ADT Data Breach Puts 5.5 Million Customer Records At Risk
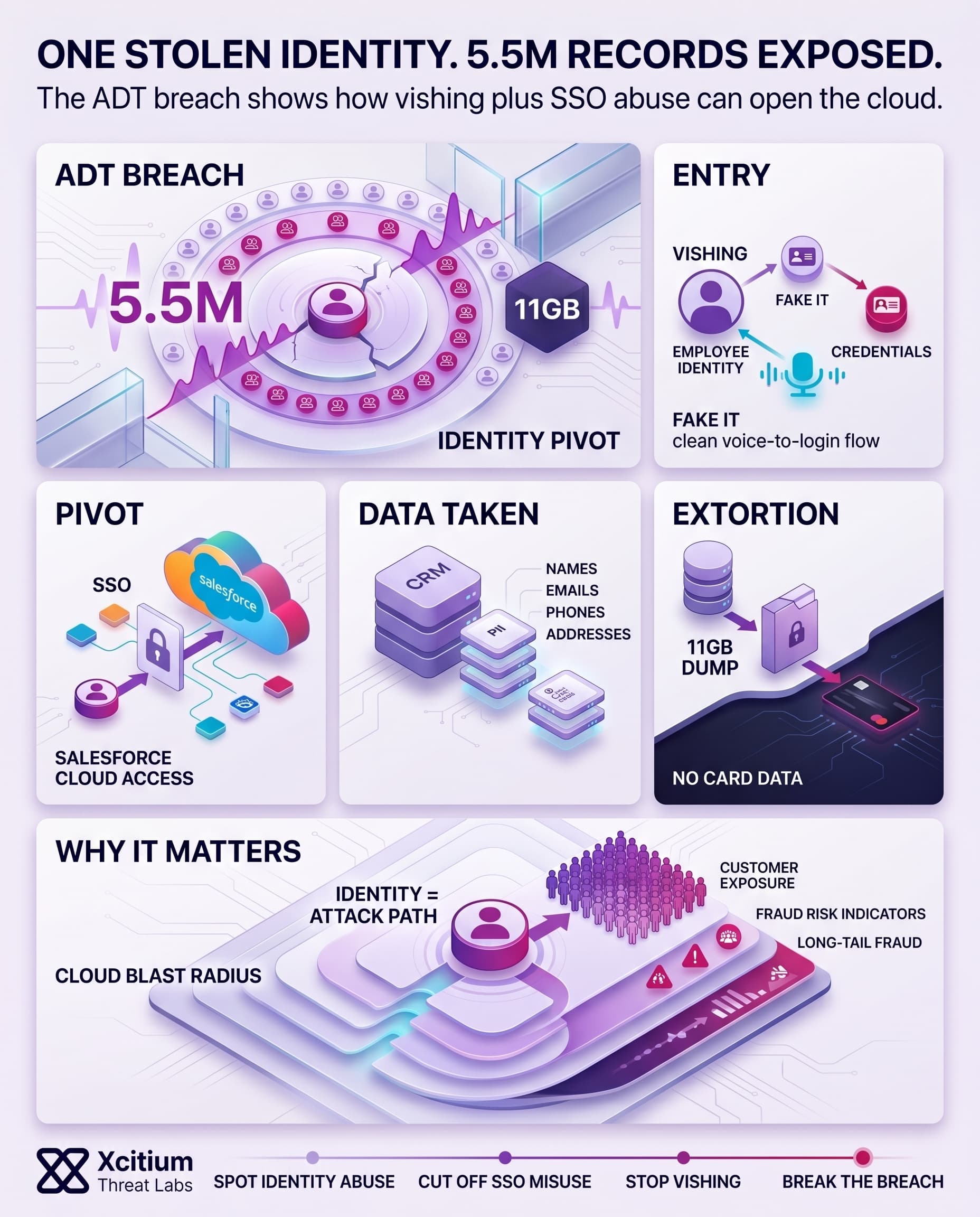
ADT, a home security systems company, experienced a data breach which left the personal data of about 5.5 million people exposed.
While ADT’s security devices continued to function normally, hackers managed to access critical personal and prospect information via cloud storage facilities used by the organization. It is crucial to understand that while the physical security of homes remained intact, their virtual security was compromised.
Some of the stolen personal information includes:
- Full names
- Email addresses
- Phone numbers
- Physical addresses
- Partial Social Security or tax ID details in limited cases
It should be noted that there were no payment card details among the stolen data. Nevertheless, it poses a significant risk of phishing, fraud, and identity theft attacks.
The Identity Pivot
A sophisticated social engineering campaign exposing 5.5 million customer records through credential harvesting and CRM exploitation.
