A confirmed European Commission data breach linked to the Europa.eu web platform has put a spotlight on a modern reality: even “public-facing” systems can sit on top of complex cloud storage that may contain sensitive information. While the Commission says internal systems were not affected, it also acknowledges that data was taken and that the full impact remains under investigation.
What The Commission Confirmed About The Europa Web Platform Incident
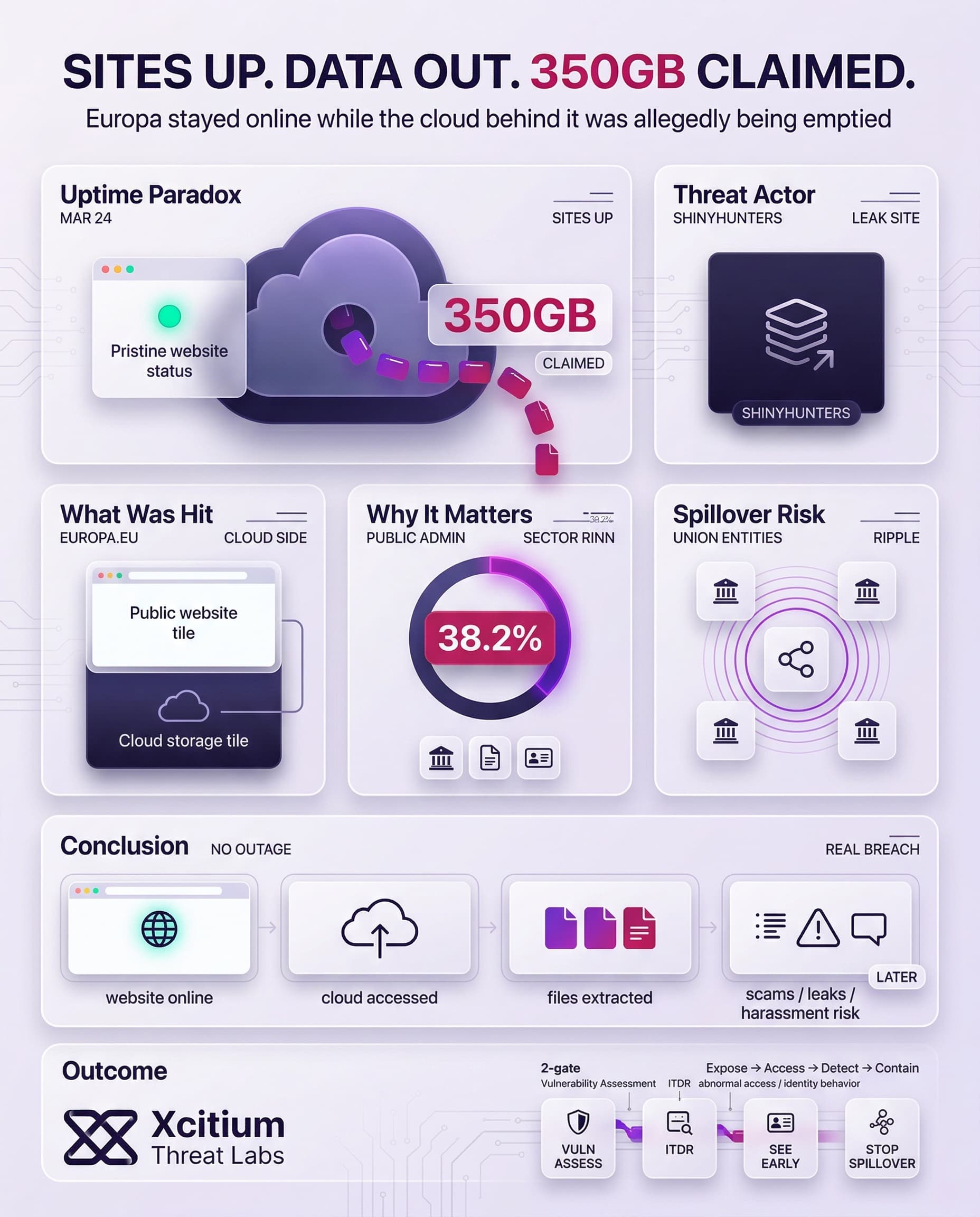
In its official communication, the European Commission said it discovered a cyberattack on March 24 that affected cloud infrastructure hosting its web presence on the Europa.eu platform. Europa websites stayed available during the incident. Even so, early findings indicated that data was taken, and the Commission said it is notifying Union entities that could be affected while the investigation continues.
