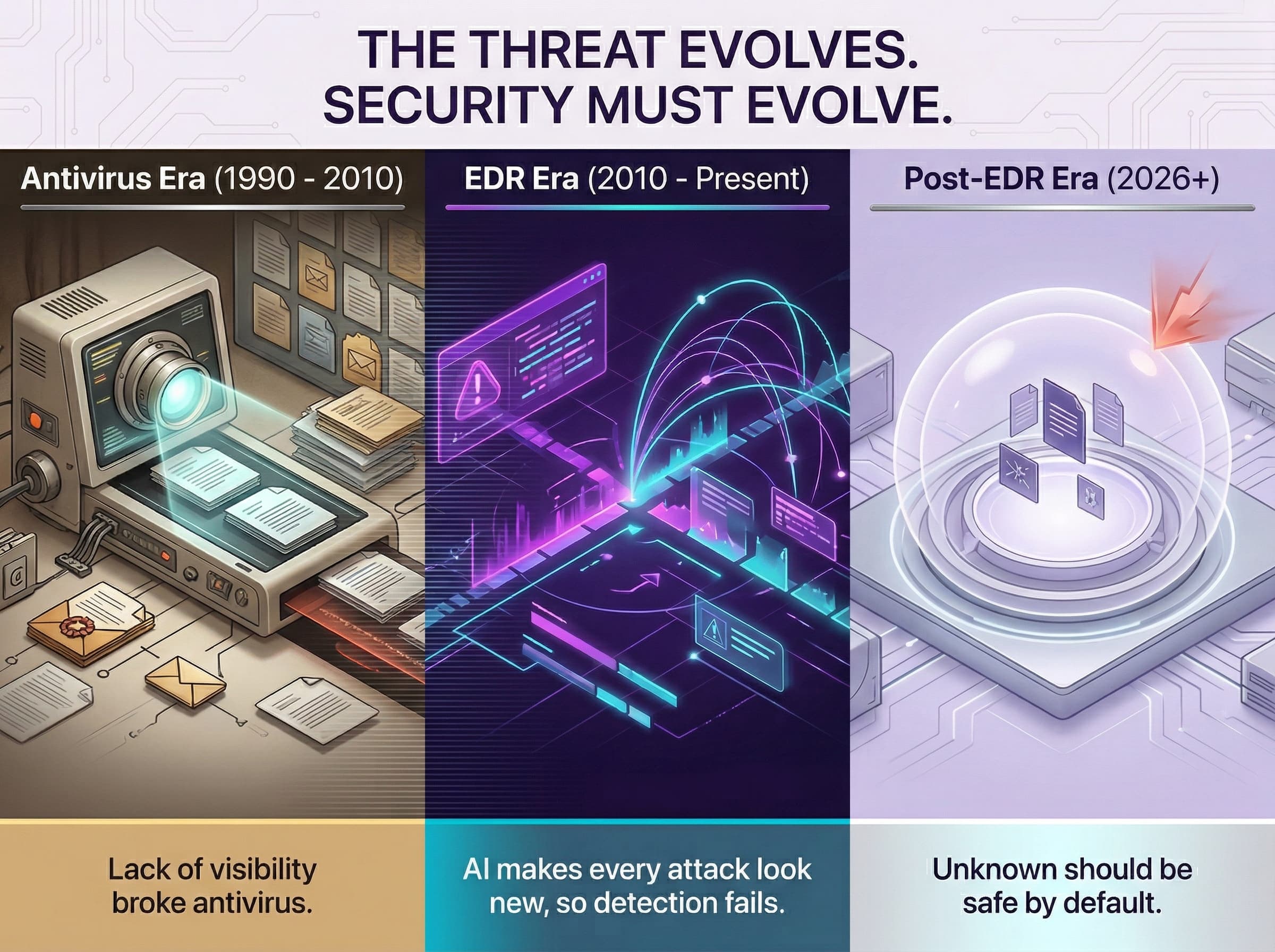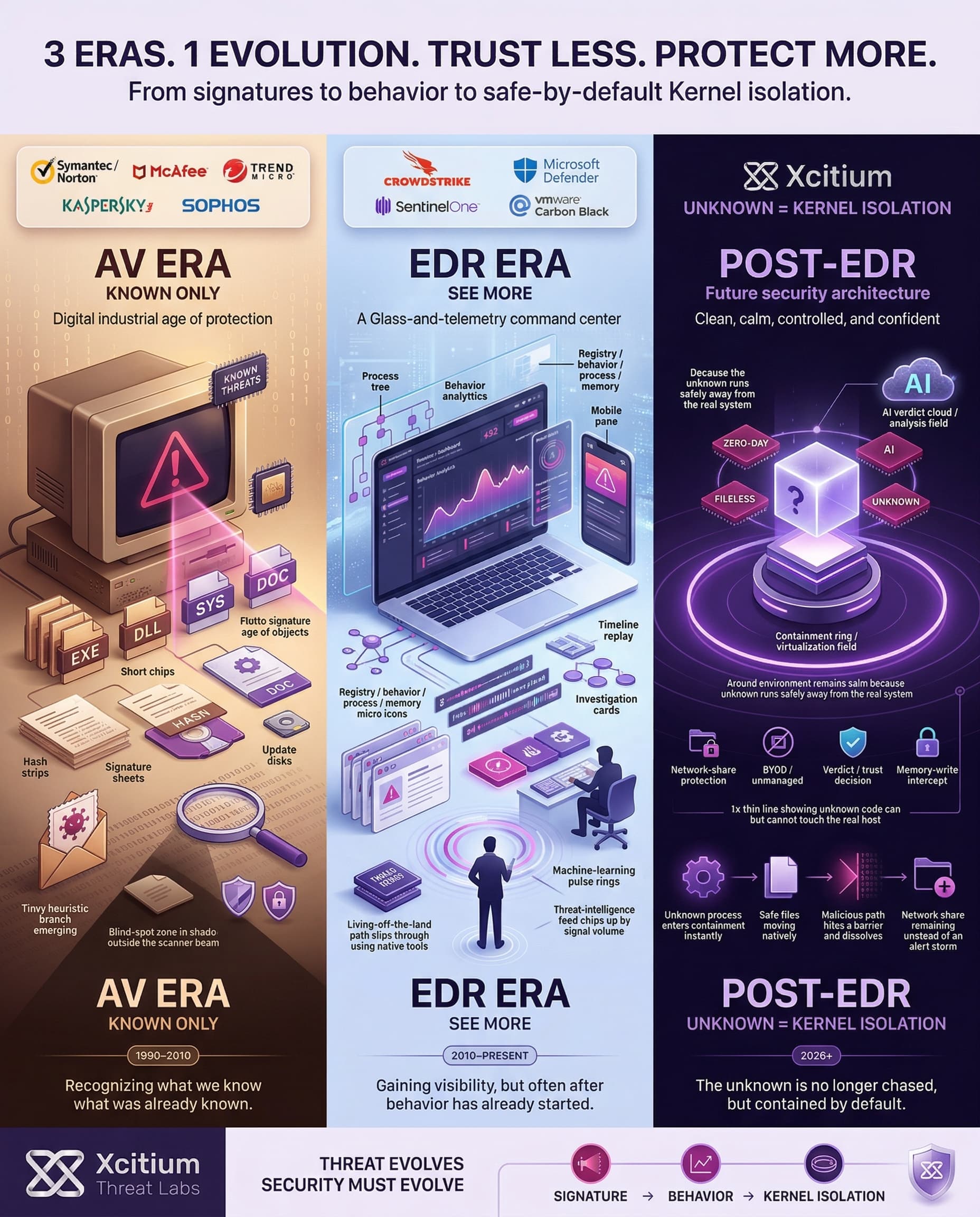
Endpoint security has evolved significantly over the last 30 years. The earliest antivirus systems used signature scanning to detect malicious files, while later EDR software enhanced security through behavioral detection that offered alerts when an attack was underway. Although these were significant improvements back then, they fail to deliver adequate protection against the rapidly evolving nature of today’s threats, such as machine learning attacks, fileless malware, and zero-day exploits.
