According to a recent FBI alert, U.S. banks saw an unprecedented increase in such attacks last year.
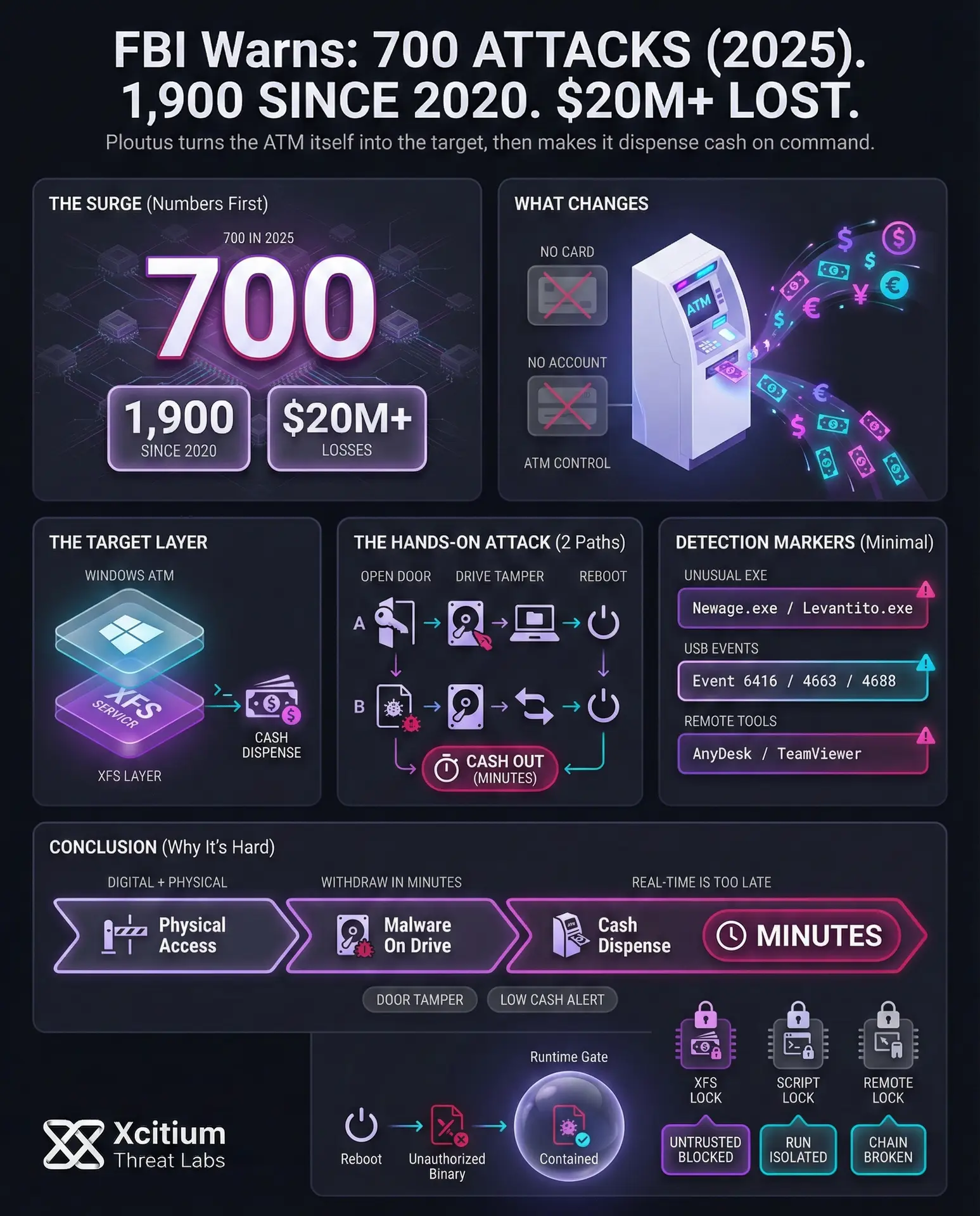
FBI noted that out of 1,900 ATM jackpotting incidents reported since 2020, over 700 occurred in 2025, resulting in more than $20 million in losses.
