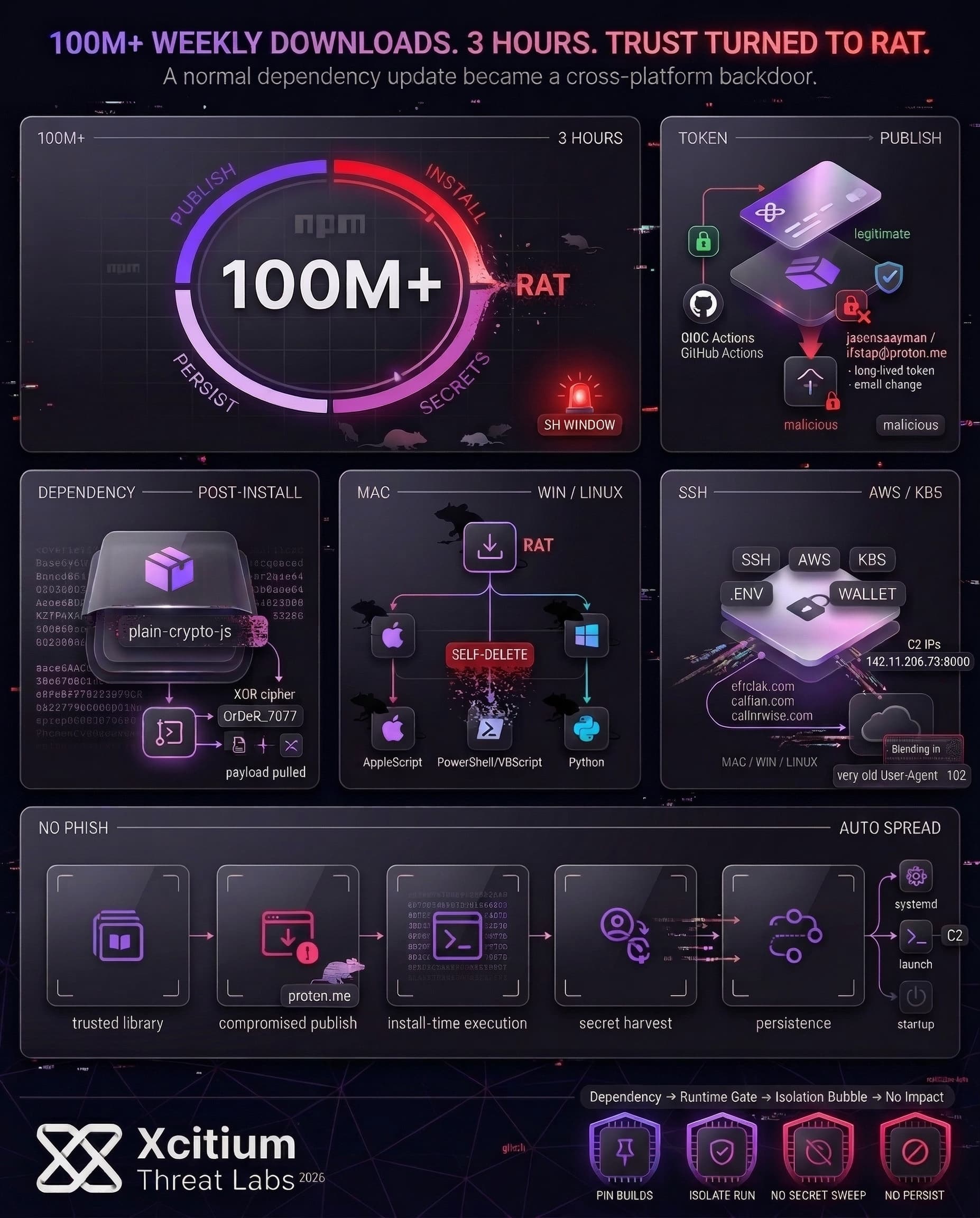
One of the most popular HTTP client libraries in use, Axios, with more than 100 million weekly downloads from npm, was compromised and utilized as a distribution channel for a cross-platform remote access trojan (RAT) on March 30, 2026.
The attacker was able to gain access to the npm account associated with the lead maintainer and released two malicious versions, targeting both the actively maintained 1.x and previously maintained 0.x lines in a short time. The attacker did not modify Axios; instead, a backdoor was added in the form of a dependency, which was only meant to distribute persistent malware targeting macOS, Windows, and Linux. After executing, the malware deleted itself, making it challenging to investigate.
What Happened When axios Was Backdoored
An attacker used compromised publisher access to push two backdoored axios releases: axios@1.14.1 (tagged latest) and axios@0.30.4 (tagged legacy). The backdoored packages included the addition of a new dependency, plain-crypto-js@4.2.1, intended to run a post-install routine and stage the cross-platform remote access tool.
The attacker changed the maintainer account email to a proton[.]me address and published the package using the long-lived token instead of the OIDC publishing method. The nuance is important because, in the presence of OIDC and a token, the token is given precedence, and this is an important factor in explaining the failure modes of “secure publishing” mechanisms.
Supply Chain Indicator – OIDC Metadata Mismatch
// axios@1.14.0 – LEGITIMATE
“_npmUser”: {
“name”: “GitHub Actions”,
“trustedPublisher”: { “id”: “github”, “oidcConfigId”: “….” }
}
// axios@1.14.1 – MALICIOUS
“_npmUser”: {
“name”: “jasonsaayman”,
“email”: “ifstap@proton.me”
// no trustedPublisher, no gitHead
}
Why This Three-Hour Window Created Outsized Risk
The reason why this escalated so rapidly is that axios is not an edge case library, and its use is widespread throughout JavaScript applications, both client-side and server-side. This means that even a temporary malicious version can rapidly disseminate through automated build and deploy processes.
