A Silent Security Failure at PayPal
Recently, PayPal confirmed its data breach and its impact on its customers. This data breach occurred when there was a software glitch in PayPal Working Capital (PPWC) loan applications.
As a result of this glitch, unauthorized users were able to access customers’ personal information from July 1, 2025, through December 13, 2025.
Although PayPal identified it on December 12, 2025, the length of time that customers were exposed to this data breach sparks concern about automated monitoring systems. Another concern from this data breach is that small business owners are exposed to serious privacy risks due to minor coding mistakes.
Understanding the Root Cause of the Exposure
Many people assume that every data leak involves a sophisticated hacker bypass. However, this specific incident was the result of an internal coding mistake rather than a direct system compromise.
PayPal officials stated that a code change in the PPWC application inadvertently made private files visible to unauthorized users. Therefore, the core PayPal infrastructure remained secure while this specific portal leaked data.
This distinction is crucial because it demonstrates that internal quality assurance is just as vital as external firewalls. For example, a single line of incorrect code can bypass years of security investment.
What Kind of Data Was Actually Stolen?
The sensitivity of the information that was exposed makes this particular data breach very concerning for the individuals who are affected.
This is because the hackers who gained unauthorized access to the information may be able to view a variety of personally identifiable information (PII) that was included in the leak.
PAYPAL DATA LEAK
The inclusion of Social Security Numbers in this leak drastically elevates identity theft risks. PayPal has initiated aggressive measures to contain damage and provide specialized protection to all affected account holders.
Because the Social Security Numbers were included in the leak, the chances of identity theft are much higher than they would have been in any other data breach scenario.
This is why PayPal is taking very aggressive measures to reduce the potential damage that may be done to the individuals who are affected.
How PayPal Responded to the Security Incident
Once the security team identified the error on December 12, they moved quickly to resolve the vulnerability. They rolled back the faulty code within twenty-four hours to prevent further data scraping.
In addition, PayPal has already reset passwords for every account that was potentially compromised. The company detected a small number of unauthorized transactions and has issued full refunds to those victims.
This proactive financial response helps maintain user trust, yet the long exposure period remains a point of contention for many security analysts.
Protecting Your Identity After a Major Leak
If you are among the approximately 100 customers affected by this specific leak, you must take immediate action. PayPal is currently offering two years of free credit monitoring through Equifax to help spot suspicious activity.
You should enroll in this service before the June 30, 2026, deadline to ensure your financial health. Additionally, all users are advised by experts to ensure that they enable 2FA on their accounts.
It is more secure to use a dedicated authenticator app rather than SMS codes. Thus, it becomes much more difficult for criminals to use the leaked information.
Lessons Learned from PayPal’s Recent Security History
This is not the first time the fintech giant has been in the news for its data protection standards. The company was hit by a credential stuffing attack in early 2023, where more than 35,000 accounts were breached within a few days.
Later, in January 2025, the company paid a settlement of $2 million to the New York State government for not adhering to the cybersecurity standards set by the government.
Thus, it can be said that the company’s perfect record in cybersecurity, as seen in the 2026 attack, is a constant battle for the company, and companies must ensure timely code auditing and threat detection mechanisms to avoid such long-term vulnerabilities in the future.
Actionable Steps for All PayPal Users
However, even if you haven’t gotten a breach notification letter, you should still maintain good digital habits. First of all, change your password to a unique, complex string that you haven’t used elsewhere.
In addition, you should frequently check your transaction history for unknown transactions, even if they are small. This is because thieves may use small “micro-transactions” to test stolen accounts before making larger unauthorized transactions.
