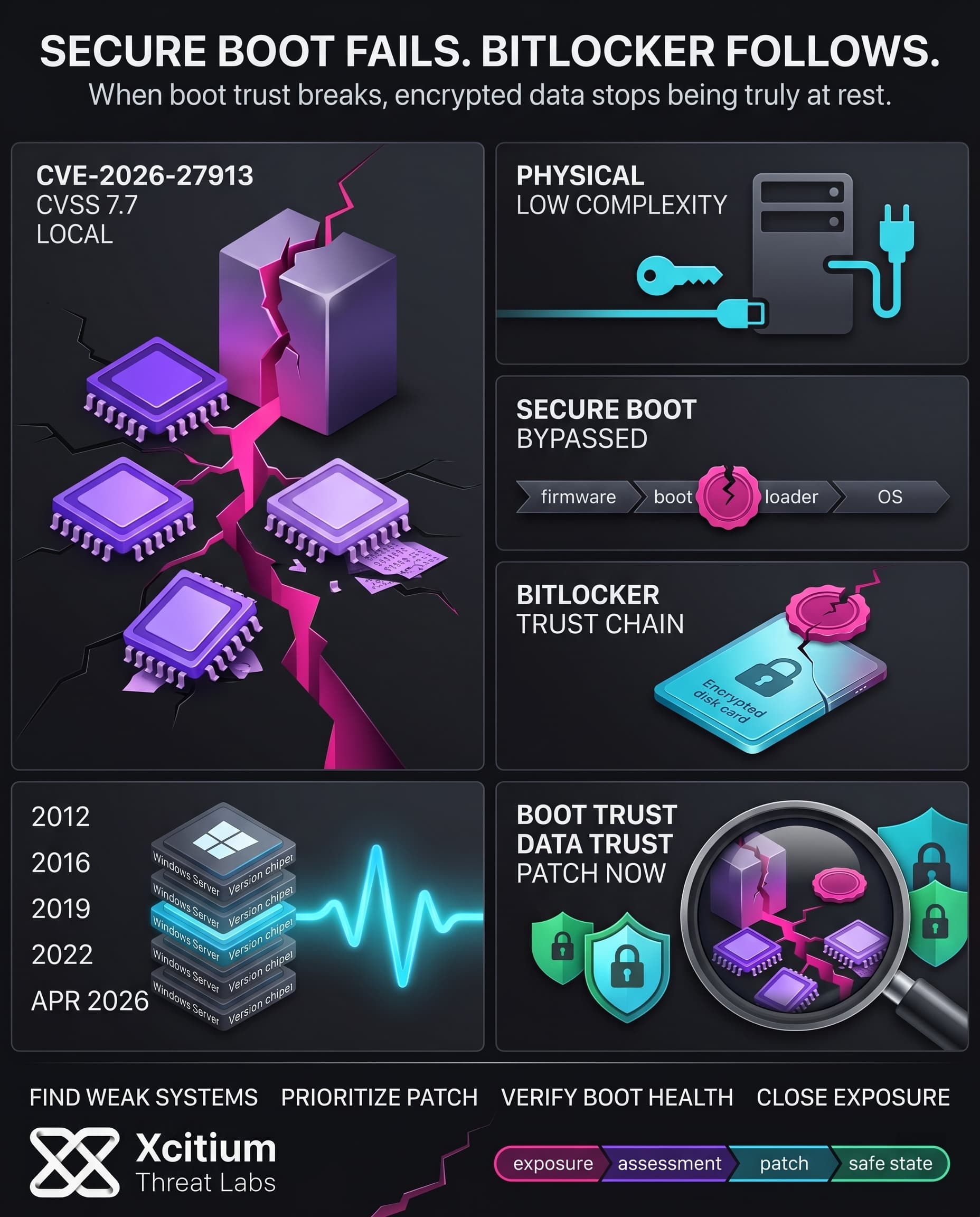
Full disk encryption on windows depends on BitLocker technology. In plain language, BitLocker technology is referred to as a tool that “protects your data by encrypting your drives.” However, it appears that a security advisory (CVE-2026-27913) shows a vulnerability that occurs because of a lack of proper input validation and allows a malicious local user to breach protection measures.
According to Microsoft, no one currently uses this vulnerability; however, it still is an important problem and is classified as such. According to the information from Microsoft, this issue is expected to lead to exploitation of data stored on encrypted drives despite the use of UEFI Secure Boot.
Key Details of the BitLocker Flaw
CVE-2026-27913 is a vulnerability related to insufficient input validation in BitLocker. Basically, a local attacker having prior access to the machine would use malicious inputs that will allow the BitLocker checks to fail.
- Attack Vector: Requires local access (physical presence or an existing system account).
- Complexity: Very low the attacker needs no extra privileges or user clicks.
- CVSS Score: 7.7 (High/Important severity).
- Impact: Confidentiality and integrity are at risk attackers can bypass UEFI Secure Boot.
- Affected Systems: Broad range of Windows Servers. All supported Windows Server releases (2012 through 2022, Standard or Server Core) are vulnerable.
This problem should be considered extremely serious for every enterprise using BitLocker encryption on Windows servers. It should also be stressed that UEFI Secure Boot feature which guarantees that only trusted software is loaded during startup can be entirely bypassed with this vulnerability.