Recognizing these limitations, Xcitium defines the Post-EDR Era, where traditional detection is no longer enough. In this era, our technology goes beyond “detect and respond” by implementing kernel-level virtualization (Layer 1) to safely isolate unknown executables and network share protection (Layer 2) to prevent malicious encryption or data corruption. This proactive approach ensures threats are neutralized before they can cause damage, offering a level of endpoint security unmatched by legacy AV or modern EDR solutions.
Antivirus Era (1990–2010)
The first line of defense for the computer was early antivirus software. It worked by scanning files for malware using a signature database. If a match was found, the malware was blocked.
During this era, there were many antivirus companies being utilized for consumers and businesses alike. These included Symantec (Norton Antivirus), McAfee, Trend Micro, Kaspersky, and Sophos. The techniques they used mainly involved using file and email signatures to detect malicious software. Although they were the norm at that time, they heavily depended on signature databases; therefore, any changes made to existing malware would go undetected until an update was installed.
The problem with signature-based malware detection is that new or modified malware will not match any signature until the signature database is updated. This means that unknown malware, zero-day attacks, brand-new ransomware, etc., will not be detected. Signature AV also provides very limited real-time information. It only alerts the user after the malware has been identified.
However, in the latter years of this period, some antivirus products began to use heuristic analysis and behavioral detection to try to identify new threats. The analysis would look for file properties or behavior that was considered suspicious even when there was no known signature of the threat. Some early versions of rootkit and macro virus detection technologies were also developed as malware targets shifted towards Microsoft Office files. However, such technologies were still unreliable, sometimes resulting in false alarms.
In other words, the signature database must be updated continuously. If malware is not recognized in the signature database as is the case with new malware, new malware variants, fileless malware, or malware based on credential attacks it will not be detected. Signature-based malware detection was not enough in the late 2000s.
EDR Era (2010–Present)
Around 2010, security companies started using Endpoint Detection and Response (EDR) platforms to address the limitations of AV. Unlike AV, EDR monitors endpoint processes, network connections, registry changes, and other system activities. It analyzes the activities using behavioral analysis, machine learning, and threat intelligence. When EDR sees unusual behavior (for example, a process injecting into another process or modifying many files), it raises an alert and often provides a timeline of the incident. Many EDR tools even automate responses like isolating the endpoint or killing a process.
Several EDR vendors, such as CrowdStrike, SentinelOne, Microsoft Defender for Endpoint, and VMware Carbon Black, were widely deployed in enterprise environments during this era. Such technologies utilized advanced methods and performed additional monitoring of endpoint processes, network activity, registry, and behavior. The combination of behavioral analysis, intelligence feeds, and machine learning was used for detecting sophisticated activities and attacks. Nevertheless, EDR required some human intervention for managing alerts and handling incidents. The development of malware and attacks proved that EDR alone was no longer sufficient to address the current challenges of cybersecurity.
EDR introduced many significant changes. EDR can now identify new threats that do not have a signature. It can give a better view of the incident and speed up the investigation.
However, EDR has its own disadvantages. To begin with, EDR is a reactive system. A file or a program has to start misbehaving or behave like a known malware for the EDR system to kick in. By the time the EDR system is activated, the attacker could have done a lot of damage. In addition, modern EDR products produce a massive amount of alerts. Every anomaly, no matter how small, on the endpoint device will produce a corresponding alert. In effect, the security analyst will experience a state of “alert fatigue.” A lot of human intervention is required to manage the flood of alerts generated by the EDR system.
Finally, sophisticated attackers are evading the EDR system. Many attackers are using fileless attacks. In addition, they are using living-off-the-land attacks. They are flying under the radar. In a recent attack on a credit bureau, the attackers used a third-party application. The application was not detected by the EDR system. In a word, the EDR system failed.
2026 and Beyond: The Post-EDR Era
Today’s threat landscape has exploded in complexity. Attackers leverage new technologies and tactics that outpace “detect and respond” defenses:
- AI and Automated Attacks. 2025 witnessed the advent of real AI-driven attacks. Cybercriminals are now using AI to automate all hacking activities from reconnaissance to exploit development without or with little involvement of a human. The AI agent gained domain dominance in under an hour without a single human intervention on a corporate network, bypassing EDR controls via on-the-fly tactic adaptation. Deepfake social engineering, automated ransomware attacks, and AI-based vulnerability scans are becoming mainstream. These attacks are too fast for a slow response model.
