What the FBI is Warning About and Who Gets Targeted
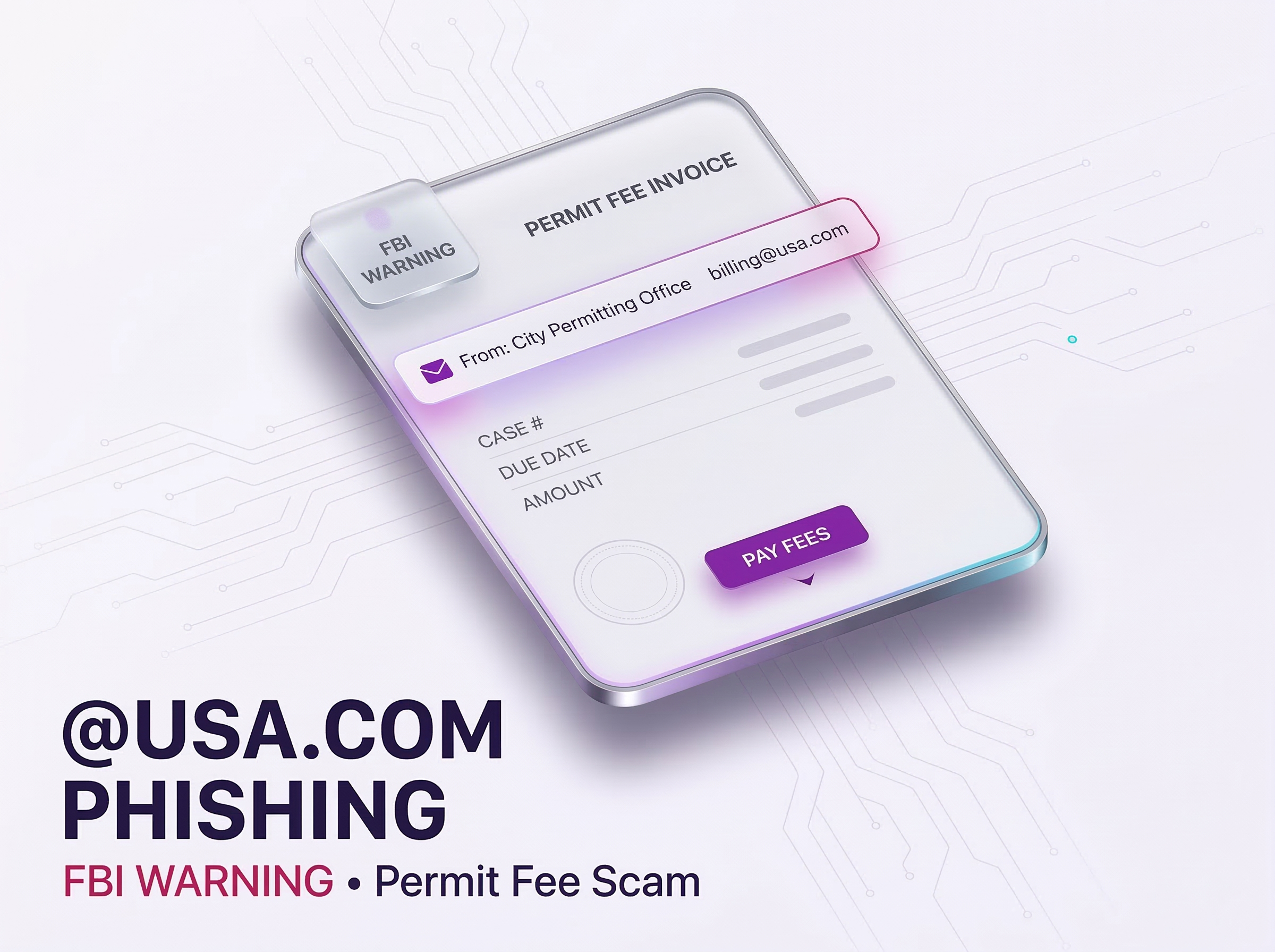
Recently, the Federal Bureau of Investigation warned about a phishing scheme tied to planning, zoning, and land-use permits in the United States. Criminals target individuals and businesses with active permit applications.
Unlike generic spam, these emails arrive when an applicant expects updates. Therefore, the message feels relevant, and some recipients respond quickly. Attackers then push payment through wire transfer, peer-to-peer apps, or cryptocurrency using fake invoices. The FBI says it has identified victims nationwide.
Why Public Permit Information Becomes a Perfect Phishing Ingredient
Permit workflows mix transparency with urgency. Applicants often see case numbers, addresses, hearing dates, and staff names in normal communications. Meanwhile, delays can stall work and raise costs.
