Why The Instructure Data Breach Matters Now
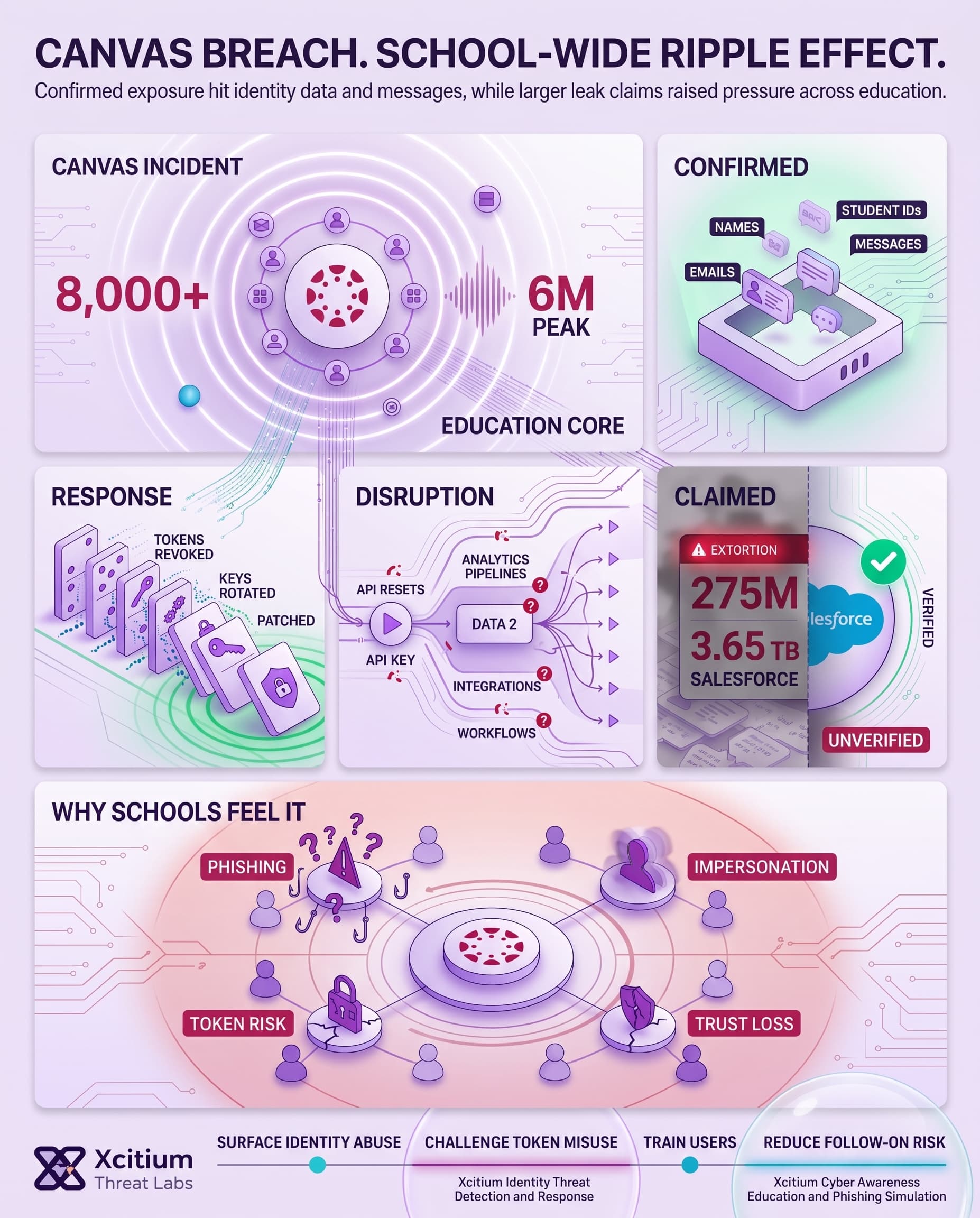
The Instructure data breach matters because Canvas sits at the center of day-to-day education, not at the edge of it. Instructure markets Canvas as the top LMS in North America, says it serves tens of millions of users, supports peak usage of 6 million concurrent users, and works with more than 8,000 institutions.
Meanwhile, the education sector already faces relentless pressure. The U.S. Department of Education says K-12 districts average five cyber incidents each week, while a UK survey from the Department for Science, Innovation and Technology found that 98% of higher education institutions and 88% of further education colleges identified breaches or attacks in the past year.
What Instructure Has Confirmed So Far
Instructure first disclosed a criminal cyber incident on May 1 and said a day later that, at that stage, it believed the incident had been contained. The company later confirmed that the exposed data included names, email addresses, student ID numbers, and messages among users. At the same time, it said it had found no evidence that passwords, dates of birth, government identifiers, or financial information were involved. Just as importantly, Instructure has not publicly disclosed how many institutions or individual users were affected. Therefore, the confirmed facts remain narrower than the leak-site narrative now surrounding the incident.
