacker via Discord Webhooks or specialized API panels.
Breaking the Encryption: How Arkanix Targets Your Sensitive Data
The main aim of Arkanix was to perform the complete and comprehensive harvesting of digital identity and financial assets from the infected systems.
The malware had its sights set on a wide range of 22 different web browsers, including mainstream browsers such as Google Chrome to some of the most private browsers such as the Tor Browser. The information to be harvested by the malware from the infected systems
- Stored Credentials: The usernames and passwords stored in the browser’s database.
- Financial Data: The credit card information, autofill information, and billing addresses.
- Session Tokens: The 0Auth2 tokens, which enable attackers to bypass multi-factor authentication.
- Crypto Assets: The information from popular wallet extensions such as MetaMask and Binance.
Perhaps the most worrying feature of the premium version of Arkanix was the inclusion of the ChromElevator application. This application is specifically designed to bypass Google’s App-Bound Encryption (ABE), which is essentially a security feature designed to protect sensitive information from unauthorized access.
The fact that Arkanix was able to successfully evade these security measures speaks to the fact that even the most recent forms of encryption are not safe from the ever-evolving nature of malware.
A Business-First Approach: MaaS and Referral Programs
Unlike many traditional malware operations that operate in the shadows, Arkanix adopted a surprisingly public-facing business model. It functioned as a Malware-as-a-Service (MaaS) provider, offering a polished control panel and dedicated support through a Discord server. The developers implemented a referral program to aggressively expand their user base. Existing users could earn extra hours of premium access by bringing in new customers, who in turn received a free trial week.
This professionalized approach to cybercrime suggests that the developers viewed Arkanix more as a software product than a clandestine operation. The use of community feedback loops and rapid feature deployment cycles mirrors the methodologies used by legitimate tech startups.
The Short Lifecycle of Modern Infostealers
While the Arkanix project was full of advanced features and heavily marketed, the project itself was surprisingly short-lived. The entire project, including the control panel and the Discord community, was removed only two months after the project first appeared.
It is theorized that the project was intended to be a “one-shot” type, intended solely for financial gain. The fact that these threats disappear quickly poses a problem for traditional security measures.
The brief existence of Arkanix represents an example of what the future of cyber threats may hold. This is because, with the increasing pace at which AI is helping to develop malware, there will be many “flash” campaigns that come and go before they can be fully understood and contained.
This is because, with the speed at which code can be developed using LLMs, even if one example is identified, another can be released almost immediately.
Protecting Your Digital Identity from AI-Enhanced Threats
The advent of AI-assisted malware, such as Arkanix, calls for a more proactive approach to personal and corporate security measures. In order to combat such emerging threats, which can bypass conventional detection mechanisms, it is necessary to adopt a zero-trust approach to security, such as having strict control over browser extensions and using hardware security keys for authentication, thereby reducing the probability of data exfiltration.
Organizations should prioritize employee education regarding phishing, as this remains the primary infection vector for most infostealers.
As a result, a combination of technical safeguards and human vigilance is the only effective defense against the next generation of AI-powered cybercrime. While Arkanix may have been a short-lived experiment, the lessons learned from its analysis will be crucial for defending against the more permanent threats that are surely on the horizon.
Conclusion: AI Has Turned Malware into a Rapid-Iteration Product
Arkanix Stealer is a clear example of how AI is lowering the barrier to building sophisticated cybercrime tooling. In late 2025 it surfaced with two operational tracks, a Python based build optimized for fast changes, and a premium native C++ build hardened with anti analysis protections. It was marketed like a product, complete with a control panel, support, and a referral program, then it disappeared within two months.
Why This Is a Structural Shift
For decades, malicious intent needed a carrier. Attackers had to ship code, and defenders could anchor detection to artifacts like binaries, scripts, and macros.
AI accelerates the break from that model. With LLM assistance, malware authors can generate new variants quickly, refactor modules on demand, and adapt faster than signature based detection can keep up. The payload changes, the infrastructure changes, the campaign changes, and the window for static indicators collapses.
Why Organizations Are Exposed
Arkanix shows why infostealers remain one of the most dangerous initial access tools.
- Targets 22+ browsers and steals stored credentials, financial data, and session tokens
- Focuses on OAuth tokens and cookies to bypass MFA
- Includes specialized modules like ChromElevator to bypass Google App Bound Encryption
- Uses fast distribution and rapid updates, making traditional detection lag behind
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
With Xcitium Advanced EDR, the moment Arkanix attempts to execute, the chain breaks at runtime. The stealer can start, but code can run without being able to cause damage. Credentials, tokens, and wallet data remain out of reach, and exfiltration never becomes impact.
Defend for the Speed of AI, Not the Speed of Signatures
Arkanix may have been short lived, but the model is durable. AI is making malware faster to build than defenders can fingerprint. Security has to anchor on architecture, not artifacts, because you cannot scan a thought.