How Ploutus Malware Exploits ATMs
Ploutus targets the operating system of ATMs, which is based on Windows. It targets the XFS (eXtensions for Financial Services) service layer of ATMs, which controls cash dispensing functions. The attackers use unauthorized commands through XFS to carry out jackpotting attacks without any authorization from banks.
Hackers use Ploutus malware to take control of an ATM and then instruct it to spit cash without requiring a card or account. Once Ploutus infects an ATM, hackers get direct control over it and can withdraw cash from it almost instantly. Since jackpotting attacks involve ATMs’ hardware and not users’ accounts, hackers can withdraw cash from ATMs within a matter of minutes without any possibility of detection during the attack.
In reality, attackers use various methods to carry out jackpotting attacks on ATMs. In one such case, hackers broke into an ATM and opened its door through generic keys. After that, they tampered with the hard drive of the ATM. To carry out a jackpotting attack, hackers pulled out the hard drive of the ATM and used a laptop to copy Ploutus malware onto it. After that, hackers rebooted the ATM. Once rebooted, Ploutus malware started working on its own and allowed hackers to withdraw cash from it whenever they wanted.
In another case, hackers inserted a pre-loaded hard drive into an ATM containing Ploutus malware. After rebooting the ATM, it started working from the hard drive containing Ploutus malware. Once rebooted, hackers started withdrawing cash from it whenever they wanted. These are hands-on methods of carrying out jackpotting attacks on ATMs. These methods allow hackers to withdraw cash from ATMs within a matter of minutes. It becomes extremely difficult to detect such attacks in real time.
Case Study: Xcitium vs. Ploutus Malware
This demonstration highlights how Xcitium protects critical systems against advanced ATM malware using a prevention-first security model. In this test, live Ploutus samples are executed in a controlled environment to simulate a real-world jackpotting attack scenario targeting Windows-based ATM systems.
Rather than relying on signatures or post-execution detection, Xcitium’s ZeroDwell technology automatically classifies the Ploutus executables as untrusted at launch and runs them inside a secure isolation environment.
As a result, Ploutus is unable to interact with the XFS service layer, issue unauthorized cash-dispense commands, or manipulate system services. Even though the malware samples are fully functional, their attack logic never reaches the host operating system.
By removing the exposure window entirely, Xcitium keeps the system operational and uncompromised. This video demonstrates how specialized financial malware like Ploutus is neutralized instantly through continuous zero-trust execution and real-time isolation.
Key Indicators of Compromise (IOCs)
The FBI report lists specific indicators that a given ATM may be infected. Watch for unexpected files or behavior on the ATM’s Windows system. Notable IOCs include:
- Suspicious Executables: Unusual programs on the ATM hard drive such as Newage.exe, Color.exe, Levantaito.exe, WinMonitor.exe, Promo.exe, sdelete.exe, etc.. These filenames are not part of normal ATM software. Also look for copies of remote-admin tools like Anydesk1.exe or TeamViewer executables that should not be there.
- Known Malicious Hashes: Several MD5 hashes are associated with Ploutus variants (for example, 2C2D16658D8DA6B389934273EF8F8E22). Any matching files should be flagged and removed.
- Malicious Scripts and Files: Batch scripts and config files often appear on a compromised ATM. These include files like Restaurar.bat, Restauraropteva.bat, Logcontrol.txt, Logc.txt, and Borrar_beta.txt, as well as hidden files named C.dat. These scripts typically activate or restore the malicious code.
- Unauthorized Directories: Check for new folders or files in unusual locations. For example, attacker-created directories such as
C:<ATM_Manufacturer>...orC:UsersSSAuto1AppDataLocalPhave been observed. These paths often host the malware payload. - Remote Access Software: Any presence of remote-login applications on an ATM (e.g. TeamViewer, AnyDesk) is suspicious unless explicitly approved. Also check for logs of unexpected incoming connections or logins from outside IP addresses these can indicate a hacker is accessing the machine remotely.