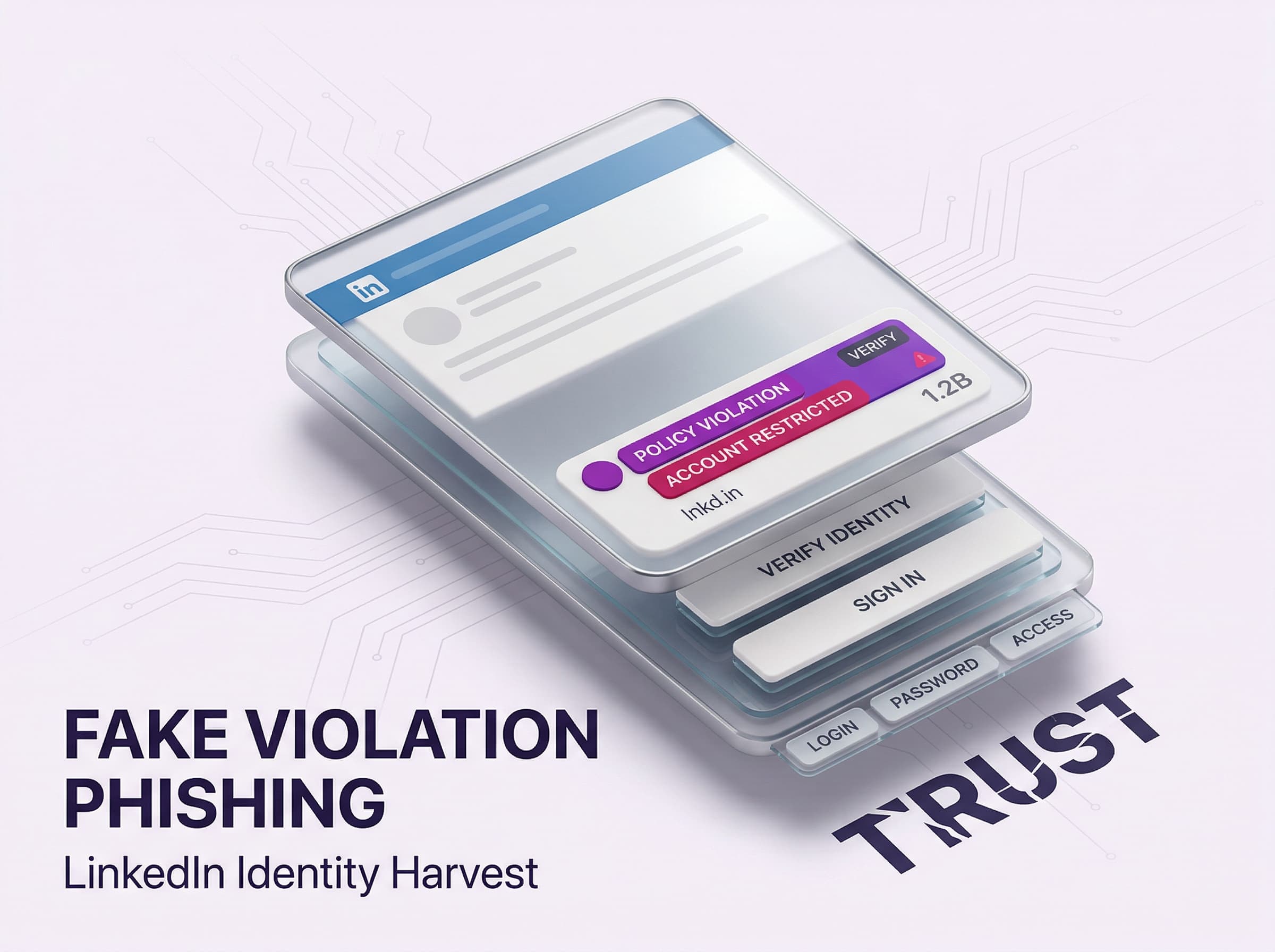
Finally, you should be careful about phishing emails claiming your account has been locked. Always go to the PayPal website directly instead of following a link in an email.
Conclusion: Six Months of Exposure Becomes Years of Identity Risk
The PayPal Working Capital incident shows how a simple internal coding mistake can create a high-impact privacy failure. For six months, unauthorized users could access sensitive customer files, including Social Security numbers, names, contact details, and dates of birth. Once this type of data is exposed, the risk does not end when the bug is fixed, it shifts into long-term identity fraud and targeted scams.
Why This Threat Hits Hard
This dataset is valuable because it enables high-confidence impersonation and financial abuse.
- Social Security numbers drastically elevate identity theft risk
- Attackers can combine personal and financial context to craft convincing follow-up phishing
- Fraud often begins with small “micro-transactions” to test access before larger theft
Why Organizations Stay Exposed
This breach was not driven by advanced exploitation, it was driven by visibility gaps and delayed detection.
- A code change made private files visible to unauthorized users
- The exposure lasted from July 1, 2025 to December 13, 2025, despite discovery on December 12
- Long exposure windows create a larger opportunity for scraping and downstream abuse
Secure the Identity Layer After the Breach
You cannot recall exposed SSNs, but you can stop what attackers try to do with them next. Treat identity as the primary perimeter, and enforce controls that respond in real time.