Microsoft Teams Social Engineering Phishing
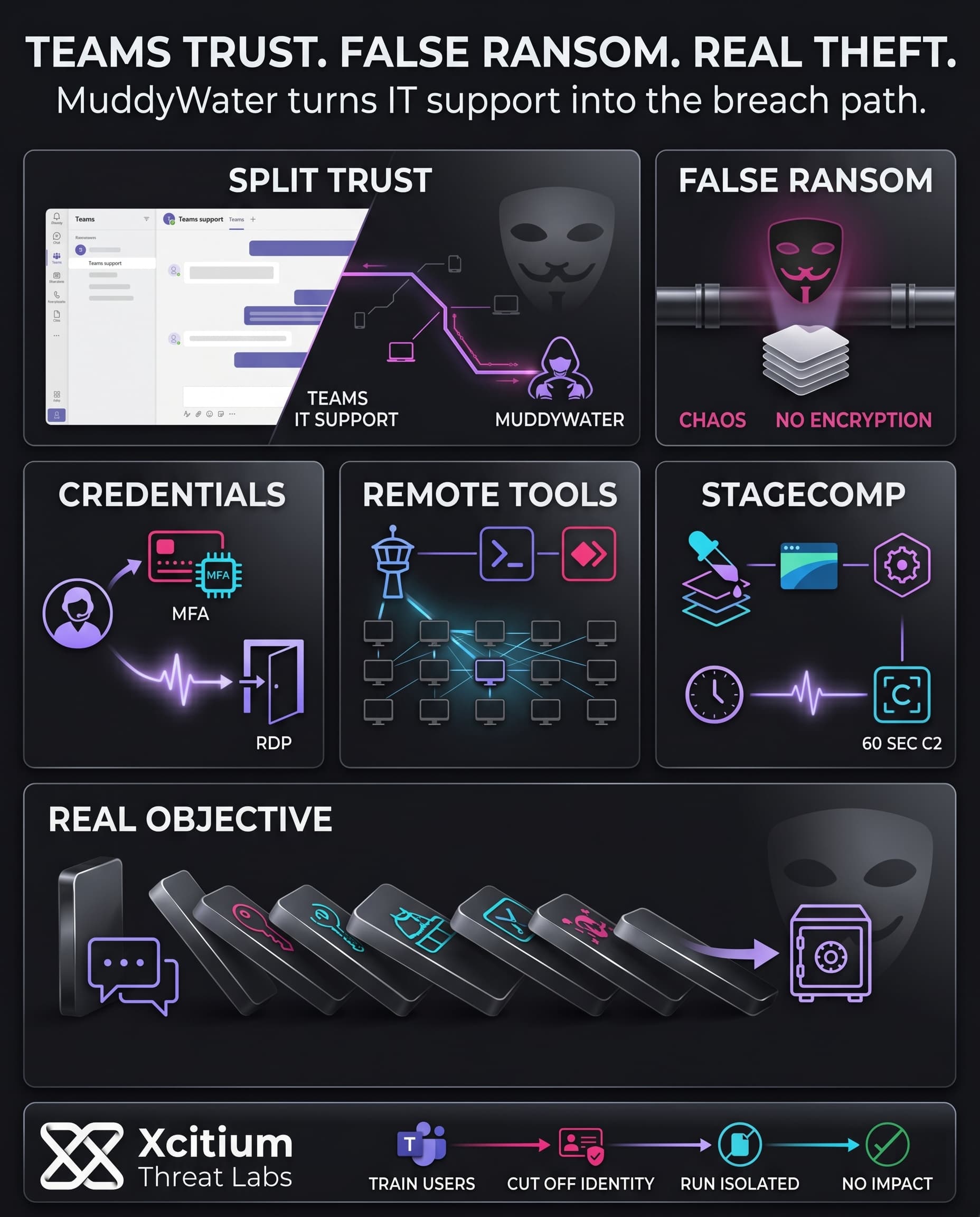
The Iranian-related APT (MuddyWater/Seedworm) targeted Microsoft Teams in an active session-based spear-phishing campaign. Using external sessions, which include chats and screen sharing capabilities in Teams, hackers impersonated IT staff to get victims to disclose credentials and even MFA codes. This kind of real-time use of Microsoft Teams made it hard for the company’s security measures to detect this kind of attack.
