Geographic Targeting and Unique Tactics
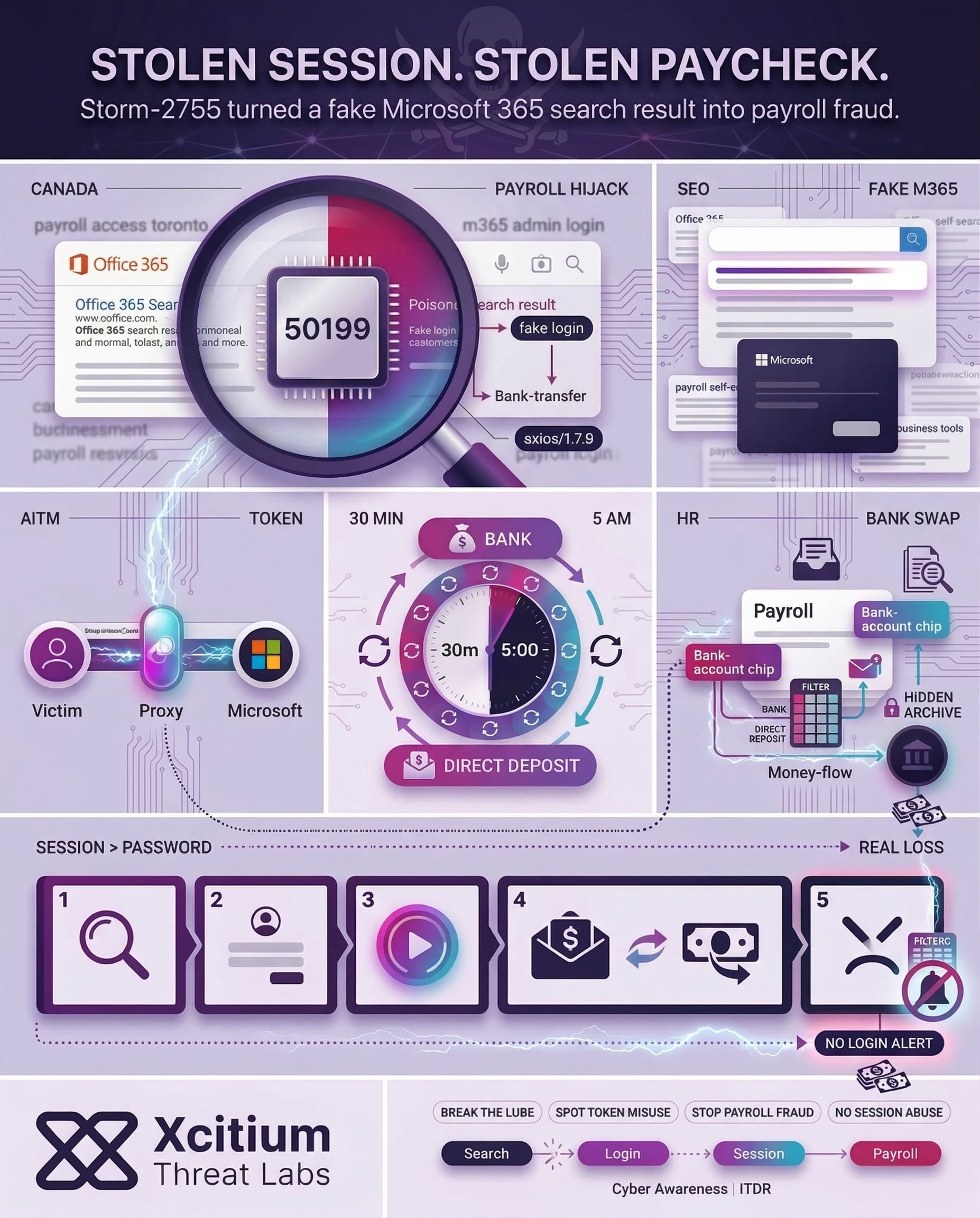
Storm-2755, nicknamed a “payroll pirate,” targeted Canadian organizations to reroute employee paychecks. Attackers compromised staff accounts and secretly changed payroll settings so that salaries were sent to bank accounts they controlled. Rather than focus on a specific industry, Storm-2755 targeted Canada as a whole. The attackers relied on malvertising and SEO poisoning of generic search queries to find victims.
SEO Poisoning and Malvertising: Credentials at the Crossroads
The Storm-2755 first infection relied upon search engine poisonings. The hackers placed bids on commonly searched terms such as “Office 365” and misspellings (“Office 265”) so that a phishing website would show up when the users were conducting their searches.
The victim clicking the search result would then be directed to a phishing version of the Microsoft 365 login website (hosted at bluegraintours[.]com), where the attacker would steal the credentials of the victim before redirecting them to the actual Microsoft website.
