Why This Campaign Matters Beyond the Headlines
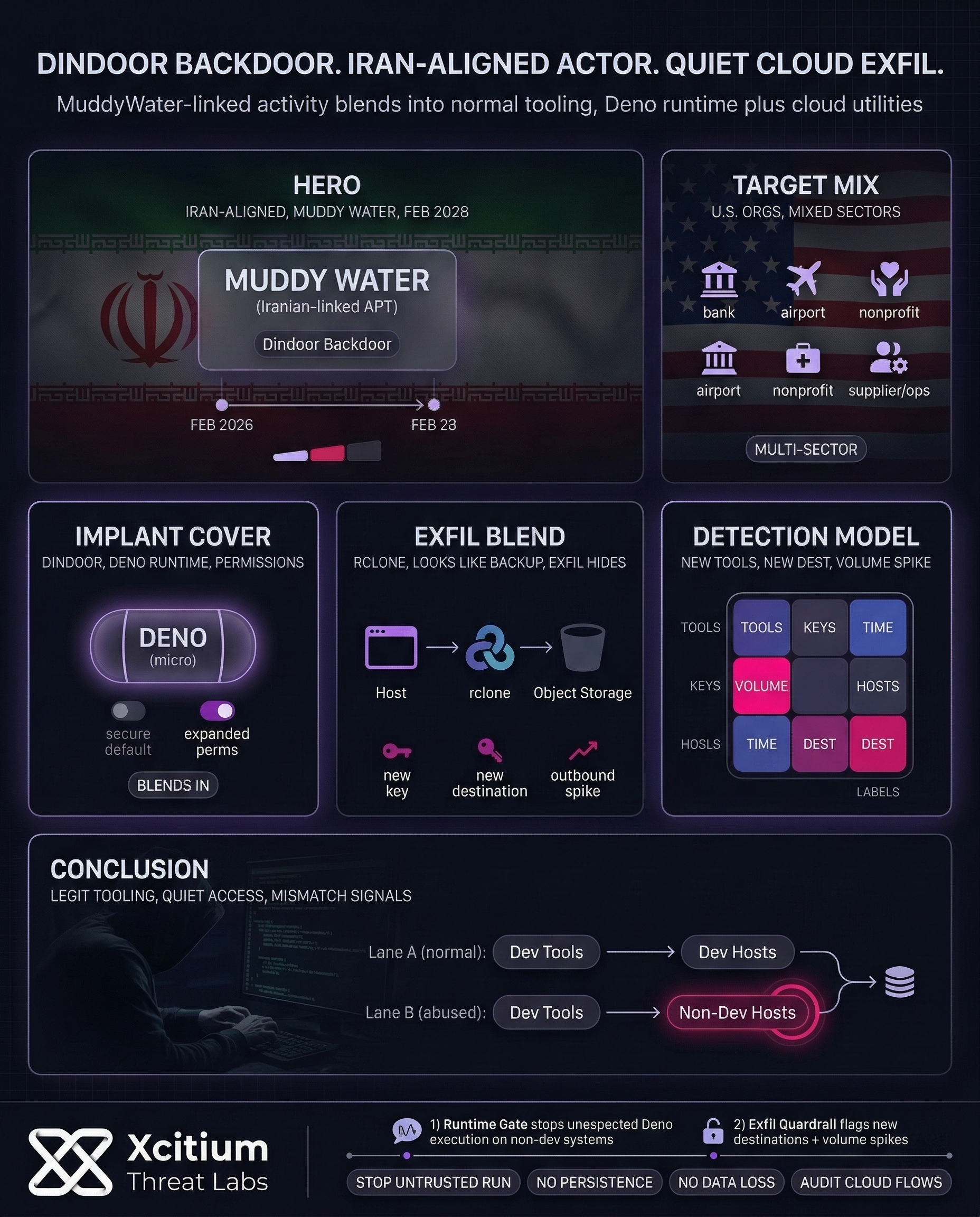
Recent reporting links the Iran-aligned group MuddyWater to intrusions across several organizations in the United States. Targets include a bank, an airport, nonprofits, and the operations of a U.S. software supplier in Israel. Importantly, investigators say the activity began in early February 2026. That timing suggests pre-positioning quiet access gained before pressure peaks.