Confirmed response actions included:
- Revoking privileged credentials and access tokens
- Deploying patches and rotating certain keys
- Increasing monitoring and reissuing some application keys that required reauthorization
Why The Service Disruption Is Part Of The Story
This story is not only about stolen data. It is also about how quickly trust resets can ripple through a modern learning platform. Instructure’s status updates show maintenance affecting Canvas Data 2 as well as Beta and Test environments, while some customers saw limited disruption in tools that relied on API keys.
That detail matters because Canvas Data is positioned by Instructure as a source of raw, event-level data used for dashboards, advanced queries, and data warehouse integrations. Likewise, Canvas promotes more than 1,000 partners and integrations. So, when keys are reset, the impact can reach analytics pipelines, classroom tools, and administrative workflows at once.
Where The ShinyHunters Claim Goes Further
In contrast, the supposed extortion message takes the tale even farther than Instructure itself. The attacker alleges that almost 9,000 institutions and 275 million people have been affected; that billions of personal messages have been hacked; that Salesforce’s environment has been accessed; and that more than 3.65 TB of uncompressed data has been stolen.
It should be emphasized, however, that none of these statistics have been verified by Instructure. It is important to observe that the numbers are themselves already rather murky. In the very same news cycle, the attacker story makes mention of more than 240 million records being stolen. This distinction is significant because “people,” “records,” and “messages” are not equivalent measures.
What The Images Reveal About The Attack Playbook
In fact, the accompanying visual elements for this incident contain several important points to consider. First, one screenshot bears the brand marks of the Canvas application, promoting it as a reliable learning tool. Another screen displays the victimization card from a leak site bearing Instructure’s name, along with the ultimatum, huge cloud storage capacity, and blurred preview pane.
This combination points towards the typical ransomware extortion scheme. Prove your possession, hint at your sample accessibility, and build up pressure without making an immediate release of all information. Moreover, the mentioning of Salesforce also merits attention. Back in March, Salesforce announced that hackers have been leveraging overly permissive guest settings of their Experience Cloud to exploit CRM information without even authenticating themselves. Later, FINRA issued warnings against the exact same campaign pattern.
Why Exposed Messages Change The Stakes
The data that may be compromised could extend past identity-oriented directories to richer contextual information. According to how the institution will use this information, it may concern deadlines, behavior, support needs, accommodation, communication between students, or instructor feedback sessions. Hence, this event is not only about violating privacy; it may well turn out to be a case of exposure of information too.
Why Education Platforms Keep Attracting Attackers
Education technology systems are still desirable due to the combination of scale, identification information, communication capabilities, and operational dependencies that can be found there. The UK government survey conducted in 2025/2026 showed that over a quarter of further and higher education organizations suffered from data breaches and/or cyberattacks on a weekly basis.
In the U.S., the Department of Education outlines a consistent trend of recurring breaches at K-12 establishments. Meanwhile, this breach occurred despite Instructure’s September 2025 security update in which the company reported a social engineering attack conducted by an external party using a Salesforce environment; however, no data breaches related to its products occurred in this case.
Conclusion: When the Classroom Platform Becomes the Breach Surface
The Instructure incident shows why education platforms are now high-value targets. Canvas is not just a learning tool, it is the operational layer for students, instructors, administrators, analytics, integrations, and institutional communication. When that layer is disrupted or exposed, the impact moves far beyond email addresses and student IDs. It reaches trust, privacy, workflows, and the daily rhythm of education.
Why This Threat Matters
The confirmed exposure already includes names, email addresses, student ID numbers, and messages among users. That alone creates meaningful risk for phishing, impersonation, credential stuffing, and targeted scams against students and staff.
The unverified ShinyHunters claim goes much further, alleging massive data theft across institutions and messaging archives. Whether those numbers prove accurate or not, the pattern is clear. Attackers understand that education platforms hold both identity data and sensitive context.
Why Schools Stay Exposed
Education environments are difficult to defend because the ecosystem is large, distributed, and integration-heavy.
- Students, faculty, staff, vendors, and third-party tools all depend on access
- API keys and application tokens connect analytics, classroom tools, and administrative workflows
- Key resets can disrupt learning systems even while reducing risk
- Messages may reveal context that makes follow-up phishing more convincing
- Attackers can turn uncertainty itself into extortion pressure
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed the same way.
With Xcitium Identity Threat Detection and Response, abnormal identity behavior, suspicious token use, and risky access patterns can be surfaced before they become broad data exposure. With Xcitium Cyber Awareness Education and Phishing Simulation, students and staff become harder targets for the follow-up scams that usually arrive after education data leaks.
- Identity misuse is detected earlier
- Suspicious cloud and application access is challenged faster
- Users learn to recognize credential theft and impersonation attempts
- Attackers lose the ability to turn exposed education data into wider compromise
Protect Learning Environments Like Critical Infrastructure
Schools are no longer soft targets by accident. They are strategic targets by design. Secure the identities, tokens, integrations, and people that keep digital learning running.