Leveraging the trust of users within the corporate infrastructure, the actor stole working credentials and manipulated multi-factor authentication, then switched immediately to system-level access. In the first wave of activity, the actor used simple reconnaissance commands (ipconfig, whoami) to manipulate victims into typing in their password into a text file.
- Illustration: Victims were prompted to copy and paste their credentials into newly created text documents on their computer, which gave the attacker full access to these accounts.
- Outcome: Using stolen credentials and MFA, the attacker had access to the company systems through RDP and other remote access tools.
Ransomware Facade Masks Data Theft
While the scenario seemed typical ransomware (Chaos RaaS), there were no signs of any file encryption activity. Rather, the attackers pretended that they carried out a ransomware attack. This is because ransomware groups using Chaos ransomware are known to offer double and triple extortion threats, such as making data public or conducting DDos attacks in case they are not compensated.
What was clear from this cybersecurity analysis is that the ransom claim was a ruse. There were no signs that the attackers proceeded to encrypt any files but rather went straight into lateral movement and exfiltration. It is evident from the dissonance created that the ransomware attack was an act. When victims found their files on a leak site after receiving ransom emails, it was all too late for the intruders.
Downloader and RAT Tradecraft
Once inside, the attacker leveraged remote admin tools like DWAgent, AnyDesk, and RDP to move laterally in the network. The intruder deployed a series of stages consisting of ms_upd.exe which is known as stagecomp. This dropper gathers information and reaches out to its C2 server, moonzonet[.]com, and downloads three other files:
- WebView2Loader.dll: An authentic DLL provided by Microsoft.
- Game.exe: A RAT dubbed Darkcomp that pretends to be the Microsoft WebView2APISample app.
- visualwincomp.txt: An encrypted configuration file with information about its C2 server.
Once ms_upd.exe launched, Game.exe persists by contacting its C2 server every 60 seconds to receive instructions. This RAT is capable of executing shell commands, running scripts, and modifying files. It is important to note that upon further examination of Game.exe, it has been discovered that it includes malicious modifications to Microsoft’s WebView2API sample project.
Case Study: Xcitium vs. MuddyWater Ransomware
This demonstration shows how Xcitium protects endpoints against a MuddyWater-linked intrusion campaign abusing Microsoft Teams social engineering, credential theft, and staged malware delivery.
In this controlled test, the attack simulates tactics observed in real-world incidents where attackers impersonate IT support personnel, harvest credentials and MFA codes, and deploy additional payloads for persistence, remote access, and data exfiltration.
The intrusion chain includes PowerShell execution, reconnaissance activity, remote administration tools, the Stagecomp downloader, and a trojanized WebView2-based RAT disguised as a legitimate Microsoft application.
Xcitium’s ZeroDwell technology automatically classifies the unknown processes as untrusted and places them into isolation at execution.
As a result, payload execution, persistence attempts, credential access activity, and outbound C2 communication are fully isolated before they can impact the endpoint.
MITRE ATT&CK Tactics, Techniques, and Procedures (TTPs)
Campaign Analysis & TTPs
Indicators of Compromise (IOCs)
Key file IOCs include:
- ms_upd.exe (SHA256: 24857fe8…4d14): Initial downloader (Stagecomp).
- Game.exe (SHA256: 1319d474…f97b6): Custom RAT masquerading as WebView2.
- WebView2Loader.dll (SHA256: a47cd0dc…82f3a): Legitimate DLL fetched by the dropper.
- visualwincomp.txt (SHA256: c86ab271…f1e0): Encrypted RAT config holding C2 addresses.
