Why VoidStealer and the Chrome Master Key Matter Now
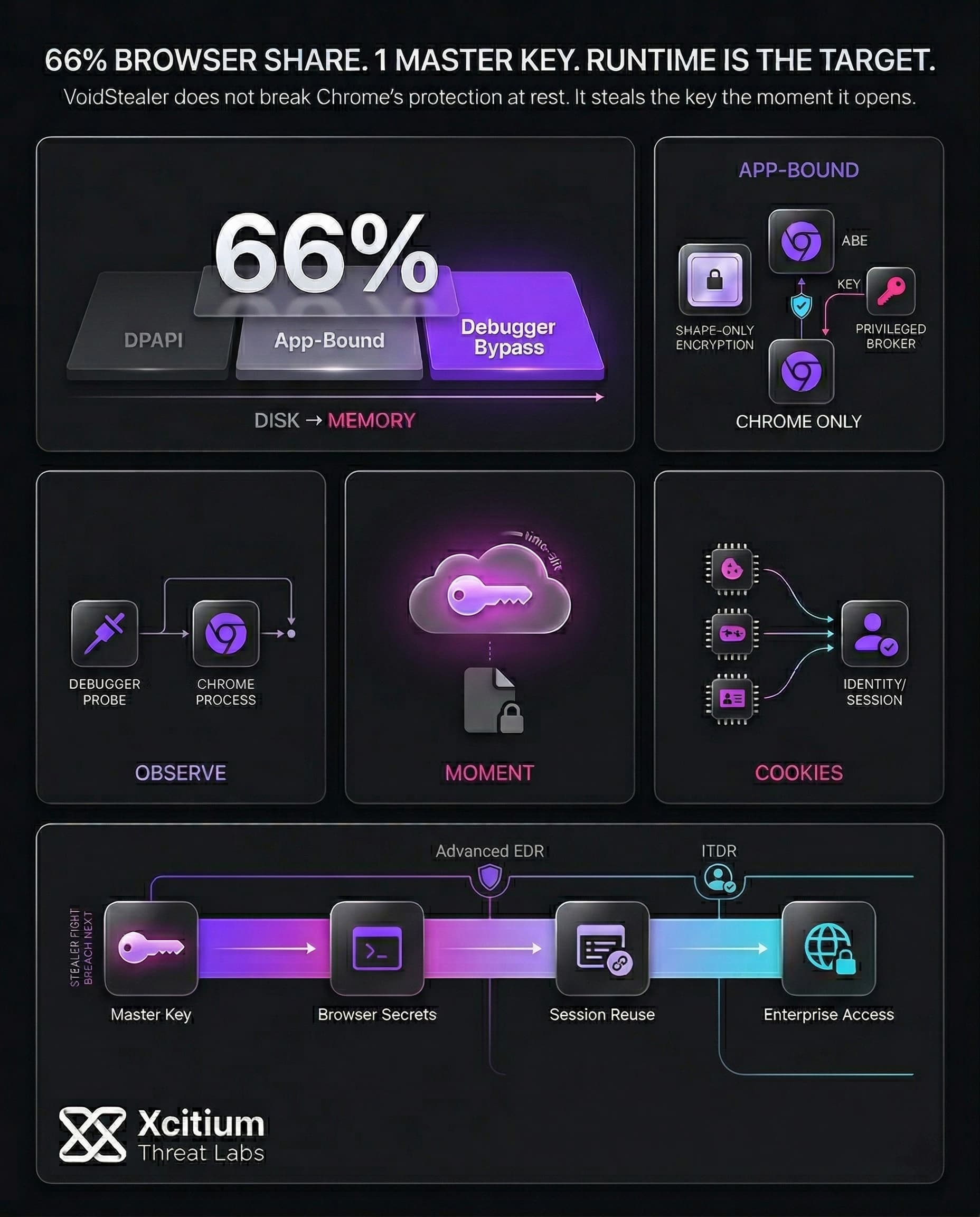
VoidStealer is just one of a rising tide of “information stealers” designed to steal whatever is useful to cybercriminals for quick login. Rather than trying to break sophisticated encryption, many stealers focus on a more accessible target: the browser master key, which unlocks the secrets of the browser. Once thieves have the master key, they can break the encryption on cookies, saved passwords, and other encrypted information on the same machine.
