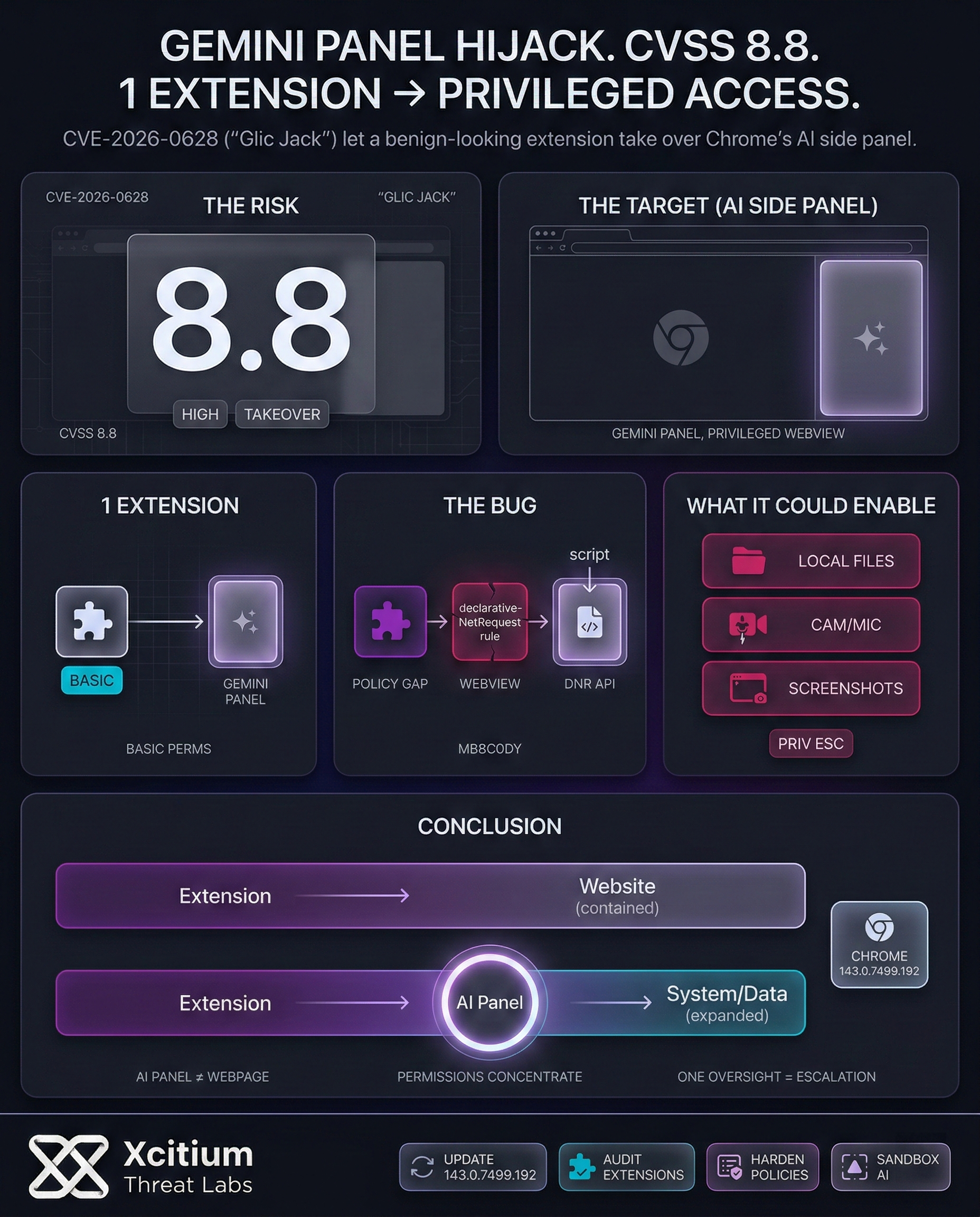
In this ever-changing landscape of cyber security, the inclusion of artificial intelligence in our web browsers presents us with a host of unforeseen risks and opportunities. As such, the recent fix for a critical vulnerability in Google’s popular web browser, Google Chrome, identified as CVE-2026-0628, represents an interesting case study. This vulnerability was found to have the potential to enable a malicious browser extension to take over control of the new AI side panel in Google Chrome, thereby creating a host of security-related problems.
The flaw, codenamed “Glic Jack,” carried a high CVSS score of 8.8, highlighting its potential for severe impact. For example, had it been exploited, an attacker who convinced a user to install a seemingly benign extension could have gained alarming capabilities. This is a serious concern for all Chrome users.
