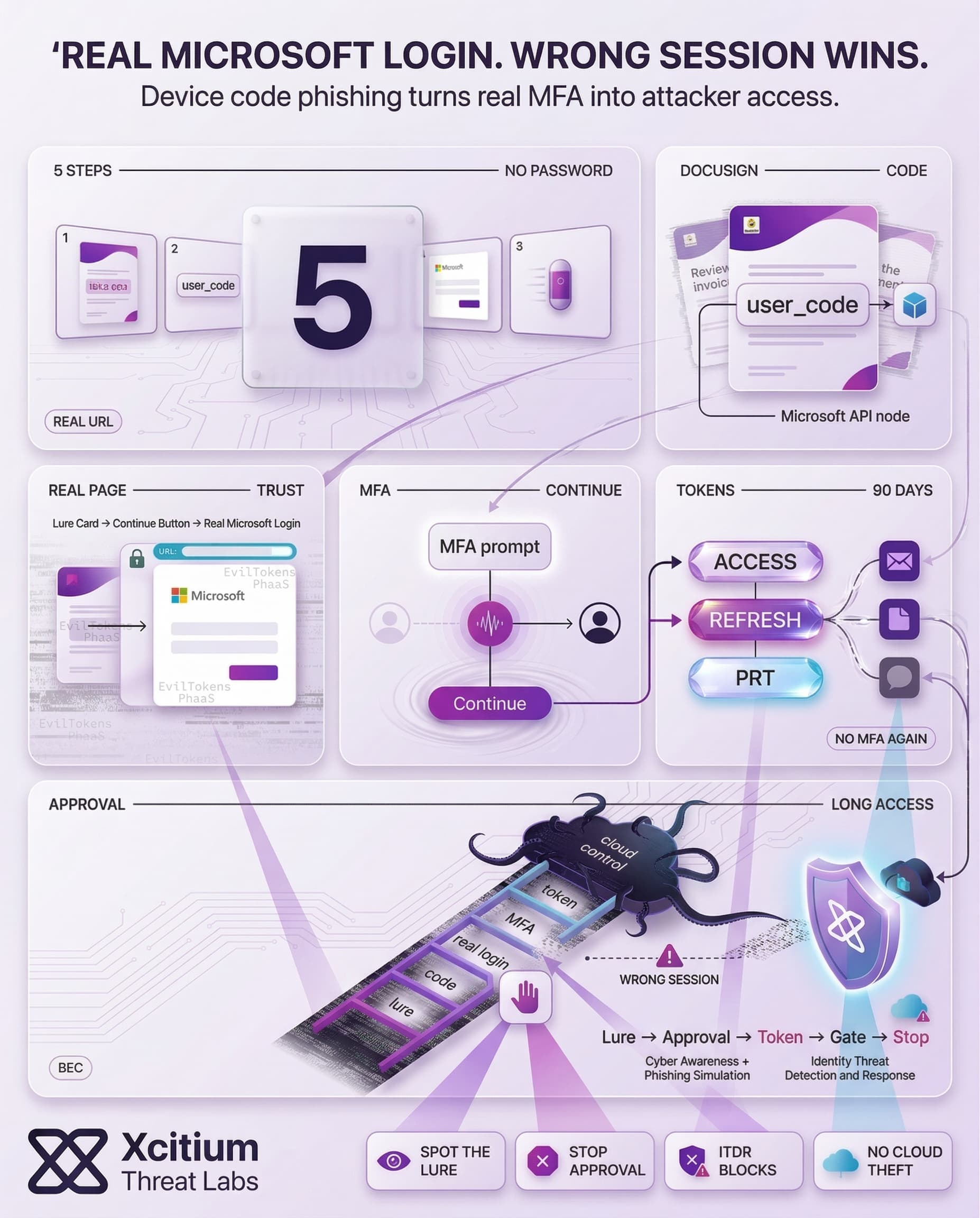
The EvilTokens approach is taking the Microsoft device code phishing into a more ‘productized’ form. Rather than copying the sign-in pages, it uses a real Microsoft sign-in approach and uses social engineering tactics to trick the victim into granting access to the attacker’s session.
The difference here is the flip in the result, instead of password theft, the attacker is stealing OAuth tokens. EvilTokens is being sold as a kit on Telegram, aiming at being used for business email compromise attacks, with plans for expanding past the focus on Microsoft-based attacks into Gmail and Okta pages.
Device Code Login Was Built For Constrained Devices And Simple Setup
The OAuth 2.0 Device Authorization Grant is available for use by devices that cannot easily support interactive web sign-in, like smart TVs. They display the short code and verification URL. Then, the user signs in on another device like a phone or computer using a normal browser.
After the user grants approval for the request, the original device is able to receive access and refresh tokens so it can act on behalf of the user. This code is not ‘extra verification.’ It is the authorization key that links the sign-in attempt to the device session.