The FBI says attackers harvest publicly available permit data to “blend in.” As a result, a phishing email can cite the correct address or application number. Consequently, the message seems legitimate even when the sender is not.
Process of Permit Fee Phishing Scam
Most often, criminals send an email to the victim, impersonating planning and zoning officials. The timing of this is usually around the same time as communication from the local office.
Some of the signs of this scam, as identified by the FBI, are:
- Professional appearance and content, which is similar to legitimate government communication and includes actual processes and ordinances.
- Use of sender email addresses similar to those used by government departments but with non-government domains and domains similar to those of government departments.
- Use of PDF invoices with “fees” and details of these “fees,” and instructing victims to ask for payment details via email rather than phone.
Another tactic is to use urgency. For example, a contractor might receive an email with details of their correct address and case number. The next step is to send an email stating that failing to make payment will cause delays. The FBI also points out that the scam often comes from non-government domains that look legitimate at first glance, including “@usa.com.”
Another detail is the control of communication channels. The FBI identifies this as another tactic used by scammers. For example, there are instances where the invoice includes details of emailing them instead of contacting them via phone to ask for payment details. This means that scammers maintain control of communication via email and do not allow victims to call them via phone numbers found on public websites. This means that there is no “sanity check” as victims are only able to communicate via email.
The Bigger Picture: Phishing and Impersonation Continue to Grow
This permit fee scam is part of an increased trend in cyber-enabled fraud. According to the FBI’s latest IC3 report, phishing and spoofing are still the most reported cybercrime in America, with 193,407 complaints in 2024.
Total cybercrime losses have also increased significantly. The FBI reported over 859,000 complaints and $16.6 billion in reported losses in 2024, marking a 33% increase from 2023 and a new record high in reported losses related to internet fraud.
Impersonation scams are still proving costly. The reported losses related to government impersonation scams amount to around $405.6 million, although it is believed many of these scams have also involved payment methods such as cryptocurrency, wire transfers, and peer-to-peer payment systems. These are often requested in fraud schemes, including permit fee phishing scams.
Practical Defenses for Applicants and Local Governments
Individuals and businesses should follow process discipline. If they are sent an unexpected permit fee notification, they should assume it is fraudulent.
Quick checklist:
- Check the sender’s domain, not just the name.
- Contact the office using the contact information on the official government website.
- Make payments only through the official portal or your regular billing process.
- Do not act on requests for wire transfers, peer-to-peer transfers, or cryptocurrencies.
If they have already clicked on something, replied to the message, or made payments, they should save the message and attachments, contact their bank, and file a complaint with the Internet Crime Complaint Center.
Individual local governments can also prevent these scams. CISA has recommended using SPF, DKIM, and DMARC for better email authentication. NIST has also included these as measures for detecting and reporting spoofing.
Another measure is operational clarity. CISA has recommended local governments to establish official channels for communications and reporting. If the official payment channel is clear, applicants will not fall for these scams.
Conclusion: When Public Records Become a Fraud Engine
This permit fee scam shows how attackers exploit a uniquely dangerous combination, public transparency and real-world urgency. By harvesting publicly available permit details, scammers can send high-fidelity emails that cite the correct address, case number, and timeline, then pressure victims into paying fake fees through irreversible methods like wire transfers, peer-to-peer apps, or cryptocurrency.
Why This Threat Hits So Many Victims
This is contextual phishing, timed to moments when applicants expect updates and cannot afford delays.
- Messages mimic legitimate government communication and ordinances
- Sender domains look close to official addresses, but are not government domains
- PDFs and invoices push victims to request payment details by email, not by phone
- Urgency is used to prevent a simple verification call
The FBI’s IC3 data reinforces the scale behind this pattern. In 2024, phishing and spoofing remained the most reported cybercrime category with 193,407 complaints, and total reported losses reached $16.6 billion.
Where Xcitium Changes the Outcome
With Xcitium in place, this attack would NOT succeed.
- Xcitium Cyber Awareness Education and Phishing Simulation conditions applicants and staff to verify the sender domain, distrust payment urgency, and validate fees through official portals and published phone numbers.
- If a click happens, faster reporting and stronger decision discipline reduce the chance that a message turns into a payment event.
The attacker loses at the decision point, because the payment workflow is verified through an independent channel.
Stop the Payment Before It Leaves the Bank
These scams succeed because victims act fast and pay outside normal processes. Slow the workflow down, verify through official sites, and train teams to treat unexpected fees as fraud by default.