New OAuth Phishing Attack Exploits Authentication Trust
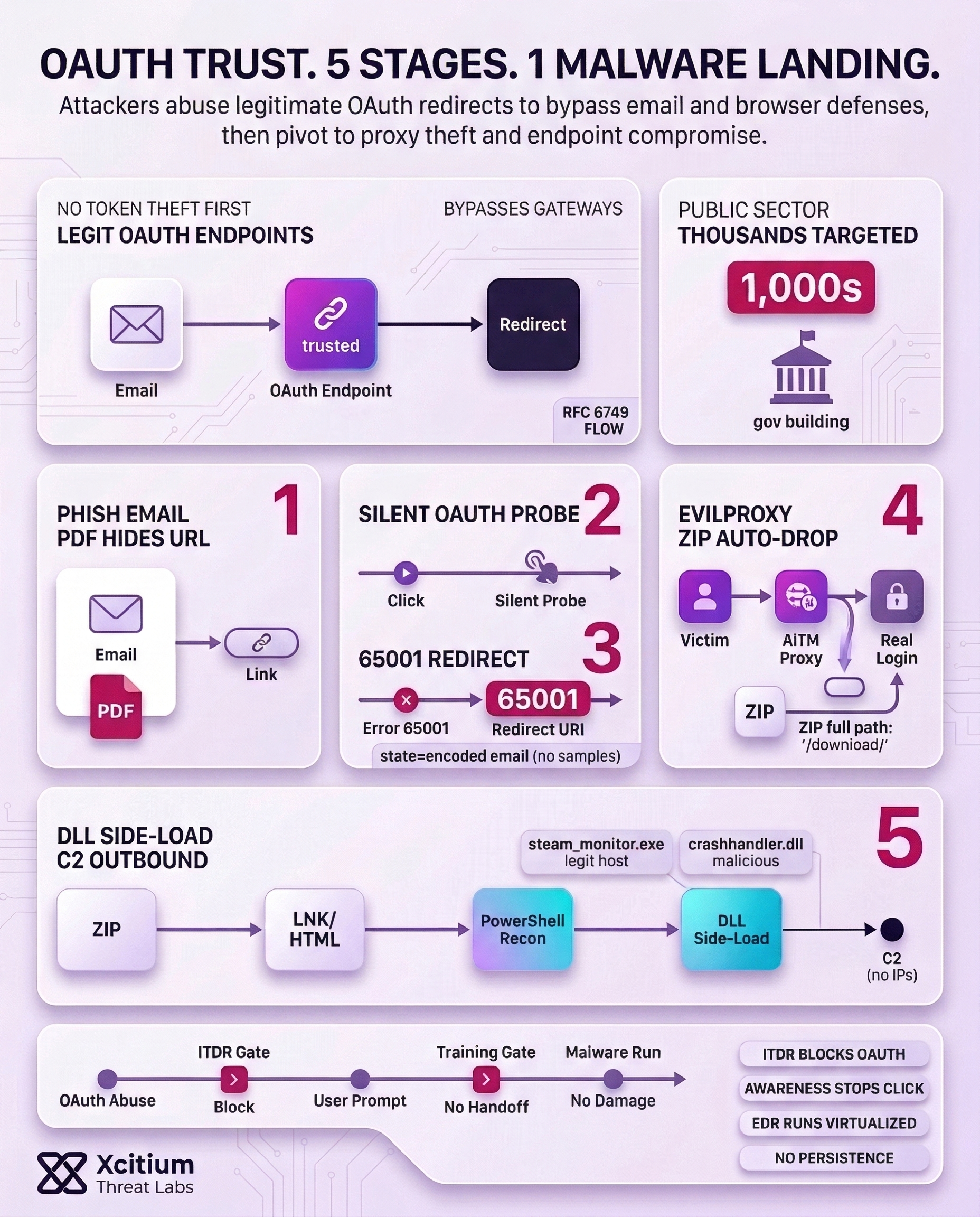
A new sophisticated phishing attack has been identified that utilizes the legitimate redirect functionality of the OAuth protocol for malicious purposes. This attack differs from other attack vectors in that it evades email gatekeepers as well as the security measures of browsers without engaging in token theft. The attackers target government and public sector entities by using domains associated with legitimate identity providers.
The attack utilizes the standard error handling provided by the OAuth mechanism described in RFC 6749. Attackers can create malicious applications, set redirect URIs that point to their domains, and spread carefully crafted phishing links. The users are unaware of the attack until the malware is deployed on their systems.
How the Five-Stage Attack Chain Works
Stage 1 – Deceptive Email Delivery
Threat actors send phishing emails containing e-signatures, notifications about Social Security, Teams meetings, and financial documents. Additionally, phishing campaigns have been noted to embed OAuth redirect URLs within the content of the phishing emails and also hide them in PDF attachments for stealthier operations. Mass emailing tools created using Python and Node.js, along with cloud-based virtual machines, have been utilized to conduct phishing on thousands of users.
