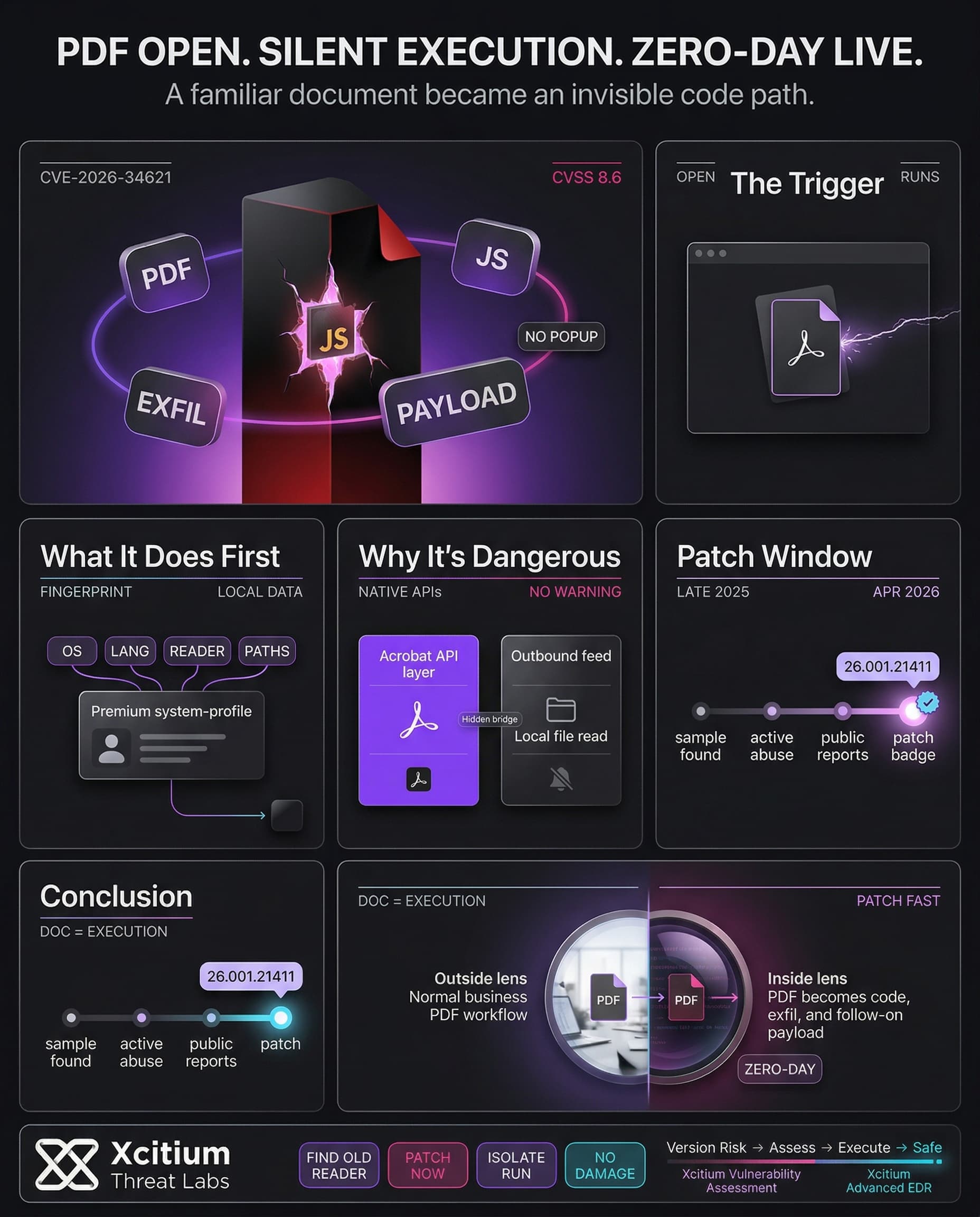
Adobe has issued an urgent patch addressing a severe zero-day vulnerability (CVE-2026-34621) in Acrobat and Acrobat Reader on Windows and macOS systems. This prototype pollution vulnerability in the embedded JavaScript engine can be leveraged by malicious PDF files to modify Acrobat objects and execute arbitrary code with the permissions of the logged-on user.
According to Adobe’s official security bulletin, this vulnerability is ranked as “critical” (CVSS score: 8.6), and Adobe confirmed that it has already been exploited in attacks against customers in the wild. Some important details related to CVE-2026-34621 are as follows:
- Flaw type: JavaScript prototype pollution in Acrobat/Reader (CWE-1321).
- Impact: Enables remote code execution under the current user, potentially leading to full system compromise.
- Affected products: Acrobat DC/Reader DC (Continuous track) ≤26.001.21367, and Acrobat 2024 (Classic) ≤24.001.30356.
- Patched versions: Acrobat DC/Reader DC 26.001.21411 (Win/Mac) and Acrobat 2024 v24.001.30362 (Win) or 30360 (Mac).
The exploit was first noticed in late 2025. Malicious PDFs were found to embed heavily obfuscated JavaScript to “fingerprint” victims and exfiltrate data.