Adversary-in-the-Middle: Hijacking Sessions with Axios
After credential harvesting, the Storm-2755 actor performed an AiTM session hijack. From the logs, Microsoft Entra 50199 error followed by a login using Axios/1.7.9 user agent. However, the session ID is identical to the credential harvesting attempt. This suggests that rather than attempting a traditional sign-in process, the attacker only needed to replay the stolen token. Essentially, the attacker’s proxy obtained the OAuth token live during the credential harvest process.
Persistence and Off-Hours Tactics
However, Storm-2755 continued to exploit Axios to keep the tokens refreshed continuously so that the victims would remain logged in for several days at a time. The perpetrators maintained silence as they kept refreshing sessions approximately every 30 minutes.
Moreover, they also ensured that tokens would be renewed approximately around 5:00 AM local time so that they could not be detected. After the tokens finally expired within 30 days or so, some criminals reset the password/MFA settings for the victims.
Discovery: Hunting Payroll and HR Data
Once the attacker had access to the account, Storm-2755 sought out payroll and financial data. Using queries to the target’s computer network and mail accounts for words such as “payroll,” “finance,” or “banking,” the attackers sent the target’s HR department an email under the subject line of “Question regarding direct deposit,” asking for the employee to update his banking information.
In other words, Storm-2755 attempted to act as the employee himself in order to have HR update the direct deposit account. In the event that the attempt was not successful, Storm-2755 logged in to the HR/payroll site themselves and updated the employee’s bank directly.
Defense Evasion: Inbox Rules and Timing
Additionally, Storm-2755 hid evidence by creating inbox rules to filter any email with keywords like “direct deposit” or “bank”. This meant alert emails from HR were moved out of the user’s view. Coupled with the off-hours token renewals, these measures kept the compromise hidden. Neither the employee nor IT saw obvious alerts that payroll changes were happening.
Impact: Stolen Salaries and Direct Loss
In summary, the attack achieved tangible success by directing at least one paycheck into the attacker’s account. Since the attacker logged into the system using the victim’s session, no external login warnings were triggered. This theft went unnoticed until the victim realized that the paycheck did not arrive.
This attack demonstrates a growing pattern: a similar group named Storm-2657 deployed the same attack vector on American educational institutions. Of particular interest is Storm-2755, whose unique traits include exploiting SEO tactics and targeting Canadian entities. It is worth noting that in this attack, emails were not used for phishing; rather, the use of poisoned search results exploited users’ natural tendencies.
Indicators of Compromise (IoCs)
- Malicious domain:
bluegraintours[.]coma phishing site mimicking Microsoft 365 logins. - User agent:
axios/1.7.9appears in authentication logs immediately after a 50199 error, indicating a token was replayed. - Login error: A Microsoft Entra 50199 error appearing just before a successful login is a hallmark of Storm-2755’s AiTM token relay.
- Authentication pattern: Repeated sign-in failures ending with a 50199 error followed by a success under the same session ID (token reuse).
- Hidden inbox rules: Filters for keywords like “bank” or “direct deposit” in a user’s mailbox, especially newly created rules.
- Payroll changes: Unauthorized updates to an employee’s payment or bank account in HR systems (e.g. Workday) made via the employee’s own account.
Conclusion: When a Stolen Session Becomes a Stolen Paycheck
Storm-2755 shows how modern phishing no longer ends with credential theft. It ends with token replay, silent session persistence, and direct financial loss. In this campaign, poisoned search results led victims to a fake Microsoft 365 login page, then an Adversary-in-the-Middle flow captured the live OAuth token and turned one sign-in into payroll fraud.
Why This Threat Matters Now
This attack works because it blends into normal behavior, then stays quiet long enough to profit.
- Victims searched for familiar terms like Office 365 and landed on attacker-controlled results
- The stolen session was replayed instead of using a traditional login flow
- Tokens were refreshed continuously, often during off-hours, to avoid detection
- Inbox rules hid keywords like “bank” and “direct deposit,” keeping warning emails out of sight
- At least one paycheck was successfully rerouted before the victim realized it was missing
Why Organizations Stay Exposed
Password resets and MFA are not enough when the attacker already has the session. Once the proxy captures the token, the criminal is no longer trying to break in. They are operating as the user.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
- Xcitium Cyber Awareness Education and Phishing Simulation reduces the first failure point by training users to distrust poisoned search results and fake Microsoft 365 login flows
- Xcitium Identity Threat Detection and Response helps stop the second stage by detecting risky session behavior, token misuse, and follow-on payroll access before the fraud is completed
Protect the Session, Not Just the Password
Storm-2755 proves that the real target is not the login page, it is the authenticated session that comes after it. Train users to break the lure, then monitor identity behavior so stolen tokens do not become stolen salaries.




