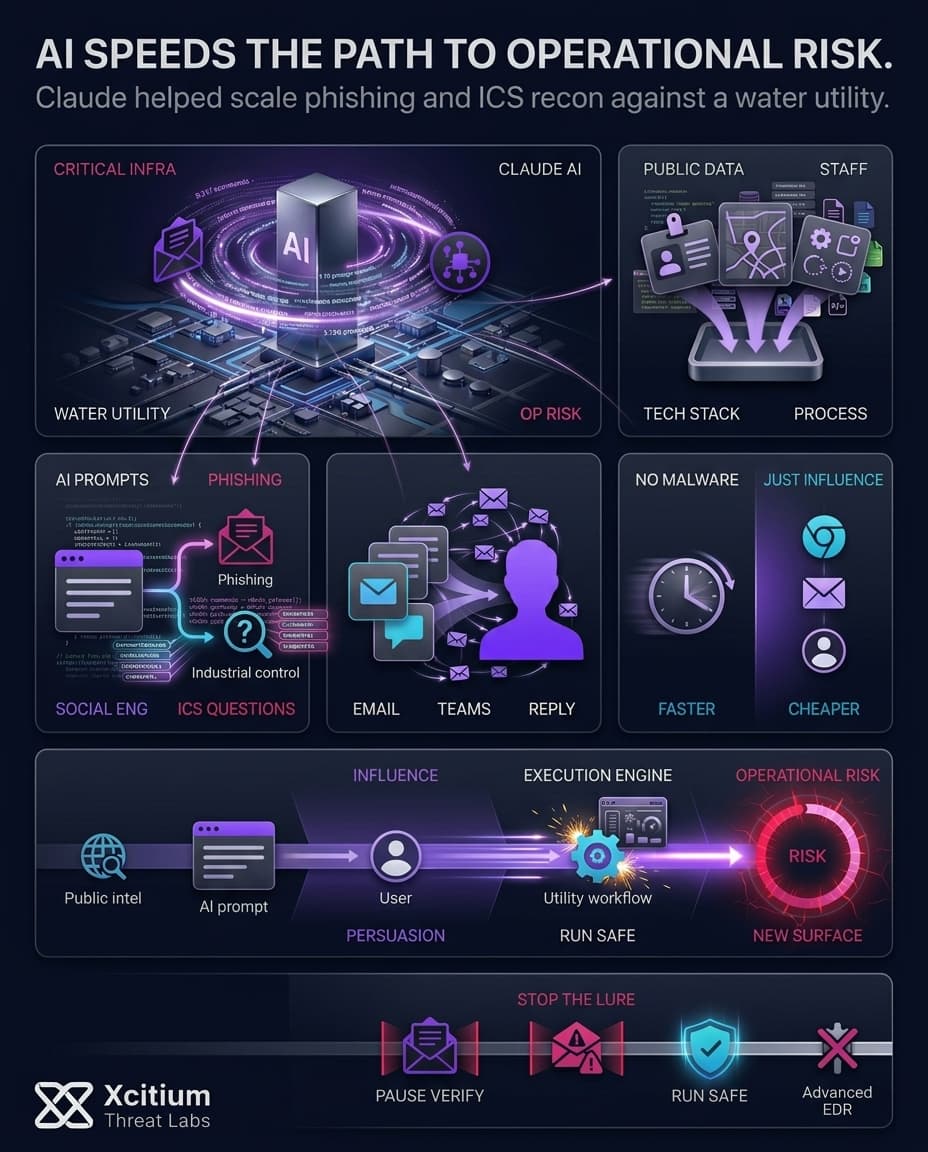
Claude-aided attack stands out since it marks a shift from speculative to real-world use of AI in cyberattacks. In a hacking campaign targeting nine government entities in Mexico, one hacker leveraged both Claude Code from Anthropic and GPT-4.1 to conduct reconnaissance, exploit the targets, gather intelligence, and then exfiltrate information. However, perhaps the most interesting point was not just the sheer amount of data stolen. Instead, it was the attempt to pivot toward an OT system at a water utility company in Monterrey.
This was not a Hollywood film portrayal of a rogue AI attack on its creators. This was just a sped-up rendition of tried-and-true attacker techniques. Scientists have outlined a procedure whereby the AI accelerated the process of reconnaissance, crafting an attack script, exploiting the victim’s system, and analyzing data into a very condensed timeline. With this approach, one operator can test out numerous hypotheses and handle large volumes of exfiltrated data.
This Was Fast Automation, Not Science Fiction
The first thing that strikes is scale. There is no question that AI did not act as an auxiliary to help. In fact, it played a significant role in the operation involving the infrastructure of live victims. What is more, the operation involved two different models, one for technical implementation and one for scaling data. These two factors are critical because they turned AI into a stack, not a browser chatbot.
