Critical SharePoint Server Zero-Day Vulnerability
A severe deserialization flaw was found in Microsoft SharePoint Server (on-premises editions). This bug lets an unauthenticated attacker execute arbitrary code on vulnerable servers. It affects SharePoint Server Subscription Edition, 2019 and 2016 (on-premises only). (SharePoint Online in Microsoft 365 is not impacted.)
- Affected Systems: On-premises SharePoint Server 2016, 2019, and Subscription Edition.
- Impact: Remote Code Execution with SYSTEM privileges; attackers need no credentials to exploit the flaw.
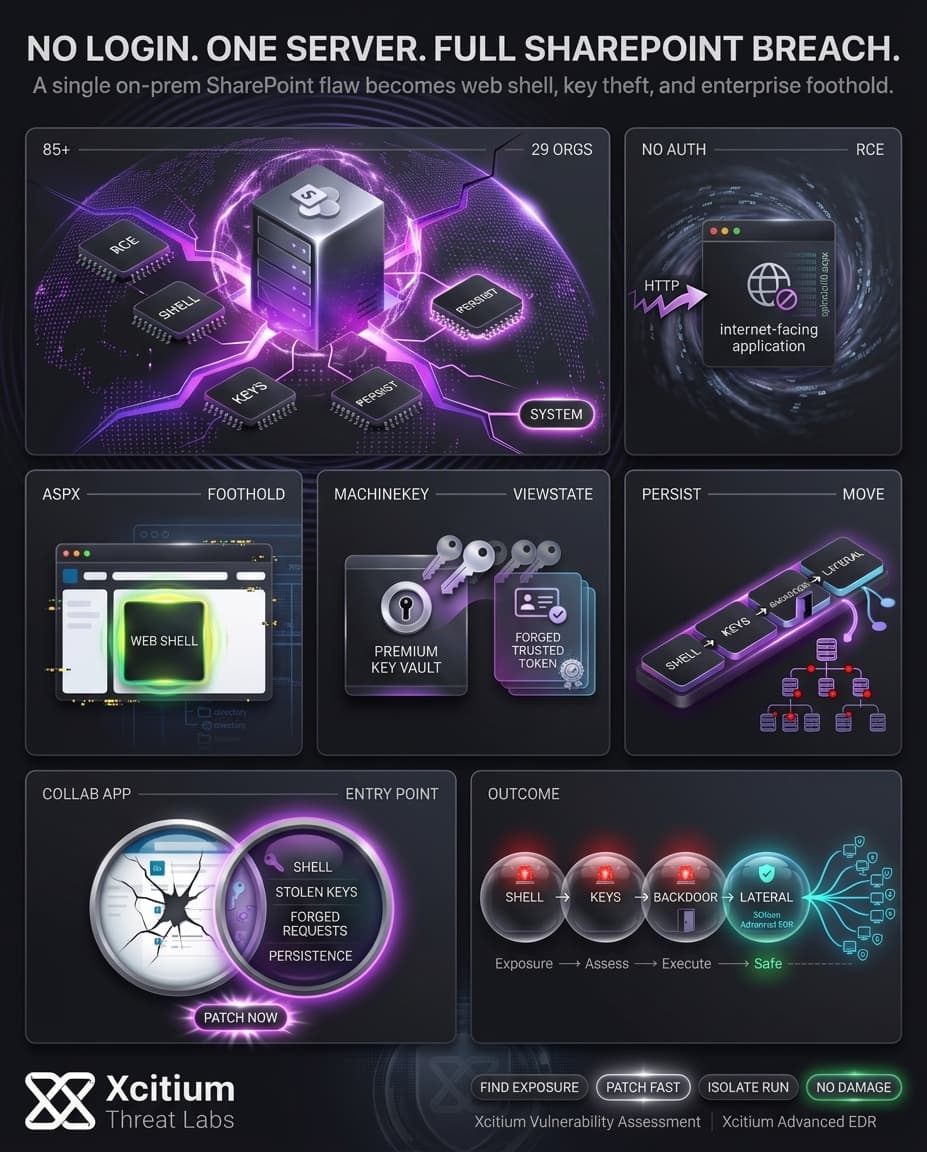
Attack Mechanics: Web Shell Deployment and Key Theft
Attackers usually perform an HTTP POST against the SharePoint application in order to upload an ASPX web shell, typically at /_layouts/15/ToolPane.aspx, such as spinstall0.aspx. The uploaded web shell is executed by the SharePoint application and performs actions according to the attacker’s inputs.