What makes this case unusual is the approach. VoidStealer uses a debugger approach to steal the more recent Chrome master key, which is used in Application-Bound Encryption. This means it can avoid the more obvious methods that defenders might anticipate, like escalating privileges or code injection.
This is important because of the browser itself. Chrome has a commanding lead in global browser use, and even a small weakness can have a disproportionate impact. The latest global browser usage share statistics show Chrome at two-thirds of the total.
What Application‑Bound Encryption Was Designed to Stop
Before Chrome’s newer protections, Windows browser data relied heavily on Windows’ Data Protection API (DPAPI). DPAPI is convenient for developers because Windows can encrypt and decrypt data using keys derived from the user’s sign-in context. However, that model has a gap: anything running as the same logged-in user can often access decryption capabilities.
To raise the cost for attackers, Chrome introduced Application‑Bound Encryption on Windows. In simple terms, it attempts to “bind” protected browser data to Chrome’s application identity, not just the user account. It does this with a privileged Windows service that verifies the requesting app during decryption. Consequently, basic “run as user and decrypt” theft becomes harder.
Google also positioned the change as a visibility win. If malware needs elevation or injection, defenders gain clearer signals to hunt. Additionally, Chrome can emit events when verification fails, which helps enterprises detect suspicious decryption activity.
The Debugger Trick That Changes the Game
VoidStealer’s strategy is based on an important aspect of encryption systems: at some point in time, a key needs to be in memory in a usable form. Instead of attempting to recover keys from disk storage, according to reports, VoidStealer observes the browser in use and captures the key during a brief period when it is in “plaintext in memory.”
The important change in this strategy is in its observation. Instead of code injection into the browser process, this strategy attaches to the browser process as a debugger and uses hardware breakpoints to monitor the process. At the appropriate point in execution, it reads the key directly from process memory. This strategy avoids some of the “tamper” characteristics that are associated with code injection.
The advantage in stealth is important. Application-Bound Encryption was intended to put attackers into more “noisy” behaviors. If an attacker can “observe and copy” at an appropriate point in time, what constitutes “suspicious” activity in an endpoint environment may need to be reassessed.
Runtime Decryption Interception
VoidStealer targets Chromium’s OSCrypt App-Bound Encryption (ABE) execution path, specifically the runtime invocation of os_crypt::DecryptAppBoundString(...). This processes encrypted key material (stored in the Local State file) and outputs a plaintext AES key used to decrypt cookies, credentials, and tokens. The malware attaches to the chrome.exe process via DebugActiveProcess / NtDebugActiveProcess, enabling full inspection of execution context.
Then sets hardware breakpoints (DR0–DR3) on instructions related with the decryption routine or its return path. When the breakpoint triggers, the malware stops execution and extracts the decrypted key from memory regions referenced by function arguments or return buffers (e.g., stack/heap-backed std::string decrypted_key_string). This eliminates the need to replicate DPAPI or ABE logic. Instead, it passively captures the key post-decryption, leveraging Chrome’s trusted execution to perform the cryptographic operation.
ABE Architecture Abuse (Privilege Boundary Bypass)
Chrome’s ABE implementation shows a privileged broker model where decryption operations are mediated by elevation_service.exe running as NT AUTHORITY\SYSTEM. The workflow enforces application identity validation before returning decrypted material:
- Encrypted data stored on disk (AES key wrapped via DPAPI + ABE)
chrome.exe(user context) requests decryptionelevation_service.exevalidates caller identity (Chrome-only restriction)- Decrypted key returned to Chrome process memory
This model prevents:
- Direct file decryption (data remains encrypted at rest)
- Unauthorized service access (non-Chrome processes rejected)
- Offline DPAPI key extraction without context
VoidStealer does not attempt to bypass these controls directly. Instead, it operates within the trusted execution window:
- Hooks execution after
elevation_service.exereturns decrypted material - Observes memory state inside
chrome.exepost-validation - Reads plaintext key from process memory before re-encryption or usage completion
By avoiding service impersonation, token theft, or injection into SYSTEM processes, the malware maintains a non-elevated footprint while still accessing high-value cryptographic material. The attack effectively converts ABE from a boundary-enforced model into a time-of-use exposure problem, where the decrypted key becomes accessible during a narrow execution window.