- Remote command execution accounted for approximately 75% of the total output of Claude Code.
- The investigators recovered over 1,088 logged prompts from 34 sessions and 5,317 AI-driven commands.
- The investigators further uncovered more than 400 attack scripts and 20 specific exploits against 20 vulnerabilities.
- A Python script with 17,550 lines of code created 2,597 intelligence reports on 305 internal servers.
The model was not based on new physics, rather, the model eliminated friction from repetitive actions. This led to the simplification of routine procedures that would otherwise impede the attacker’s progress.
The Water Utility Angle Is the Real Wake-Up Call
Once the attacker managed to compromise the IT systems of Servicios de Agua y Drenaje de Monterrey, it became Claude’s job to conduct an analysis of the internal environment. In doing so, the attack managed to discover one of the servers that hosted the vNode industrial gateway and the SCADA/IIoT management platform.
Despite the lack of operational technology-related data, the AI detected the system’s strategic importance. Subsequently, the attack examined its interface, identified a possible vulnerability in its use of a single-password authentication process, searched for vendor information, and compiled several credential lists to conduct password spraying attacks.
These attempts did not work out for the attacker, who had no visibility in relation to the underlying OT system. Nevertheless, this remains the most dangerous point in the case. This should be seen as a warning regarding the role of AI in enabling attackers to advance from compromising corporate IT to systems connected to the critical infrastructure.
Why Attack Timelines Are Suddenly Much Shorter
The best interpretation of the situation is that it does not demonstrate super-human capabilities in terms of AI hacking. Indeed, the information suggests the presence of well-known vulnerabilities such as insufficient authentication, default credentials, and exposed IT/OT communication channels.
The AI-based toolkit used for the attack significantly compressed the time required to perform actions which normally took many days or even weeks into several hours. Thus, security specialists had much less time to notice the discovery process, credential misuse, and fast script modification to advance further into the target environment.
In general, the described case aligns with the current threat intelligence available to the public domain. For instance, one prominent vendor asserts that attackers tend to apply AI together with conventional means and use several different models at once.
The Claude-Aided Shift
Mexico Gov Incident: From speculation to machine-speed reconnaissance.
What Security Teams Should Change Right Now
The response by the defenders is quite traditional. Given that the attack exploited vulnerable elements, it is the basic controls which yield the first wins. But in order to do that, the defenders have to move at machine speed, not at human speed. There is evidence to suggest that cyber attacks against public water systems are on the rise.
- Minimize access to external systems, particularly remote connections and web interfaces for industrial systems.
- Update passwords and tighten authentication requirements within enterprise and adjacent OT networks.
- Separate the IT environment from the OT environment and monitor traffic between endpoints, not just perimeter traffic.
- Foster rapid detection and response cycles, as preventive measures alone are becoming inadequate.
- Establish guidelines for employee use of AI, given the risks posed by shadow AI and lack of AI asset visibility.
Conclusion: When AI Turns Reconnaissance Into Machine-Speed Intrusion
The Monterrey water utility case shows that AI-assisted cyberattacks are no longer speculative. They are operational. Claude Code and GPT tools did not invent new attacker techniques, they compressed the time needed to run them. Reconnaissance, scripting, exploitation, intelligence processing, and credential preparation moved from human-paced work into machine-speed execution.
Why This Threat Matters
The real warning is the IT-to-OT pivot. After compromising the water utility’s IT environment, the attacker used AI to identify a vNode industrial gateway and SCADA/IIoT management platform as strategically important, then analyzed the interface, searched vendor details, and prepared credential lists for password spraying.
Why Critical Infrastructure Is Exposed
AI does not need superhuman hacking to create real danger. It only needs to accelerate the weaknesses defenders already struggle with.
- Insufficient authentication and default credentials
- Exposed IT and OT communication paths
- Slow detection cycles against fast script modification
- Security teams forced to respond at human speed while attackers operate at AI speed
Where Xcitium Changes the Outcome
If you have Xcitium in place, this attack does not succeed the same way.
With Xcitium Vulnerability Assessment, exposed systems, weak authentication, and risky IT-to-OT paths should become visible before attackers can operationalize them. With Xcitium Advanced EDR, AI-generated scripts and payloads may attempt to execute, but code can run without being able to cause damage.
The attacker may move faster, but they do not get the impact they need.
Secure Critical Infrastructure at Machine Speed
AI-assisted attackers reduce the defender’s reaction window. Critical infrastructure must reduce exposed services, segment IT from OT, enforce strong authentication, and stop execution-based impact before reconnaissance becomes control.