Device Code Phishing Works Because The Right Page Is Still The Trap
“Device code phishing” takes advantage of the difference between the “requesting device” and the “sign-in device.” The phishing attack begins with a legitimate device authorization request, which obtains a time-limited device code. This is then sent to the victim with a lure, which directs the victim to the legitimate device sign-in process. This leads to the victim signing in and unknowingly approving the phishing request through multi-factor authentication (MFA).
The phishing attacker then receives the issued tokens and can use these to access. This is because the victim is signing in to a legitimate domain, and all the traditional signs of a fake site are eliminated. Successful device code phishing attacks have been active since at least August 2024, which proves this type of phishing is effective. Common lures include:
- “View the document” or “review the invoice” related to daily work activities
- QR codes to make the phishing process easier and faster
- A “continue” button to redirect to a legitimate Microsoft sign-in page
Device Code Phishing via EvilTokens
- EvilTokens PhaaS offers self-hosted phishing templates for device code-based attacks.
- The phishing pages may resemble the following:
- Pages may be disguised as Microsoft services or trusted application names like Adobe Acrobat or DocuSign.
- Users may be asked to verify their identity in order to open the document.
- Users receive a verification code from the Microsoft device authorization flow.
- They may be asked to complete the verification process.
- There may be a “Continue to Microsoft” button to redirect the user to the device login page.
- After entering the verification code, the actual Microsoft sign-in page may be prompted.
- Once the user has been authenticated, the attacker device may be granted access to the user’s account for the targeted application.
EvilTokens Productizes The Workflow With Templates And Operator Tooling
EvilTokens offers scale through standardization both in terms of lure and token-handling workflow. These are common themes for document signing, file sharing, invoices, meeting invites, and payroll notifications. EvilTokens is more than “just phishing,” focusing on operator tooling and automation for faster email frauds once access is gained.
Campaign mapping provided alongside the kit points towards wide-scale targeting as well, while countries most impacted appear to be the US, Canada, France, Australia, India, Switzerland, and UAE.
Tokens Matter More Than Passwords Because They Enable Fast, Quiet Access
Token theft changes the definition of account compromise. Access tokens have a limited lifetime (around 60 to 90 minutes), while refresh tokens have a maximum lifetime of 90 days to renew access without re-signing in.
The Primary Refresh Token (PRT) is a long-lived single sign-on token with a maximum lifetime of 90 days. Once compromised, attackers can impersonate the victim across cloud services and renew tokens before their lifetime ends.
Using stolen tokens, attackers can easily:
- Open the mailbox to search for payments or vendor threads
- Access cloud files and collaboration data with the same identity
- Switch services with single sign-on
Business Impact: Device Code Phishing Aligns With BEC Economics
Business Email Compromise is based on legitimacy, with device code phishing providing legitimacy through a genuine login process. The FBI’s Internet Crime Report reports BEC at $2.77 billion in losses, with 21,442 complaints.
A technique that can often provide legitimate access to an inbox can create massive financial losses. This is in line with EvilTokens, which targets finance, HR, logistics, and sales teams, who handle invoices, payroll changes, purchase orders, and shared documents, often under time pressure.
The Larger Shift: Identity Abuse Moves From Credential Theft To Consent Capture
EvilTokens is an example of an overall trend towards credential theft and the capture of consent. MFA has made password phishing less effective. Device code phishing takes legitimate compliant actions and turns them into a grant for the wrong session. In other words, the victim is performing a legitimate login, but the beneficiary is the wrong party.
The roadmap given by reporting the expansion beyond Microsoft-centric pages suggests that this type of attack is likely to expand to other identity landscapes over time. This is because phishing toolkits will evolve to become services, and token-based attacks will be able to scale without changing the face of the login page.
Conclusion: Device Code Phishing Turns Legitimate Login Into Illegitimate Access
EvilTokens shows why token theft is scaling faster than password theft. The victim signs in to a real Microsoft domain, completes MFA, and still grants the attacker long-term access because the authorization is linked to the attacker’s session, not the victim’s intent.
Why This Threat Matters
This is phishing designed to remove the classic warning signs.
- The lure fetches a real device user code from Microsoft and displays it inside a trusted looking “DocuSign” style workflow.
- The victim is sent to the real Microsoft login page, which removes the usual fake site indicators.
- MFA approval becomes the attacker’s authorization, tokens are issued to the attacker, and the session persists.
Why Organizations Are Vulnerable
Token theft changes the compromise model. Access tokens may last 60 to 90 minutes, while refresh tokens and the Primary Refresh Token can extend access up to 90 days. Once tokens are stolen, attackers can move through mail, cloud files, and other services with single sign-on.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
- Xcitium Cyber Awareness Education and Phishing Simulation reduces successful consent capture by training users to recognize device code lures and stop before approval.
- Xcitium Identity Threat Detection and Response helps detect and stop risky identity behavior after token issuance, so stolen tokens do not translate into mailbox access and cloud data theft.
Protect Identity After Login, Not Only At Login
EvilTokens proves the attacker no longer needs your password. They need your approval. Secure consent paths, monitor token based access, and treat identity abuse as the primary perimeter.