Stage 2 – Silent OAuth Probe Executes
Upon clicking the phishing link, an OAuth authorization process is initiated. In this process, the state parameter is used to send the encoded email address of the recipient in plaintext, hexadecimal, Base64, or any custom encoding scheme. Hence, the email address is populated on the phishing page automatically. This is a hidden request to check if the account exists for the attacker.
Stage 3 – OAuth Error Redirect Confirms Vulnerability
However, when silent authentication is not successful, Entra ID returns an error code of 65001 (interaction_required) and redirects the browser to the attacker’s registered URI. This again emphasizes the requirement for interactive MFA. The attackers gain valuable intelligence about the state of account security even when tokens are not compromised.
Stage 4 – Malware Delivery via Proxy Framework
After a redirect attack, a victim is presented with a phishing framework such as EvilProxy. This is an attacker-in-the-middle tool used to steal credentials and session cookies. In targeted attacks, a ZIP file is automatically downloaded via a /download/XXXX path. This ZIP file contains LNK shortcut files and HTML smuggled loaders used for code execution.
Stage 5 – Endpoint Persistence Through DLL Side-Loading
The extraction of the ZIP archive executes a PowerShell sequence of commands that performs host reconnaissance (ipconfig /all, tasklist, etc.). Next, DLL side loading occurs through a legitimate steam_monitor.exe executable. The malicious crashhandler.dll file decrypts the payload in memory and establishes an outbound C2 connection to maintain control.
Why Traditional Defenses Fail Against This Attack
In addition, email filters usually filter out credential-stealing phishing attacks. The technique, however, first directs the victim to legitimate OAuth endpoints, and email filters will likely misclassify the first request as non-malicious. The attack takes advantage of the trust relationships that are inherent in authentication protocols.
Some factors that make the vulnerability possible are discussed below:
- DLL side-loading avoids endpoint detection systems
- OAuth Redirects are legitimate-looking to email gateways
- Silent authentication requests do not trigger user warnings
- Error messages reveal account security status
- Proxy frameworks capture credentials after the redirect
Effective Mitigation Strategies for Organizations
Microsoft recommends that organizations implement the following defensive measures:
- Monitor Redirect URIs: Monitor new registrations and unusual redirect URIs, and implement OAuth applications with unusual permission requests.
- Restrict User Consent: Enforce administrative consent policies for OAuth applications, which will restrict users from granting unknown applications consent without approval from IT.
- Audit OAuth Registrations: Remove unused, overprivileged, or unrecognized OAuth app registrations. Document legitimate applications and their required permissions.
- Enable Conditional Access: Organizations can implement identity protection and conditional access policies. Unusual sign-in activity should prompt additional verification.
- Deploy Cross-Domain XDR: Organizations can implement extended detection and response (XDR) that provides visibility into coordinated attack attempts across the security infrastructure.
The Broader Security Implications
As organizations improve multi-factor authentication (MFA) and credential defenses, attackers are shifting to take advantage of trust relationships inherent in authentication protocols. For instance, Microsoft has already taken down malicious OAuth applications; however, OAuth abuse activities associated with it are still being detected.
This attack embodies one of the most important lessons: security measures should be beyond passwords and tokens. Authentication protocols should be monitored under formal processes. In addition, user awareness should be trained to incorporate OAuth authorization requests and suspicious redirect attacks.
For organizations that solely depend on traditional phishing protection measures, the risks are enormous. Therefore, it becomes necessary to incorporate a complete identity security strategy. The union between OAuth abuse and malware delivery poses a major threat that needs to be addressed through robust defense mechanisms.
Conclusion: When Trust Becomes the Delivery Mechanism
This OAuth phishing chain shows a strategic shift in modern intrusion. The attacker does not start by stealing tokens. They start by abusing OAuth trust, using legitimate identity provider endpoints and redirect behavior to bypass email and browser defenses, then pivoting into credential capture and malware delivery.
Why This Threat Matters
The five-stage flow is designed to look normal until it is too late.
- OAuth probes confirm account security posture through error-driven redirects, even without token theft
- Proxy frameworks like EvilProxy can capture credentials and session cookies after the redirect
- ZIP delivery and shortcut based loaders move the attack from identity to endpoint compromise
Why Traditional Defenses Keep Missing It
This attack wins by hiding behind what defenders trust.
- Email gateways see legitimate OAuth URLs and let them pass
- Silent authentication requests do not trigger user warnings
- Redirect URIs and error flows leak intelligence about account state
- DLL side-loading and smuggling tactics reduce file-based detection value
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
- Xcitium ITDR detects and blocks abnormal identity behavior and risky OAuth patterns before access becomes a session takeover.
- Xcitium Cyber Awareness Education and Phishing Simulation trains users to treat OAuth consent prompts and redirect-driven login flows as high-risk events, stopping the click and the credential handoff.
- Xcitium Advanced EDR ensures that if malware is delivered, code can run without being able to cause damage, so the endpoint stage never becomes persistence or control.
Secure OAuth Like Critical Infrastructure
OAuth is now an attack surface. Monitor redirect URIs, restrict user consent, audit app registrations, and harden identity sessions. Then enforce prevention at execution, so trust cannot be weaponized into compromise.