Geopolitical tension makes that access more concerning. A bulletin from the Canadian Centre for Cyber Security assessed that Iran is very likely to use cyber operations after the Feb. 28, 2026 U.S. Israel strikes. It specifically warned about critical-infrastructure attacks and information operations. Therefore, even “espionage-looking” access can become leverage fast.
Dindoor Explained: Why a Deno-Based Backdoor Stands Out
The investigators called the implant “Dindoor” because it uses Deno, a JavaScript and TypeScript environment that is “secure by default” and uses permissions. In some cases, the environment may appear legitimate from the perspective of an attacker. The attackers, however, could run the environment using lax permissions. Thus, the investigators must consider the context, not just the name of the process.
A second backdoor, called “Fakeset,” was also identified in the victim environments. Although the initial vector for the backdoor has not been publicly disclosed, the variety of backdoors indicates that the attackers are flexible in their operation. Another piece of publicly disclosed information is that the attackers reuse the same certificates for their malware.
Cloud Tools in the Middle: How Data Theft Can Blend In
It has been noted that an attempt to transfer data using rclone to an object storage bucket. rclone is used by many teams to perform backups. Thus, it is not necessarily malicious on its own. However, unusual destination buckets, new access keys, or sudden spikes in outbound traffic can indicate malicious activity.
Also it’s suggested that since most organizations cannot prevent cloud storage services, better guardrails are needed. For instance, detecting new tools, new external endpoints, and high volume transfers. This is in line with the U.S. recommendations regarding exposed systems during times of tension.
The Bigger Pattern: Repeatable Access Over Movie Hacker Tricks
As can be seen from long-running threat tracking by MITRE’s ATT&CK platform, MuddyWater has been around at least since 2017. Additionally, they have been flagged as being associated with the Ministry of Intelligence and Security. Thus, defenders should be prepared for patience, focus on credentials, and persistence rather than “tricks.”
As can be seen from the conflict-related activity tracking, researchers have identified spikes in the attempts to access internet cameras using well-known vulnerabilities. Though not necessarily indicative of Dindoor activity, the situation does highlight a simple model for assessing risk: everything exposed is at risk in a conflict situation. Thus, the lack of inventories and patching cycles can be a problem.
Practical Security Moves That Fit This Threat
Because investigators have not publicly confirmed the initial intrusion method, it’s smart to prioritize controls that shrink multiple attack paths:
- Secure internet-facing systems and expedite patching for edge devices and remote access gateways.
- Use strong, distinct passwords and move high-risk access to phishing-resistant MFA.
- Detect unexpected Deno or Python code execution on systems where these tools shouldn’t be running.
- Detect use of rclone, new cloud destinations, and large outbound data transfers.
- Have offline backups ready and test recovery in case activity becomes destructive.
Conclusion: When “Secure by Default” Tooling Becomes the Cover
The Dindoor campaign shows how modern intrusions hide inside legitimate developer and cloud workflows. A Deno-based backdoor can look normal in the wrong environment, and cloud utilities like rclone can make data theft blend into routine backup activity. The reported activity beginning in early February 2026 also signals pre-positioning, quiet access established before pressure peaks.
Why This Matters Beyond One Implant
Geopolitical tension turns access into leverage. Even intrusion activity that looks like espionage can pivot quickly into disruption when conditions change. Everything internet-facing becomes higher risk during conflict, especially when inventories and patch cycles lag.
Why Organizations Are Exposed
This campaign succeeds by exploiting normal enterprise reality:
- Legitimate runtimes can run with permissive settings, context matters more than process names
- Trusted cloud tools and storage providers are hard to block, so exfiltration can hide in plain sight
- New destinations, new keys, and sudden outbound volume are often missed until after the transfer
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
- Xcitium Advanced EDR stops untrusted execution paths at runtime, even when adversaries abuse developer tooling. Code can run without being able to cause damage.
- This blocks the attacker’s ability to turn Deno execution into persistence, and to turn cloud transfer tooling into real data loss.
Reduce the Room for Quiet Access
Treat unexpected developer runtimes as high-risk on non-development systems. Validate cloud endpoints and transfer volumes, tighten remote access, enforce phishing-resistant MFA, and prepare recovery paths in case activity turns destructive.