Massive Cyber Breach Strikes Medical Giant Stryker
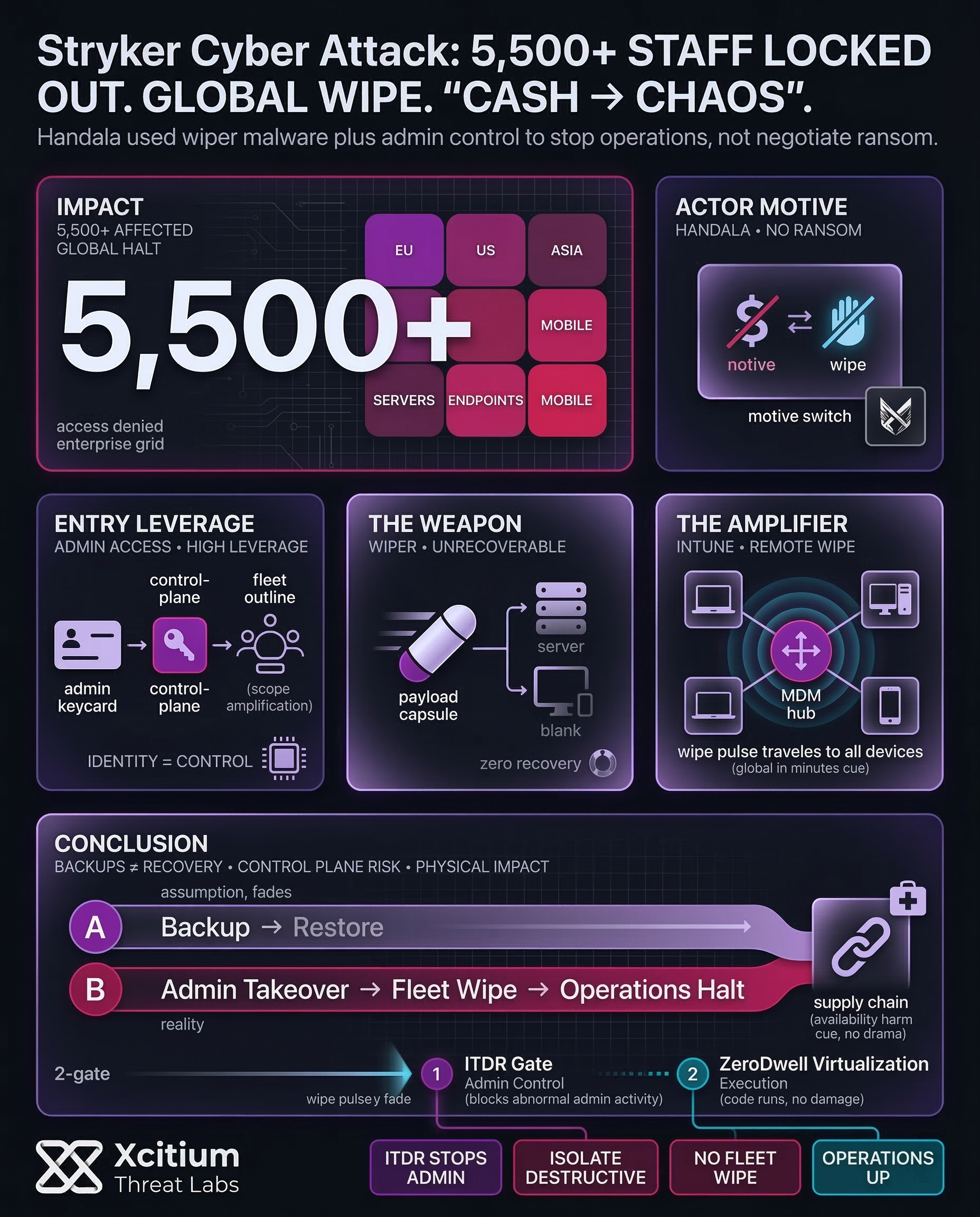
On March 11, 2026, Stryker, which is considered one of the most important international players in the medical technology field, was the target of a substantial cyberattack that influenced its information technology infrastructure. Thousands of its employees were denied access to critical systems.
Though the main target of the attack was the company’s headquarters in Cork, Ireland, the attack was also reflected in its facilities in Europe, Asia, and the United States. Initial findings indicate that the attack was not meant for demanding ransomware payments; rather, the attackers sought the complete destruction of the company’s data.
Handala Hacktivists Claim Responsibility for System Wipe
The destructive cyber attack has been traced by cybersecurity experts to a group identified as Handala. This is a Palestinian hacktivist group with strong ties to the Iranian regime. This is different from other cybercriminal groups, who are primarily interested in extortion ransoms.