How a Simple Extension Could Seize Control
At the heart of the vulnerability was a small mistake in Chrome’s design. In particular, the problem was one of “insufficient policy enforcement” for the browser’s component named WebView, which was utilized by the Gemini panel. Indeed, the latest browsers employ a variety of application programming interfaces (APIs) to regulate the capabilities and prohibitions for browser extensions. In the present situation, the browser extension declarativeNetRequest API, which is normally utilized by browser extensions such as ad blockers to monitor web communications, was not correctly restricted from interacting with the Gemini panel.
This small oversight had major consequences. This oversight allowed the extension with basic permissions to inject malicious JavaScript code directly into the Gemini panel. While the extension affecting a normal website is expected behavior, affecting a core and privileged browser component such as the Gemini panel is a major security flaw. This is an important point in understanding the severity of this vulnerability. This also relates to the difficulties in integrating powerful AI tools into the browser environment.
The Real-World Impact: From File Access to Surveillance
This exploit of CVE-2026-0628 would not have been a minor inconvenience, however, because the Gemini panel, by the nature of being a powerful AI assistant, has access to a plethora of sensitive user information and system functionality. Thus, by hijacking this panel, the extension could have gained the powerful permissions that the panel has access to. The potential consequences of this are far-reaching and include:
- Local File Access: The ability to read files directly from the user’s computer.
- Surveillance: Unauthorized access to the user’s camera and microphone.
- Data Theft: Taking screenshots of any open website, potentially capturing sensitive information like passwords or financial details.
- Privilege Escalation: Transforming a low-permission extension into a powerful spying tool.
This scenario underscores the danger of AI-powered features becoming a double-edged sword. The very capabilities that make them useful access to content, system functions, and user data also make them a prime target for attackers. Consequently, securing these features is of paramount importance.
Hijacking the Gemini Panel
This exploit of CVE-2026-0628 is far from a minor inconvenience. Because powerful AI assistants have deep access to system functionality, hijacking this panel grants an attacker far-reaching permissions.
Consequences of Privilege Escalation
Local File Access
The ability to read sensitive files directly from the user’s computer system.
Surveillance
Unauthorized access to the user’s camera and microphone for spying.
Data Theft
Taking screenshots of open websites, capturing passwords or financial details.
Privilege Escalation
Converting a low-permission extension into a powerful espionage tool.
The Double-Edged Sword
The very capabilities that make AI useful—access to content and system functions—also make them a prime target for attackers. Securing these features is not optional; it is of paramount importance.
[THREAT_LEVEL]: CRITICAL_FAIL
Google’s Swift Response and the Future of Browser AI
Fortunately, Google addressed this vulnerability with great alacrity, and the patch was released in early January 2026, with the new version of Chrome, version 143.0.7499.192. This ensures that the vulnerability does not end up being used in the wild. This situation, however, presents a great learning experience for the industry. As browser feature sets become more “agentic,” with AI assistants capable of executing complex multi-step tasks, the attack surface is bound to expand.
This event brings classic browser security risks, such as Cross-Site Scripting (XSS) and privilege escalation, into the new context of AI. Developers must, therefore, be incredibly diligent in ensuring that these powerful new components are properly sandboxed and that their interactions with other parts of the browser are strictly controlled. The “Glic Jack” vulnerability demonstrates that even a small oversight in policy enforcement can dismantle the security model that users rely on to keep them safe online. In addition, it emphasizes the need for continuous security research and responsible disclosure to identify and fix such flaws before they can be abused.
Conclusion: Browser AI Turns One Extension into a Privileged Attack Surface
CVE-2026-0628 shows why AI inside the browser changes everything. A simple policy enforcement mistake in the Gemini panel WebView allowed a low-permission extension to inject JavaScript into a privileged component. What would normally be a minor extension risk could have escalated into control of an AI interface with access to sensitive system capabilities.
Why This Threat Matters
The Gemini panel is not a normal webpage. It is an AI assistant embedded into the browser, and that makes it a high value target.
- A basic extension could have gained access to local files, screenshots, and even camera and microphone paths through the panel’s privileges
- AI features concentrate permissions, context, and user data in one place
- Small browser policy oversights can become large privilege escalation events
Why This Is a Structural Shift
For decades, malicious intent needed a carrier, attackers had to ship code and defenders could scan artifacts. Browser AI changes the model. The execution engine is already installed, and the attacker can influence behavior by hijacking the agent layer through an extension. The malicious logic becomes a sequence of actions performed through legitimate APIs. You cannot scan a thought.
What To Do Next
Google patched the issue in Chrome 143.0.7499.192. Apply updates fleet-wide, audit extension policies, and treat browser AI components like privileged infrastructure. As browsers become more agentic, the control point is architecture and sandboxing, not trust in the UI.