Social Engineering Opened The Door To Enterprise Systems
Contrary to conventional ransomware attacks that depend on the use of malicious software, this security incident seems to be associated with credential compromise through voice phishing or vishing.
In this case, the attackers tricked an individual to disclose access credentials for systems that employ the single sign-on technology. They reportedly leveraged this access to pivot into the customer data environments within Salesforce.
Some of the key milestones of this attack could have been the following:
- Voice impersonation of internal support staff
- Theft of authentication credentials
- Access to centralized identity systems
- Lateral movement into cloud CRM platforms
- Bulk data extraction
Consequently, the breach reinforces how cloud ecosystems can become high-value targets when identity controls fail.
Leak Site Images Reveal A Structured Extortion Operation
The images that have been related to the cyber attack offer some useful hints for forensics. The particular image had the ADT logo on it which was probably intended to put pressure on ADT. This is one of the ways used in extortions in this era.
The other thing that can be observed is from the screen shots showing an 11 GB file. This is indicative of:
- Database exports
- CRM backups
- Structured customer records
- Segmented archival packaging
Use of public leak sites can also be seen as part of a business model emphasizing coercion when ransomware demands fail. More specifically, this can be viewed in parallel with double-extortion techniques, whereby attackers first obtain sensitive data, then threaten its release.
Why Home Security Companies Are Increasingly Attractive Targets
While ADT might not seem like a typical target for hackers at first glance, their providers maintain uniquely valuable databases.
These organizations often manage:
- Residential addresses
- Contact hierarchies
- Property ownership insights
- Installation histories
- Customer trust relationships
Criminals do not use the personal data solely for committing identity thefts. Instead, it helps in organizing burglaries or executing social engineering attacks.
In addition to that, customers tend to trust security vendors enough to disclose their most intimate data to them.
With the increasing popularity of smart homes, security firms resemble information providers rather than mere services providers.
ADT Breach Reflects A Broader Enterprise Threat Pattern
This is part of a bigger trend of large-scale attacks against SaaS and cloud-based solutions using identity hijacking.
Instead of trying to gain access to endpoints, cybercriminals have started pursuing:
- Okta environments
- Salesforce instances
- Microsoft 365 accounts
- Help desk workflows
This lowers technical requirements while raising financial gains.
Recent breach trends show why this matters:
- The global average cost of a data breach reached $4.44 million in 2025
- Mega breaches involving tens of millions of records can exceed $375 million
- Most breaches remain financially motivated
Consequently, this hack on ADT is part of something bigger. It demonstrates how cybercrime economics have evolved, where identity is now the most important attack vector.
Customer Data Exposure Carries Long-Term Consequences
This is because, even in cases where the payment details remain secure, personal data is able to enable years’ worth of future abuses.
For example:
- Address data can enable location-based scams
- Email and phone combinations strengthen phishing campaigns
- Partial government identifiers can support account verification fraud
Consequently, victims of such breaches may find themselves at risk even after the period during which their data was vulnerable.
In addition, criminal organizations have also been known to combine the stolen databases obtained through various breaches. Data obtained from one organization becomes significantly more risky in the presence of data from other organizations.
Conclusion: When One Stolen Identity Opens the Entire Cloud
The ADT breach shows how modern data theft no longer needs malware on the endpoint or disruption at the device layer. A single identity compromise, driven by vishing and followed by SSO abuse, was enough to pivot into Salesforce and expose 5.5 million customer records. Physical security systems stayed online, but the trust layer behind them failed.
Why This Threat Matters
This was not just a customer data leak. It was an identity-driven extortion path.
- Attackers used voice impersonation to steal internal credentials
- Stolen SSO access opened the door to centralized cloud systems
- CRM data was exfiltrated in bulk, with leak site pressure used to increase leverage
- Names, addresses, phone numbers, and partial government identifiers create long-tail fraud risk for victims
Why Organizations Stay Exposed
Cloud ecosystems compress access and expand blast radius at the same time. Once an attacker lands inside the identity layer, they inherit the same SaaS convenience the business depends on. Help desk trust, SSO workflows, and cloud CRM platforms become the new attack surface.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
With Xcitium Identity Threat Detection and Response, risky sign-ins, suspicious SSO use, and abnormal cloud access patterns are surfaced before data theft becomes business impact. When paired with Xcitium Cyber Awareness Education and Phishing Simulation, the vishing step loses its power before credentials are ever handed over.
- Identity abuse is detected earlier
- Suspicious lateral movement across cloud systems is cut off faster
- Users build pause and verify habits before help desk impersonation succeeds
Protect the Identity Layer Before It Becomes the Breach
The lesson from ADT is simple. In modern cloud extortion, identity is the attack path. Defend it like your most critical asset, because it is.