For example, a malicious PDF named “yummy_adobe_exploit_uwu.pdf” was found to collect system language, OS version, Reader version, and local file paths, sending all this information to an attacker-controlled server. The exploit leverages legitimate Acrobat APIs notably util.readFileIntoStream and RSS.addFeed to siphon data from the machine. Since the malicious code runs instantly on open, victims see no warning or popup when infected.
Pollution Exploit.
util.readFileIntoStream to “fingerprint” systems and exfiltrate OS details to remote C2 servers silently.
• Acrobat 2024 (Classic) ≤ 24.001.30356
Malicious PDF Exploit Techniques
Analysis indicates that the attack chain utilizes common PDF scripting techniques and sophisticated data exfiltration methods. Once opened, the booby-trapped PDF triggers the embedded JavaScript automatically, without any further interactions required by the target. Moreover, attackers can deliver further payloads through a command-and-control server. The following key features have been identified for this exploit:
- Data exfiltration: Local system information (such as the OS version, Reader version/build, locales, file paths) was gathered and transmitted to the attackers via the booby-trapped PDF.
- Silent operation: Exploitation does not leave any traces behind. The malicious script uses Acrobat’s native functions to read data from local files and feeds on the internet.
- Payload delivery: Further malware (backdoors, ransomware, etc.) can be delivered from a remote location to the infected systems.
- Phishing bait: In order to hide their malicious intent, attackers use crafted PDFs containing innocuous-looking graphics/text. Analysts found that the booby-trapped PDF contained Russian-language images relating to gas supply crises, implying that the targets were located in Russia.
Timeline of Discovery and Patch
The malware sample came to light towards the end of November 2025. Exploits were being exploited as far back as November 2025. Alerts in the public domain were made in the beginning of April 2026 after the results were published, resulting in a quick reaction from Adobe. This is how things went down:
- Nov 28, 2025: Initial malicious PDF sample is submitted to VirusTotal.
- Dec 2025: Active attacks using this zero-day continue; systems are quietly compromised via emails or web links.
- Apr 9–12, 2026: Security outlets and reports bring wide attention to the flaw.
- Apr 11–12, 2026: Adobe issues APSB26-43 advisory and releases patched Acrobat/Reader builds for all affected platforms.
- Apr 12, 2026: Adobe adjusts the CVSS from 9.6 to 8.6, noting the vector is local (requires opening the PDF).
Affected Versions and Patch Details
Adobe’s security bulletin (APSB26-43) lists the exact products and versions in need of updates. In summary:
- Acrobat DC / Acrobat Reader DC: Continuous track up to 26.001.21367 (patched in 26.001.21411 for Win/Mac).
- Acrobat 2024 (Classic 2024 track): Up to 24.001.30356. Adobe rates the update as Priority 1 for enterprise users, underscoring its criticality. Administrators are advised to roll out the new installers immediately to eliminate the exposure.
In practical terms, any organization using Adobe Reader or Acrobat should verify that installations have moved to the above versions. The corporate release notes and patch portals list the updated builds, and both manual and automated update methods will deliver the fixes. By mid-April, patched installations should have prevented any further exploitation of CVE-2026-34621.
Affected Products and Versions:
- Adobe Acrobat DC and Adobe Acrobat Reader DC: All versions up to 26.001.21367 (fixed version is 26.001.21411).
- Adobe Acrobat 2024 (Classical track 2024): All versions up to 24.001.30356.
It is strongly recommended that all installations are checked to ensure that the correct versions are being used. Both manual and automated installation of the new software versions will fix the vulnerability. Mid-April the patches will become effective against CVE-2026-34621.
Conclusion: A PDF Should Never Become a Silent Execution Path
CVE-2026-34621 is a reminder that one of the most familiar file formats in business can still become an immediate attack vector. A booby-trapped PDF was enough to trigger obfuscated JavaScript, fingerprint the victim, exfiltrate local system data, and pull in additional payloads, all without any warning or popup when the file was opened.
Why This Threat Matters
This flaw is dangerous because it turns normal user behavior into code execution.
- The exploit runs on open, with no extra interaction required.
- It uses legitimate Acrobat APIs to read local information and communicate outward.
- It can deliver follow-on malware such as backdoors or ransomware after the initial compromise.
Why Organizations Stay Exposed
Reader and Acrobat are deeply embedded across enterprises, which makes patch lag especially costly.
- Affected versions remained common across both Continuous and Classic tracks.
- Active exploitation was observed before broad public attention and before many environments were updated.
- A single malicious document sent by email or link can become the first foothold.
Where Xcitium Changes the Outcome
Effective defense here requires two controls working together.
- Xcitium Vulnerability Assessment ensures this exposure should have been visible, by identifying outdated Reader and Acrobat installations that require urgent remediation.
- Xcitium Advanced EDR ensures that even if the file is opened, the attack does not succeed. Code can run without being able to cause damage, so follow-on payloads, persistence, and system impact never take hold.
If you have Xcitium in place, this attack does not succeed the way the attacker needs.
Treat Document Handling as an Execution Risk
Patch Reader and Acrobat immediately, verify versions across the estate, and stop treating PDFs as passive content. In modern attacks, a document is often the first executable step.