Timing also contributed to why this instance was so damaging. The first instance was seen just a minute and a half after one version of this malicious axios went live. This means, effectively, that the perpetrator did not even have to trick individuals into opening files, as the standard behavior of updating versions would disseminate them rapidly throughout the ecosystem.
The overall takeaway here, however, is that supply chain attacks are increasingly similar to third-party attacks in terms of overall risk and damage potential. Third-party involvement in breaches double from 15% to 30% over the course of the last year, and a median of 94 days to remediate leaked secrets discovered in a GitHub repository.
How The Malicious Dependency Turned Installs Into Remote Access
While the package name and versions were specific, the method used was again familiar. This time, it was “install time execution.” Once plain-crypto-js@4.2.1 was added as part of the dependency list, the post-install script ran a script setup.js, using layered obfuscation. Therefore, it would not be immediately clear what the script was doing.
In the technical details, the method used was described as a two-part decoding process using reversed Base64 and an XOR cipher with the key “OrDeR_7077.” Once decoded, the installer-stage code reached out to the command and control and pulled down the payloads. This same dependency could be used to attack macOS, Windows, and Linux systems.
macOS
- Execution Vector: AppleScript dropper
- C2 Communication:
packages.npm.org/product0 - Payload Location:
/Library/Caches/com.apple.act.mond(masquerading as Apple cache) - Execution: Background execution via
/bin/zshwith modified permissions (chmod 770) - Evasion: Self-deleting dropper to reduce forensic artifacts
Windows
- Execution Vector: VBScript PowerShell multi-stage chain
- C2 Communication:
packages.npm.org/product1 - Masquerading: PowerShell binary copied to
%PROGRAMDATA%\wt.exe - Execution: Hidden PowerShell invocation with execution policy bypass
- Payload Delivery: In-memory execution via dynamically retrieved script (fileless)
- Persistence Artifact:
%PROGRAMDATA%\wt.exe
Linux
- Execution Vector: Direct Python RAT deployment
- C2 Communication:
packages.npm.org/product2 - Payload Location:
/tmp/ld.py - Execution: Detached execution via
nohup - Evasion: Traffic disguised to resemble npm-related activity
Another network behavior, which seems intentional, is that it “blends in.” The HTTP POST bodies seem designed to look like strings from a registry, with different strings depending on the OS. The infrastructure uses a constant path (/6202033) as a campaign identifier, while the beacon uses an intentionally out-of-date user-agent string across all OS. These things matter because they suggest an operator thought about scale, noise, and repeatability, rather than just trying some one-off stunt.
Why Supply-Chain Attacks Keep Scaling In Open Source Ecosystems
The attacker is targeting a distribution chokepoint, not a particular organization. If an attacker can publish to a high-dependency package, he can reach countless downstream builds in parallel. Developer workstations and CI systems are especially appealing because they are often close to secrets, signing keys, and deployment paths.
Last year, over 454,600 new malicious packages were detected, bringing the cumulative total to over 1.233 million malicious packages across major registries. Additionally, the same system also revealed that “trillions of downloads are consumed annually, and the rate is growing fast year over year.” These numbers help illustrate why these supply chain attacks continue to prove successful: the distribution surface area is vast, and the cost to attempt such an attack is low.
The history of actual attacks demonstrates that this is not an isolated incident and that this is not a one-library or one-year problem. The event-stream incident, included malicious code that was introduced through a dependency that was added by a new maintainer, and this incident was targeting a particular downstream application environment. The ua-parser-js incident included malicious versions that were published to npm and later documented in the GitHub Advisory Database. Thus, the axios incident is an escalation, especially regarding its speed and cross-platform nature, but it is not an isolated incident.
Indicators Of Compromise For The axios npm Supply Chain Compromise
Conclusion: When a Trusted Dependency Becomes the Delivery System
The axios compromise shows how quickly software trust can turn into remote access. One of the most widely used JavaScript libraries in the world became a cross-platform RAT distributor, not because developers downloaded something suspicious, but because normal dependency resolution did exactly what it was designed to do. That is what makes supply chain compromise so dangerous. The attack rides on trust, speed, and automation.
Why This Threat Scales So Fast
This was not a niche package or a targeted one-off.
- Axios serves more than 100 million weekly downloads
- The malicious window lasted only hours, yet installs began almost immediately
- The backdoor was delivered through install-time execution, not user action
- macOS, Windows, and Linux were all included in the same campaign
Once the poisoned version entered CI pipelines and developer systems, the attacker no longer needed phishing. The ecosystem did the distribution for them.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
With Xcitium Advanced EDR, the post-install chain fails at execution.
- Obfuscated setup routines are intercepted when they try to run
- Downloaded payloads can execute, but code can run without being able to cause damage
- Remote access never becomes persistence, credential theft, or downstream compromise
The attacker may reach the environment, but not the real system.
Secure the Build Chain Before It Ships the Breach
Supply chain attacks win when trusted software is allowed to execute blindly. Defend the endpoint, protect the build pipeline, and stop malicious code at runtime before one dependency becomes thousands of compromises.