- DWAgent executables (dwagent.exe, dwagsvc.exe, dwaglnc.exe) and AnyDesk.exe: Remote management tools deployed for persistence.
Network IOCs of note:
- Domains: adm-pulse[.]com (fake Quick Assist login portal), moonzonet[.]com (Game.exe C2), uploadfiler[.]com (exfiltration C2).
- IPs: 172.86.126[.]208 (hosted
ms_upd.exe), 77.110.107[.]235 and 93.123.39[.]127 (used for Teams connection), 116.203.208[.]186 (contacted by renamed pythonw.exe). - Onion: Chaos RaaS negotiation site at
hptqq2o2qjva7lcaaq67w36jihzivkaitkexorauw7b2yul2z6zozpqd[.]onion.
These artefacts especially the unique file hashes and domains are strong red flags of this intrusion. For example, the ms_upd.exe binary was signed with a code certificate (“Donald Gay”) previously used by MuddyWater in other attacks.
MuddyWater Ransomware SHA-1 Samples & Zero‑Dwell Threat Intelligence Reports
Attribution and False-Flag Strategy
Multiple clues tie the incident to the MuddyWater APT (Iranian MOIS-linked). The reused “Donald Gay” code-signing certificate links this malware to previous MuddyWater operations. The moonzonet[.]com C2 domain was also seen in recent Iran-aligned campaigns. Even the use of pythonw.exe for process injection and the interactive Teams “IT support” guise match MuddyWater’s signature tradecraft.
The ransomware elements (Chaos branding, extortion emails) were likely just a smokescreen. In fact, MuddyWater has increasingly adopted cybercriminal tools to create plausible deniability while focusing on intelligence gathering. By mimicking a popular ransomware group, the attackers hoped defenders would fixate on immediate threats (encryption, leaks) and miss the real purpose, long-term access and data theft. The absence of file encryption, despite Chaos artifacts being present, underscores this strategy.
MuddyWater’s strategy mirrors a broader Iranian trend: blending espionage with extortion tactics to obscure intentions. In this case, the “ransomware attack” was a false flag a veil for credential harvesting and network infiltration.
Conclusion: When Microsoft Teams Becomes the Breach Path
The MuddyWater campaign shows how modern APT operations no longer need to start with malware. They start with trust. By impersonating IT support inside Microsoft Teams, attackers pushed victims into sharing credentials, approving MFA, and enabling access that looked legitimate enough to bypass normal suspicion.
The ransomware story was only the mask.
The real objective was access, persistence, and data theft.
Why This Threat Matters
This attack is dangerous because it blends social engineering, identity abuse, and staged malware delivery into one fast-moving chain.
- Teams conversations feel familiar and internal
- MFA becomes a step the victim is manipulated into completing
- Stolen credentials open the door to RDP and remote access tools
- Stagecomp and Darkcomp extend the intrusion into persistence and command execution
- Fake ransomware branding creates pressure while the real operation focuses on exfiltration
By the time the victim sees extortion language, the attacker may already have what they came for.
Where Xcitium Changes the Outcome
If you have Xcitium in place, this attack would NOT succeed the way the attacker needs.
- Cyber Awareness Education and Phishing Simulation reduce the first failure point by training users to challenge fake IT support requests, credential prompts, and MFA pressure tactics
- Identity Threat Detection and Response helps detect suspicious login behavior, risky remote access, and abnormal identity use before stolen credentials become persistent access
- Advanced EDR, powered by Xcitium’s patented Zero-Dwell platform, stops the malware stage when payloads attempt to run. Code can run without being able to cause damage
The attacker may start with a Teams message, but they do not get the chain reaction they need.
Defend the Human, Identity, and Execution Layers Together
MuddyWater proves that modern intrusions are not one-dimensional. They move from conversation to identity, from identity to endpoint, and from endpoint to data theft.
Train users before the prompt.
Detect identity abuse before access spreads.
Stop unknown code before it becomes impact.