Continuous Malware Research delivering Early Warning, Actionable Intelligence, and Preemptive Protection against emerging cyber threats Worldwide.

A Stray “!”: The Tiny Typo That Opened a Huge Hole in Linux Security CVE-2026-23111 is...

The antivirus engine included in Microsoft Defender comes with another zero-day vulnerability...

The Silent Ransom group started its latest extortion attack on law firms operating in the United...

EDR evasion is now entering a new era. Rather than manually tinkering with samples of the malware,...

TA4922 Chinese cyber-criminals have increased their malicious activities through evolving hacking...
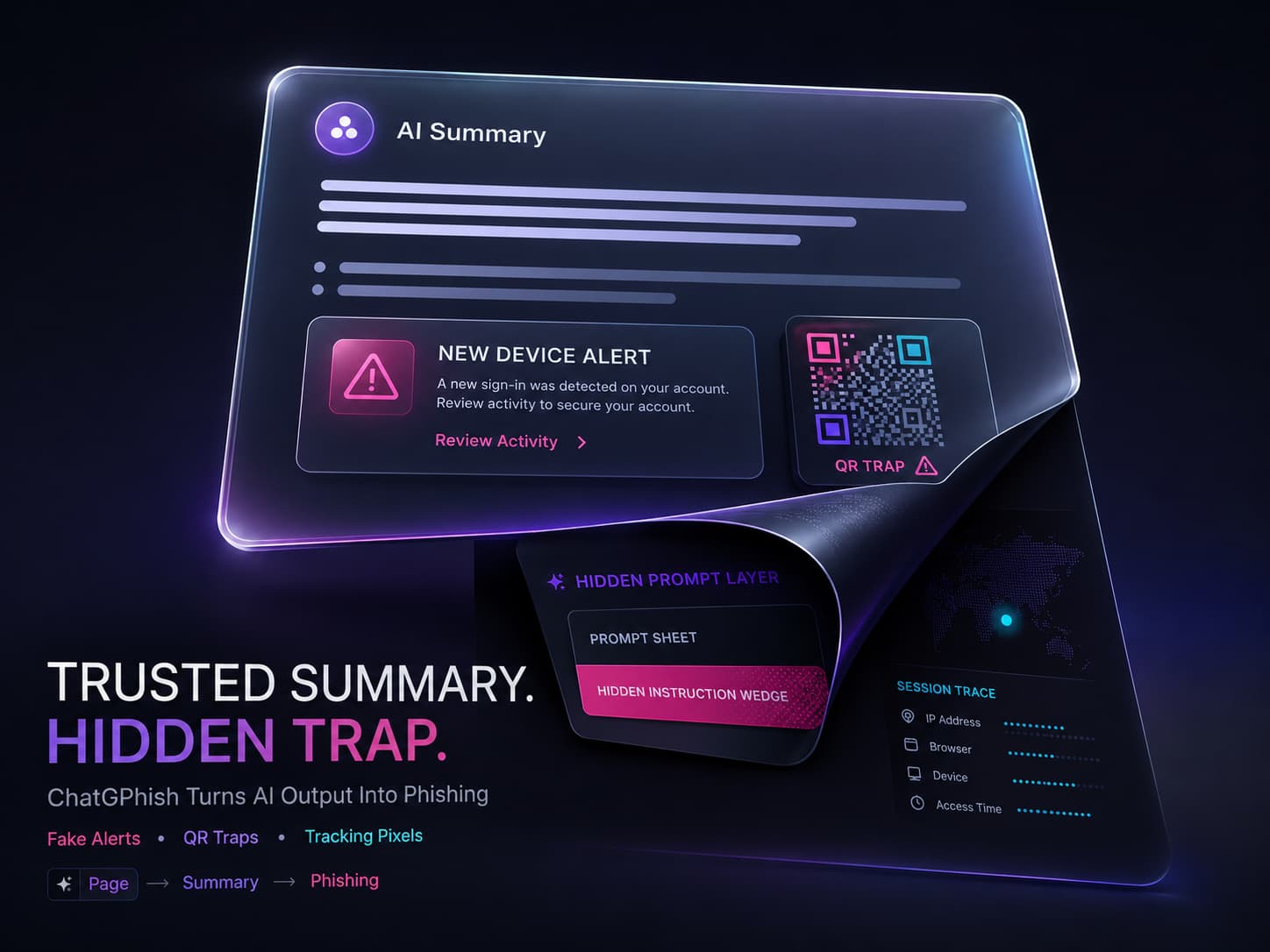
How ChatGPhish Works: Exploiting ChatGPT’s Trust ChatGPhish is a browser-based attack on...

Phishing Email Compromises npm Maintainer Phishing email impersonating npm support lured the...

Charter, which offers internet, TV, and phone services under its Spectrum brand, initially...