Why Bypassing Secure Boot Matters
The role of Secure Boot in ensuring the integrity of the boot process through signature validation of the OS loader helps to safeguard against malware infections during startup processes. BitLocker depends on this mechanism, meaning that if there is any tampering within the boot chain, BitLocker should never decrypt any information. CVE-2026-27913 breaks down this expectation because Microsoft notes that a hacker can “bypass Secure Boot entirely.”
The attacker can manipulate the boot loader software without detection by BitLocker. Previous attacks such as the bitpixie vulnerability indicate that hackers exploit weaknesses within Secure Boot mechanisms to compel the system to display BitLocker’s master key. The PXE attack illustrated how hackers could capture the BitLocker key from computer memory. Thus, CVE-2026-27913 seeks to achieve similar objectives.
This attack bypasses the boot security mechanisms. After bypassing the boot process, any unauthorized code can load in the startup sequence and enable access to the encrypted volume.
Affected Windows Systems
The vulnerability affects Enterprise Windows distributions. More precisely, it affects Windows Server 2012, 2012 R2, 2016, 2019, and 2022. Both regular installations and Server Core editions are affected. Consumer versions (Windows 10/11 Pro) are not affected, which means that there is something wrong with server-only components.
In general, enterprises use BitLocker for encrypting client computers as well, but from the information available through the CVE-2026-27913, it becomes clear that the problem concerns only server editions. Nonetheless, any BitLocker usage may be potentially exploited. BitLocker is included in all Windows editions and typically activated automatically in enterprise-grade devices, so the number of potential targets can be quite high. In case when an adversary gains unauthorized access to a patched but not fixed server, this vulnerability can be used to obtain sensitive information and install bootkits.
With such diversity of the targeted devices, it is important for large data centers and cloud hosting providers using Windows Server to update their security policies immediately. It seems like having BitLocker installed but not protected against other threats is not going to help either.
Real-World BitLocker Bypasses
The history of security suggests that BitLocker is not a perfect protection measure. Recently revealed security holes demonstrate how a potential hacker can crack down on the full-disk encryption. In the case of the BitPixie flaw (CVE-2023-21563), a potential attacker can degrade the Windows Boot Manager, launch a unique boot procedure, leave the BitLocker keys in the RAM, and access them. Using merely a LAN cable and a keyboard, a thief can easily break the protection of a Windows hard drive with Secure Boot enabled.
CVE-2022-41099 is another example that illustrates a problem with BitLocker. The vulnerability made administrators install scripts that updated the firmware to prevent BitLocker from relying on an outdated Windows Recovery partition. It is evident that BitLocker could not cope with the bug in the boot process.
CVE-2026-27913 continues a worrying trend, and there is nothing surprising in the way a potential attacker who had physical access, even if he or she combined it with remote attacks, exploited a logical error and succeeded in cracking BitLocker. Previous instances of BitLocker bypasses reveal the importance of taking any potential flaw very seriously and thoroughly checking the protection measure.
Microsoft’s Patch and Timeline
Microsoft released a patch to this particular problem during April Patch Tuesday 2026. The bulletin (dated April 14, 2026) acknowledges both a security researcher and internal teams for identifying this specific issue. As there is no public exploit reported yet, the vulnerability receives “Important” classification from Microsoft.
From practical standpoint, all systems that install monthly updates through rollup will have a patch in place. Still, not every attack is software-specific; therefore, administrators need to make sure that all necessary patches are installed for April 2026 and check if BitLocker and Secure Boot functionality works properly. Failure to do so may leave critical information vulnerable once someone finds a way to exploit the vulnerability.
Upon installing the patch, review system logs for abnormal boot processes and be wary of new techniques to circumvent BitLocker protection. According to the community, the data at rest is as protected as the most vulnerable link in the boot chain. Understanding of this specific vulnerability within BitLocker context becomes critical.
Conclusion: When Secure Boot Fails, Encrypted Data Stops Being Secure
CVE-2026-27913 is a reminder that full disk encryption is only as strong as the boot chain it trusts. BitLocker is designed to protect data at rest, but if Secure Boot validation can be bypassed, that protection can collapse before the operating system even starts. In that moment, encryption no longer acts like a barrier. It becomes a delayed assumption.
Why This Threat Matters
This flaw is serious because it targets the trust model beneath the operating system itself.
- A local attacker can bypass UEFI Secure Boot protections
- Broad Windows Server deployments are affected
- No extra privileges or user interaction are required
- Physical access or an existing foothold can be enough to expose encrypted data
When the boot path is weakened, the value of BitLocker drops with it.
Where Xcitium Changes the Outcome
For organizations using Xcitium Vulnerability Assessment, this exposure should have been visible before attackers could take advantage of it.
- Vulnerable Windows Server systems are identified and prioritized for remediation
- Missing April 2026 security updates become actionable immediately
- Weak links in the protection chain are surfaced before encryption is put to the test
If you have Xcitium in place, this attack would not succeed, because the vulnerable systems are identified and patched before the bypass can be used.
Trust the Patch, Not the Assumption
BitLocker still matters, but security at rest depends on integrity at boot. Patch quickly, verify Secure Boot health, and treat every boot chain flaw like a direct data exposure risk.