Fresh reporting links the Lazarus Group to Medusa ransomware activity aimed at healthcare organizations in the United States. The main risk is not a single “new” ransomware strain. Instead, the reporting suggests a state-linked actor may be borrowing a proven ransomware-as-a-service ecosystem. That blend increases pressure on victims.
Why This Link Matters Beyond One Set of Victims
When a state-linked actor adopts a commercial ransomware operation, profit may be only part of the story. Extortion revenue can also fund other missions. Because of that, attackers may ignore informal “no hospitals” rules some crews claim to follow.
Federal prosecutors have described hospital-focused ransomware tied to North Korean operators. They said it caused real-world harm and disrupted patient care. Consequently, healthcare organizations must treat extortion as a safety and continuity issue.
How Investigators Connect Lazarus Activity to Medusa Operations
Attribution rarely comes from one clue. Instead, analysts look for patterns across malware, infrastructure, and behavior. In the reported cases, researchers saw some tools tied to Lazarus activity. They also saw widely available utilities used by many attackers. Commodity tools can blur the trail, yet custom implants can strengthen confidence.
The reported toolset maps to a familiar sequence:
- Persistent access tools that support repeat entry
- Remote-control malware for hands-on activity
- Password theft utilities used to expand access inside the network
- Proxying and transfer tools for moving stolen data
Still, Medusa’s affiliate model complicates certainty. In other words, the same ransomware brand can involve multiple “partners.” One actor may obtain access, while another deploys the encryptor.
What Medusa Ransomware Does
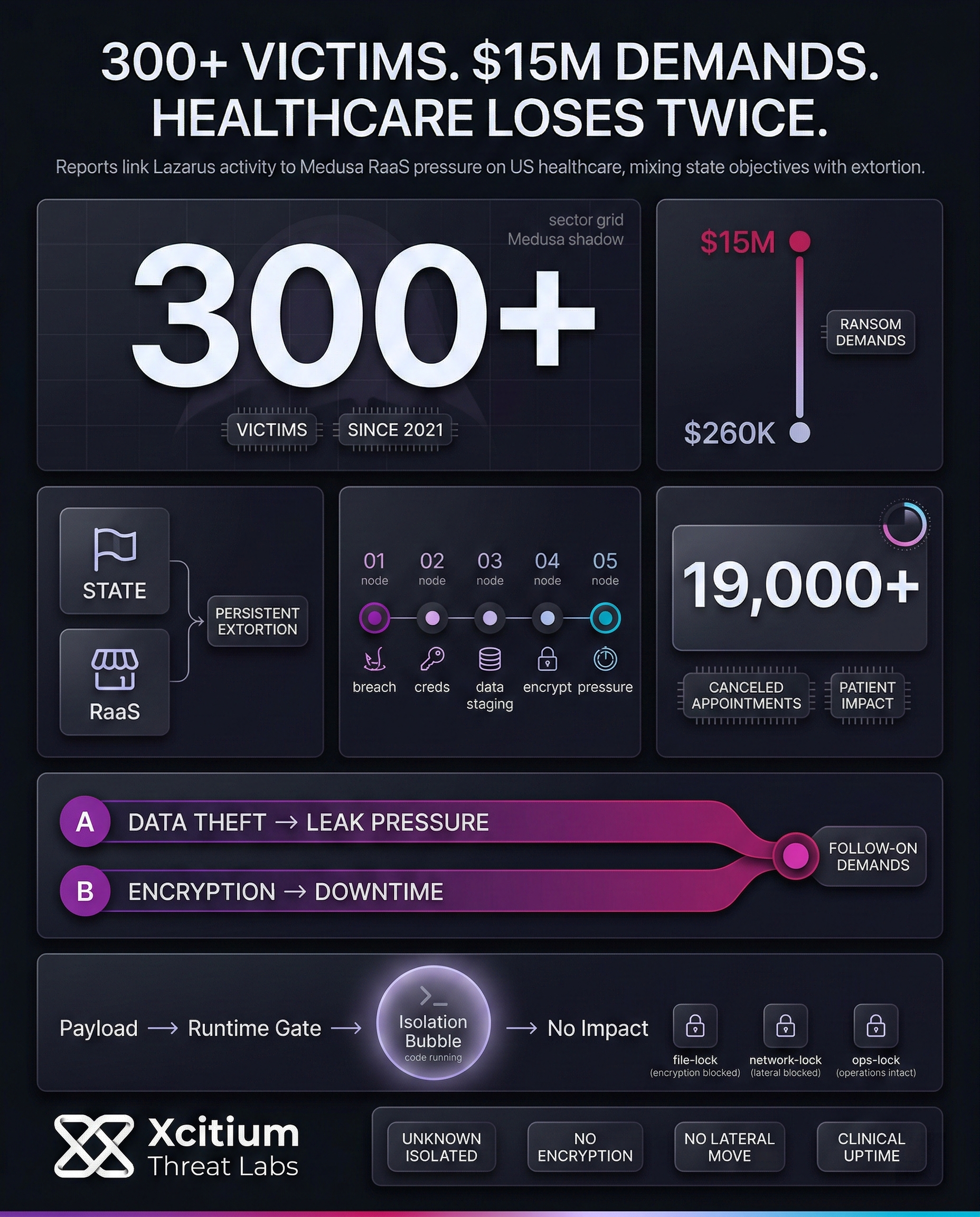
According to a joint advisory from various federal agencies, Medusa is ransomware-as-a-service that was first recognized in 2021 and has been linked to 300+ victims across various sectors.