The group did not demand a ransom. Instead, they used powerful wiper malware to delete corporate data. When the cybercriminals carried out the attack, they used administrative accounts to get access. They also went ahead and tampered with the system’s login page with their signature logo. Therefore, the impact on the employees was tremendous.
Sophisticated Wiper Malware Erases Critical Corporate Data
The attackers used a special payload intended to ensure complete unrecoverability of the information. It attacked both central servers and endpoint devices. Consequently, work computers and personal phones with corporate profiles were completely erased. Such a degree of destruction is rarely seen in a corporate environment.
The attack affected Intune-managed devices across the globe. It means that the entire digital infrastructure of the company came to a complete stop. Currently, the IT team and Microsoft engineers are working hard to determine the extent of the destruction. First and foremost, they are trying to find the point of entry.
Stryker Global Infrastructure Attack
Analysis of the coordinated cyber assault that paralyzed a medical technology giant and halted global operations.
Professional ideologically-motivated collective. Focused on data destruction and digital sabotage over financial gain.
Custom software designed for irreversible data wiping. Systematically cleared central servers and mission-critical endpoints.
Robotic surgery and orthopedic production lines were completely halted. Thousands of staff lost access to enterprise systems.
ALERT: REMOTE MOBILE DEVICE WIPES AND SYSTEM INTERFACE ALTERATIONS DETECTED
Global Operations Halted by Destructive Digital Warfare
The effect on Stryker’s daily manufacturing activities and engineering has been tremendous. In Ireland alone, more than 5,500 employees could not perform their work. The major technology centers suffered a complete stoppage of product design activities. As a result, experts are concerned about the worldwide supply chain for vital medical products. Since Stryker supplies critical hospital products, a complete stoppage could result in a crisis for patients worldwide. For example, surgical robots and orthopedic devices are manufactured by Stryker. The following is a summary of major technical impacts observed during the breach:
- Permanent erasure of data on all Intune-managed hardware.
- Complete shutdown of proprietary applications and corporate servers.
- Remote wiping of mobile devices linked to company email accounts.
- Defacement of internal login screens with political messaging.
Real-World Implications for the Healthcare Supply Chain
The role of Stryker in the global healthcare ecosystem is enormous. Hence, the disruption of such a scale creates a massive bottleneck. Hospitals require a continuous supply of medical equipment for surgeries. If the supply chain is disrupted, the outcome may not be favorable for the patient.
In addition, the destruction of engineering data may cause a delay in the release of new technology that may save lives. Therefore, the healthcare sector must consider this attack a turning point. It shows that cyber warfare may cause physical harm to the availability of healthcare.
Analyzing the Shift Toward Destructive Cyber Attacks
More and more groups are opting to engage in destruction rather than financial gain. The use of wiper malware is a manifestation of a new trend that is state-sponsored economic disruption. It is important to rethink the approach that is being used for backups as well as recovery.
In fact, having backups is not enough; it is also important to consider that the system that is being used for deployment could be compromised. In this case, the Stryker breach is a wake-up call to the entire medical technology world. In fact, it shows that the new objective of attackers is chaos instead of cash.
Conclusion: When the Goal Is Destruction, Recovery Becomes the Battlefield
The Stryker incident shows a shift from cash to chaos. This was not an extortion play, it was a destructive breach that denied thousands of staff access, disrupted global operations, and aimed to erase corporate data across servers and Intune-managed devices.
Why This Threat Changes the Stakes
Wiper campaigns target the one capability every enterprise assumes it will always have, recovery.
- Administrative access becomes the weapon, attackers can disable defenders and trigger irreversible actions at scale.
- Centralized management amplifies impact, Intune-managed fleets can be disrupted globally in minutes.
- Manufacturing and healthcare supply chains feel the blast radius immediately, downtime becomes real-world harm.
Why Organizations Are Vulnerable
Destructive attacks succeed when identity and control planes are trusted by default.
- Admin accounts are the highest leverage asset in the environment.
- Device management platforms are designed for speed, the same speed attackers exploit once inside.
- Visibility collapses fast when systems are wiped, response becomes reactive and incomplete.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed as an enterprise-wide destructive event.
- Xcitium ITDR helps stop the takeover of administrative identity, detecting and blocking abnormal admin activity before it becomes fleet-level control.
- Xcitium Advanced EDR, powered by Xcitium’s patented Zero-Dwell platform, stops destructive payload execution on endpoints and servers. Code can run without being able to cause damage, which breaks the wipe chain before operations collapse.
Build for Destruction, Not Just Disruption
Wipers do not negotiate. Resilience requires hardened admin identity, segmented management planes, tested offline recovery paths, and execution-time controls that prevent destructive code from becoming irreversible impact.