- USB Insertion Events: Because attackers often use USB drives, watch the Windows security logs. Enabling “Audit Removable Storage” will log Event ID 6416 whenever a USB device is plugged in. Repeated or unrecognized USB insertion events on an ATM (especially outside of scheduled maintenance) are red flags. Similarly, enabling Object Access auditing can trigger Event ID 4663 for file modifications.
- Physical Alarm Triggers: Don’t ignore ATM self-monitoring. Alarms or tamper sensors that indicate the door was opened or the cash drawer was accessed at odd times are an important sign of intrusion. Likewise, if an ATM suddenly reports “low cash” with no valid reason, it may have been emptied by criminals.
Ploutus Malware SHA-1 Samples & Zero‑Dwell Threat Intelligence Reports
Mitigation and Best Practices
The FBI’s advisory emphasizes a multi-layered defense combining physical controls, strong monitoring, and secure configurations. Some key recommendations are:
- Physical Security: Upgrade the ATM lock and install alarmed access panels. Consider vibration or door sensors and cabinets with internal barriers. Security cameras must provide complete coverage of the ATM area and store images for analysis.
- Hardware Security Controls: Configure the ATM to shut down in the event of indicators of intrusion detection. Implement whitelisting of approved hardware to prevent the connection of unauthorized USB storage devices. Implement TPM and firmware security and full-disk encryption to prevent boot kits and offline installation of malware. Activate Windows memory integrity for enhanced security.
- Logging and Monitoring: Activate Windows auditing for USB device connections, file access, and process creation (Event IDs 6416, 4663, 4688). Consider consolidating logs and retaining them for extended periods for incident response.
- Software Security Controls: Implement application whitelisting to prevent execution of unauthorized applications. Keep anti-malware software updated. Consider having a gold image of the operating system and treating file changes as a potential compromise.
- Operational Practices: Update default credentials and regularly inspect the ATM for security issues. Closely monitor the schedule for maintenance and access of the ATM. Share threat intelligence and educate personnel on indicators of jackpotting attacks.
By combining these defenses, banks can dramatically reduce their risk. For example, even if an attacker gets inside the ATM, a proper audit policy would log the breach (via Event ID 6416, 4663, 4688, etc.) and an automated shutdown could prevent cash dispensing before it occurs.
Physical locks and cameras can catch intruders in the act, and strong log monitoring can reveal the telltale chain of events that precede a jackpotting attempt.
Conclusion: When Malware Makes the ATM Dispense Cash on Command
Ploutus driven jackpotting is not an account fraud problem, it is a direct compromise of the ATM itself. The FBI reports more than 700 jackpotting incidents in 2025 out of 1,900 reported since 2020, with losses exceeding $20 million. Once Ploutus is on the ATM, attackers can issue XFS commands to dispense cash without a card or account.
Why This Threat Is So Hard to Stop
This is a hybrid attack, digital control plus physical access.
Attackers can break into the ATM, copy malware onto the drive, reboot the machine, then withdraw cash within minutes. In some cases they simply swap in a pre-loaded drive. That speed makes real-time detection difficult during the actual withdrawal window.
What Defenders Should Watch For
The FBI guidance points to clear forensic and operational signals, including unusual executables like Newage.exe or Levantaito.exe, remote admin tools like AnyDesk or TeamViewer, suspicious batch scripts, and audit events tied to removable storage and file modification. Hardware tamper signals and irregular low cash alerts outside maintenance windows are also strong indicators.
Where Xcitium Changes the Outcome
If you have Xcitium deployed on ATM Windows systems, this attack would NOT succeed as a jackpotting event.
With Xcitium Advanced EDR in place, unauthorized binaries and scripts can be stopped at execution. Code can run without being able to cause damage. That breaks the chain that turns a reboot into cash-out control.
Protect the Machine, Not Only the Money
Jackpotting is won before the cash is dispensed. Harden physical access, restrict removable media, monitor tamper telemetry, and block untrusted execution so Ploutus never becomes operational.