It also points out the “double extortion” technique used by the attackers to steal data and encrypt the system and threaten to leak the information to extort money from the victims. It also points out that various threats have used the term “Medusa,” and this could be confusing when reporting threats.
Medusa’s leak site has been listing healthcare and nonprofit victims since late 2025, although affiliate programs have made attribution difficult.
Generally, the process involves the following five steps:
- Breaking in via phishing or through an unpatched, exposed system
- Stealing credentials, expanding access inside the network
- Uploading stolen data to create leverage during negotiations
- Encrypting the systems to create downtime
- Escalating the pressure via leak site deadlines, direct communication, etc.
It is interesting to note that the advisory also points to situations where the victim had to face further demands after the initial payment. This shows that the payment of the ransom does not necessarily mean that the hacker will not come back.
Why Healthcare Remains a High-Pressure Target
Healthcare combines high urgency with complex technology. Legacy devices still exist. Meanwhile, staffing constraints can slow security work. As a result, attackers may believe downtime will force rapid decisions.
History shows how quickly this becomes operational impact. During the WannaCry incident affecting the United Kingdom’s health system, national auditors reported thousands of canceled appointments. They estimated the total above 19,000. They also documented wide disruption across health organizations. Importantly, auditors described the event as preventable with basic security practices.
Practical Steps That Reduce Medusa-Style Ransomware Risk
Layered basics make attacks harder, slower, and easier to contain. Prioritize the actions most connected to real intrusions:
- Patch internet-facing systems quickly, especially remote access and management services
- Use multi-factor authentication for remote access and privileged actions
- Segment networks so one breach cannot reach backups or clinical systems
- Maintain offline or immutable backups, and test restores regularly
- Limit admin privileges and watch for unusual account behavior
- Rehearse an isolation-and-recovery plan with IT, leadership, and clinical operations
Also, plan for the economics. Reported Medusa demands can reach $15 million. In the observed cases highlighted by researchers, the average demand ran around $260,000. Because negotiations often include data-leak pressure, coordinated legal and communications planning matters as much as patching.
Signals To Watch as State-Linked Ransomware Evolves
First, the tool-sharing between state actors and criminal organizations will increase. This model will make the attacks faster, but attribution will be difficult. Secondly, the access market will be monitored. If credentials are leaked, multiple attackers will hit the same industry.
Lastly, the extortion model, with less focus on encryption, will be monitored. Data theft, harassment, and repeated extortions will increase. This will be seen when the victimized organization needs to keep their service online.
Conclusion: When State Pressure Meets RaaS Extortion, Healthcare Loses Twice
The reported Lazarus and Medusa connection matters because it changes the incentives. When a state linked actor borrows a proven ransomware as a service ecosystem, extortion can become both revenue and pressure. That blend increases persistence, increases risk tolerance, and weakens any assumption that hospitals will be spared.
Why This Threat Is Bigger Than One Ransomware Brand
Medusa is already linked to 300+ victims since 2021, and uses double extortion as a default model, steal data first, then encrypt, then threaten leaks. The advisory also notes that victims can face further demands even after paying, which means the ransom is not an exit strategy.
Why Healthcare Remains the Highest Leverage Target
Healthcare combines urgent uptime with complex and legacy technology. Downtime becomes patient impact, and attackers know that pressure shortens decision cycles. The post highlights the real operational cost seen in prior healthcare disruption events, including more than 19,000 canceled appointments reported in the UK during WannaCry.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
With Xcitium Advanced EDR in place, ransomware execution loses its leverage.
- Unknown payloads are isolated at runtime
- Code can run without being able to cause damage
- Encryption cannot touch real systems or clinical operations
- Lateral movement and follow on disruption fail to establish
Treat Ransomware as a Safety Issue, Not an IT Issue
Healthcare must prioritize the controls that reduce intrusion speed and reduce blast radius, patch exposed services, enforce MFA, segment networks, test offline backups, and rehearse isolation and recovery. Then enforce execution time protection so extortion pressure cannot become downtime.