A new campaign discovered recently, shows how attackers abuse ChatGPT’s sharing feature and...

Microsoft recently released emergency updates to plug two zero-day vulnerabilities in its Defender...

YellowKey is a recently discovered zero-day exploit for Windows 11 that can circumvent BitLocker...
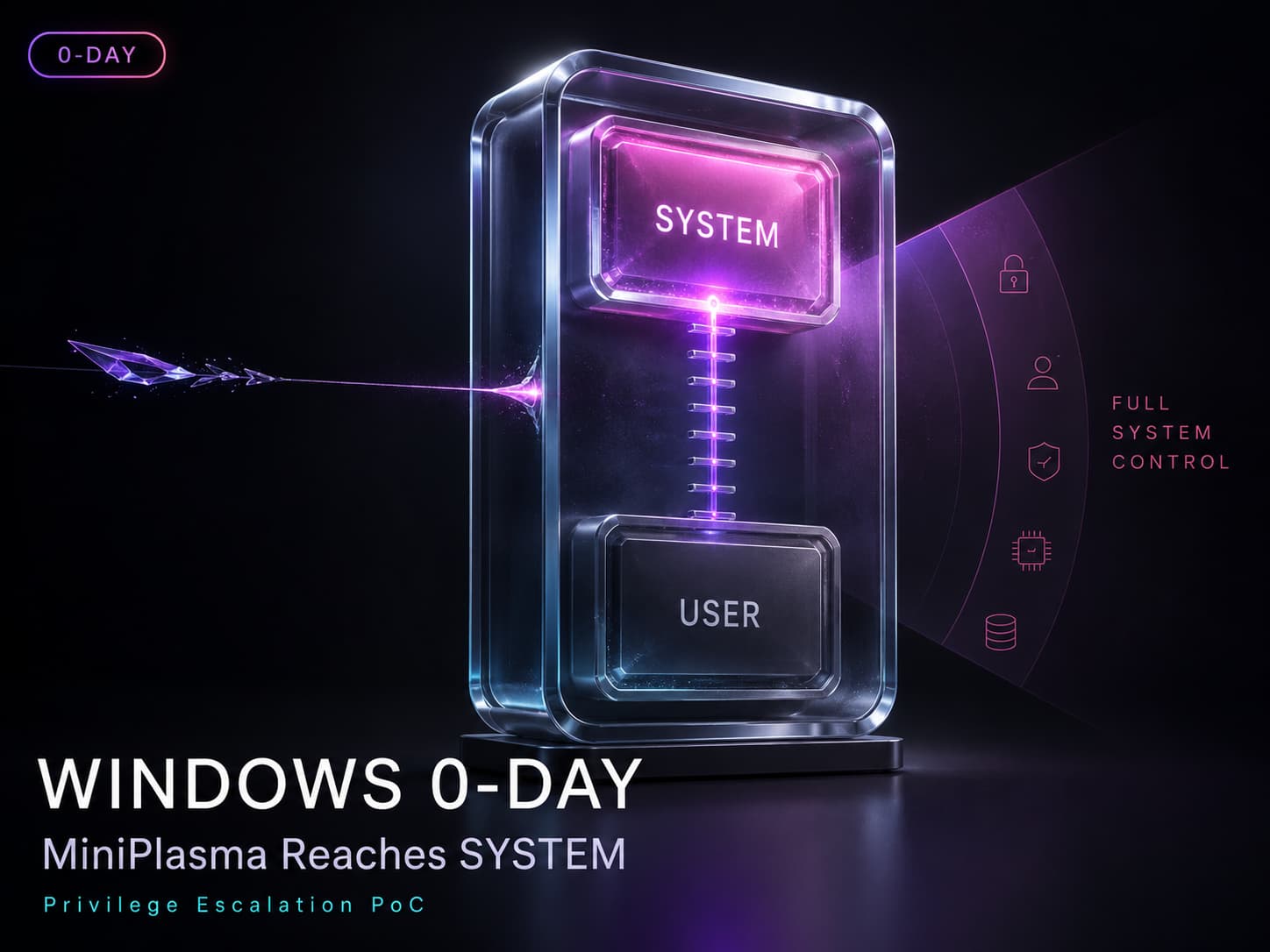
MiniPlasma Turns A Standard Account Into Full Windows Control MiniPlasma is an exploit aimed at...
Xcitium exists to ensure that people can embrace technology fully, without the shadow of insecurity hanging over them. We’re here to give users the freedom to explore, create, and connect without fear. Whether it’s preventing unknown files from compromising systems or offering innovative approaches to endpoint protection solution, Xcitium’s technology is designed to foster confidence. We believe that by keeping the digital ecosystem secure, we’re directly contributing to human evolution—by enabling people to take full advantage of the tools that define our era.
Book a Demo