High-severity flaw found in Docker Engine (CVE-2026-34040), where attackers may bypass container...

Recently, a joint alert was released by several agencies including FBI, CISA, and NSA, among...

Lightning-Fast Ransomware Breaches Storm-1175 is a Chinese cybercriminal group behind Medusa...

Recently, it was officially reported by the FBI that their internal wiretap network was breached...
Phishing attacks have been initiated against LinkedIn, wherein the perpetrators have targeted...
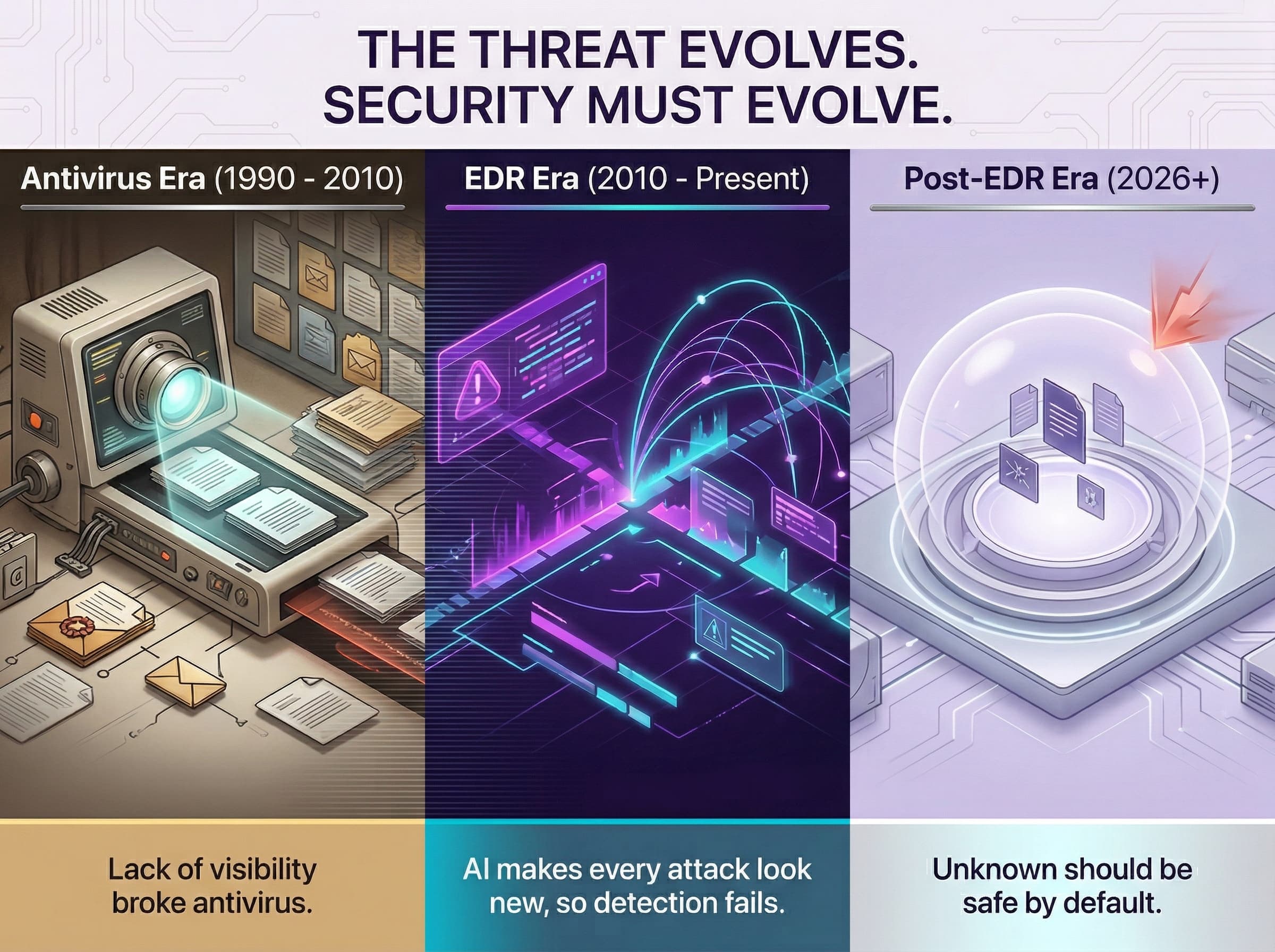
Endpoint security has evolved significantly over the last 30 years. The earliest antivirus systems...

The EvilTokens approach is taking the Microsoft device code phishing into a more ‘productized’...

One of the most popular HTTP client libraries in use, Axios, with more than 100 million weekly...

Why This DeepLoad Campaign Stands Out DeepLoad is a newly observed malware loader that shows a...