Several things are already clear from the Commission’s statement and other supporting reports:
- It’s not the Commission’s infrastructure but rather the infrastructure related to the Europa web platform that has been targeted in the cyber attack.
- Even though evidence of data theft is present, the status of the websites remains unaltered.
- Notification of potentially affected institutions in the European Union is still in the process of being done.
Claims Versus Confirmed Facts About The Stolen Data
Although the Commission has not publicly detailed what data was accessed, reporting indicates that the intrusion was claimed by the group ShinyHunters. The attacker’s claim of more than 350 GB stolen, alongside screenshots presented as proof of access to information linked to Commission employees and an email server used by staff.
The group published an entry on its leak site and released a large archive of files alleged to come from the compromised cloud environment.
Why a “Public Website” Breach Can Still Create Serious Exposure
This case highlights a different risk, web platforms often rely on cloud storage that can contain far more than web pages. Even when visitors see no disruption, behind-the-scenes systems may store content repositories, uploaded documents, user or staff contact records, configuration files, and operational logs that help run the platform.
The Commission’s choice to notify other Union entities signals potential spillover beyond a single team or website. The incident becomes a governance issue as much as a technical one.
The Commission says sites remained available, yet it also indicates investigators believe data was taken. Therefore, the lack of downtime does not reduce the seriousness of a confirmed breach especially when stolen information could surface later in leaks, scams, or targeted harassment.
Public Administration Faces Sustained Pressure From Cyber Incidents
Public administration is the most targeted sector in the EU, accounting for 38.2% of identified incidents in its referenced threat landscape. Furthermore, ENISA flags DDoS attacks, data-related threats, and social engineering as prominent risks for this sector.
ENISA illustrates why high-profile EU institutions are attractive targets, they deliver essential services and manage sensitive data, while attacks can generate outsized political and reputational impact. In other words, attackers often seek visibility and leverage, not just system access.
Breach Impact Goes Beyond Stolen Files
Even when an organization isolates an incident quickly, the downstream effort can be substantial. While a public institution’s cost categories differ from a private company’s, the operational drag investigation time, legal work, and notifications still tends to be significant.
In parallel, broader breach research helps explain why cloud-hosted web platforms can be attractive. Investigations into cloud compromises often examine identity events and access pathways just as closely as software vulnerabilities.
What To Watch As The Europa Breach Story Develops
The nature of the types of information that were actually accessed may be clarified, as “data taken from websites” can vary from innocuous information types to more sensitive personal or operational information.
The number and nature of “Union entities” that may be impacted will also be important, as this may indicate whether the compromise was contained or whether it involved a broad range of shared resources. The posture of the threat actor will also be important. The attacker had not planned to extort the Commission but would leak the information anyway.
Conclusion: When a “Public” Website Becomes a Private Data Problem
The Europa.eu incident shows how misleading uptime can be. The websites stayed online, yet investigators believe data was taken from the cloud environment behind them. That is the modern breach paradox, public services can look normal on the surface while sensitive information is being extracted quietly in the background.
Why This Incident Matters Beyond One Platform
This is not just a website story. It is a cloud governance story.
- Public web platforms often sit on top of storage that holds far more than pages and images
- Shared infrastructure can create spillover risk across multiple institutions
- A breach with no downtime can still become a major exposure event
- Stolen data can fuel later leaks, scams, and targeted social engineering
When availability is the only metric, silent exfiltration is easy to underestimate.
Where Xcitium Changes the Outcome
For organizations in this position, the failure usually happens in two places, visibility first, then access control.
- Xcitium Vulnerability Assessment helps surface exposed services, risky configurations, and weak cloud-facing assets before attackers find them
- Xcitium Identity Threat Detection and Response helps detect suspicious access behavior if the intrusion path involves stolen identities, abnormal sign-ins, or unauthorized cloud access
If you have Xcitium in place, this kind of breach is far less likely to remain invisible long enough to become a multi-entity exposure.
Secure the Cloud Behind the Website
Public-facing platforms are no longer just publishing tools. They are part of the data plane. Treat them that way, reduce exposed attack surface, monitor identity activity continuously, and assume silent theft matters as much as visible disruption.