The shell collects the ASP.NET MachineKeys stored on the server and transmits them to the attackers. These keys allow the attacker to forge __VIEWSTATE tokens that will be accepted by the SharePoint application and cause it to run attacker-controlled commands.
Important stages of the attack chain are:
- Web Shell Upload: The exploit uses a malicious ASPX shell file, (spinstall0.aspx), to gain foothold within SharePoint.
- Machine Key Theft: The web shell collects ASP.NET MachineKeys that allow signing of ViewState.
- Forged ViewState Execution: With the keys, the attacker can create forged
__VIEWSTATEtokens causing the SharePoint application to execute malicious code. - Persistence & Lateral Movement: Upon exploitation, further web shells, additional backdoors, or scheduled tasks are placed on the target to maintain persistence and move laterally.
Scope and Impact: Global Targets Under Siege
The zero-day exploit is currently being used by hackers in a worldwide cyber attack campaign. The malicious web shell was already installed in at least 85 SharePoint servers that belong to 29 organizations.
- Global Spread: Exploit activity has been detected in North America, Europe, Africa and the Middle East.
- Victim Scale: Over 85 servers across 29 organizations have been identified as compromised.
This large-scale cyber attack campaign highlights how a single security flaw could expose various organizations around the world.
CISA Alert and Industry Response
Both U.S. authorities and business acted fast after discovering the zero-day. As a result, CISA added CVE-2025-53770 to its Known Exploited Vulnerabilities list on July 20, 2025, obliging U.S. federal government departments to install the fix before July 21, 2025. Microsoft issued emergency security updates for all supported on-premises SharePoint products on July 21, 2025.
- Emergency Updates: Microsoft provided cumulative fixes for SharePoint Server 2019, 2016, and Subscription Edition.
- Post-Patch Actions: The machine key rotation was advised and enabling of SharePoint’s AMSI module to scan malicious payloads in real-time.
All major sources agree that this SharePoint bug is actively exploited in the wild, meaning companies should protect their SharePoint servers now.
Conclusion: One Unpatched SharePoint Server Can Become an Enterprise Breach
This zero-day proves how dangerous internet-facing collaboration platforms become when a single flaw enables unauthenticated code execution. In this case, attackers did not need stolen credentials or user interaction. They only needed a vulnerable SharePoint server, then they could upload a web shell, steal machine keys, forge trusted ViewState data, and turn one exposed application into a long-term foothold.
Why This Threat Matters Now
The real danger is not just remote code execution. It is everything that follows once trust inside the application is broken.
- Web shell deployment creates instant server-level access
- Stolen machine keys allow attackers to forge trusted requests
- Persistence and lateral movement can begin before teams realize the server is compromised
- One vulnerable collaboration system can expose the wider enterprise
Where Xcitium Changes the Outcome
This kind of exposure requires two controls working together.
- Xcitium Vulnerability Assessment ensures this weakness should have been visible, by identifying exposed on-prem SharePoint systems and prioritizing urgent remediation before attackers find them
- Xcitium Advanced EDR ensures that even if exploitation is attempted, code can run without being able to cause damage, preventing follow-on malware, persistence, and destructive post-exploitation activity from turning into business impact
If you have Xcitium in place, this attack does not succeed the way the attacker needs.
Secure Collaboration Infrastructure Before It Becomes the Entry Point
Patch immediately. Rotate machine keys. Remove internet exposure where possible. Then enforce security that finds the weakness early and stops execution-based damage before it spreads.