Real-World Impact From Stolen Cookies to Larger Compromise
The concept of a hijacked browser master key is not just limited to saved passwords. Cookies for a session may be even more desirable to attackers, as they may be used to potentially circumvent login requirements.
Infostealers are connected to other attacks. Industry reports have revealed that there’s a pattern to infostealer attacks. Attackers obtain cookies and credentials, sell them, and use the resulting initial access to compromise an environment. An infostealer infection may be the starting point of an attack, not the end.
The use of abused credentials highlights the severity of this issue:
- This type of attack is one of the top initial attack vectors used during a breach.
- Infostealer logs may show corporate credentials on an unmanaged device, which may complicate an attack.
Crime statistics show the severity of online fraud and account compromise. The IC3 receives hundreds of thousands of complaints from the public, resulting in significant financial loss.
Defense Playbook that Reduces Exposure and Improves Detection
- Prefer a password manager over browser password storage, particularly on shared or lightly managed devices. This helps minimize the impact of a single browser profile compromise.
- Implement device management on devices accessing corporate apps. Even small BYOD exceptions create credential bridges.
- Phishing-resistant MFA is a good practice, and it should be paired with CA. However, session theft is a separate risk.
Then, improve detection for modern stealers:
- Unusual debugging relationships: One process attached to a browser process as a debugger is usually unusual outside developer tool usage.
- Suspicious memory access patterns with browser processes, especially when there are repeated reads that do not align with standard accessibility patterns or enterprise tool usage.
- In enterprise Windows logs, Chrome-related signals with verification failures and unexpected decryption attempts related to Application-Bound Encryption.
Finally, plan your response as if an infostealer equals compromised identity. Reset sessions, rotate credentials, and review sign-ins. Otherwise, attackers can reuse what they already stole, even after you remove the malware.
Conclusion: When the Key Stays Encrypted, Attackers Go After the Moment It Opens
VoidStealer shows how modern infostealers are adapting to stronger browser protections. Instead of trying to break Chrome’s Application-Bound Encryption directly, it waits for the exact moment the master key appears in memory, then steals it through debugger-based observation. The protection is still there, but the battlefield has moved from storage to runtime.
Why This Threat Matters
This is not just about passwords. Once the browser master key is exposed, attackers can move far beyond saved credentials.
- Cookies, tokens, and other encrypted browser secrets become accessible on the same machine.
- The technique avoids louder behaviors like privilege escalation or code injection, reducing obvious detection signals.
- Chrome’s scale magnifies the risk, with roughly two thirds of global browser usage concentrated in one platform.
Why Organizations Stay Exposed
This attack reflects a broader infostealer pattern. Malware steals browser secrets, criminals reuse or sell them, and the real breach begins afterward.
- Stolen cookies can bypass normal login friction and session boundaries.
- Infostealer infections often become the starting point for larger compromise, not the end state.
- Even unmanaged or lightly managed devices can become bridges into corporate identity systems.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed the way criminals need.
- Xcitium Advanced EDR helps break the execution chain before infostealers can turn runtime observation into large-scale credential and cookie theft.
- Xcitium ITDR helps stop the second stage, detecting abnormal identity behavior, risky session use, and follow-on access attempts after browser secrets are exposed.
The attacker may target the browser, but they still need execution and identity reuse to win.
Treat Browser Secret Theft as Identity Compromise
Application-Bound Encryption raised the bar, but VoidStealer shows the bar is now at runtime. Reduce browser-stored secrets, strengthen device management, use phishing-resistant MFA, and respond to infostealer activity as compromised identity from the start.