- Fileless & Memory-Only Malware. More and more attacks have no ‘file footprint’ for scanners to detect. In fileless attacks, malware runs in memory using legitimate system tools (PowerShell, WMI, etc.) and is therefore ‘invisible’ to AV software. The result is an attack with a small footprint, which avoids signature-based AV software and is fully integrated with legitimate system activity.” The use of fileless malware techniques has grown by approximately 78% from 2024 to 2026, and the use of in-memory exploits is continuously growing. Traditional defenses with a focus on files are largely unaware of these attacks.
- Zero-Day Exploits. Software vulnerabilities unknown to defenders are prime targets. In 2025, 90 zero-day vulnerabilities exploited in the wild, with many of them affecting enterprise software. These bugs are not patched at first, giving attackers free rein until a defender catches up. Zero-day exploits are particularly dangerous because attackers target unaware systems, giving defenders no time to react until after the vulnerability is discovered and patched.
- Supply Chain & Hybrid Attacks. Threats are increasingly using hybrid approaches. For instance, there were attacks in 2025 that were called “remote encryption attacks,” where attackers were able to lock network files from a single unmanaged “jump box” that attackers used. In such scenarios, there was simply no malicious process for the endpoint agent to quarantine on the endpoint.
As a result, the old “detect and respond” approach is not working. In the new world, attackers act in minutes, often without any explicit malware file to detect. The best EDR teams can be seconds or actions too late.
Xcitium’s Post-EDR Approach: ZeroDwell Isolation
This is exactly what Xcitium does. Its approach is based on a default deny virtualization architecture. The underlying philosophy of default deny virtualization is that you never trust anything unknown. That is, all executables that are not 100% known to be safe are immediately isolated in a kernel-level virtualization where they can execute safely, yet cannot cause harm.
Xcitium agent uses a variety of approaches to identify known good binaries as well as known malware. However, what’s most important is that, in a pre-execution approach, it checks all requests from a process to execute runtime privileges. If a file or process is not 100% safe or 100% malicious, it’s considered unknown. That unknown file executes inside a virtual environment created by the kernel itself. That unknown code runs as well as it would on the actual host system, yet it cannot modify or infect anything critical.
Meanwhile, Xcitium Verdict Cloud uses multiple AI engines to analyze the unknown in real-time and then declare it safe or malicious. If it is safe, then it runs natively. If it is malicious, then it is quarantined instantly. In either case, any malicious actions are quarantined in the environment, completely eliminating threats such as zero-days or ransomware before they can be unleashed. This approach offers complete protection against zero-day threats, actively prevents damage, and has zero impact on end-user experience. In short, Xcitium now moves from “detect and respond” to “prevent and protect” by never trusting unknowns to run natively.
Xcitium also protects critical data on network shares and shared drives. Any write operation is intercepted and validated in memory before it reaches disk, ensuring that ransomware or other malicious processes cannot encrypt or corrupt shared files.
This feature not only covers completely managed end points, but it is also valid for unmanaged endpoints including contractor’s laptops or Bring Your Own Device (BYOD). With a secure execution layer as well as a secure data layer, Xcitium creates a full architecture for preventing ransomware.
Revolutionizing Endpoint Security: Xcitium’s Post-EDR Kernel-Level Virtualization
This zero-trust virtualization approach gives Xcitium several powerful advantages over traditional vendors:
- Proactive Isolation of Unknowns. With its deny-by-default policy, Xcitium only allows files that have been explicitly whitelisted. As a result, it is able to neutralize any threats before they can cause any problems. Any unknown executable file will be automatically isolated in a virtual environment so that it is unable to do any damage to the computer system.
- Reduced Reliance on Detection. Xcitium doesn’t rely on detection. In contrast to scanning for attacks, this solution treats any operation which wasn’t identified before as a suspicious activity. Safe applications can execute freely, but all others operate under safe conditions. Such approach minimizes blind spots which cybercriminals take advantage of in other systems like EDR. For instance, even “living-off-the-land” attacks with the use of PowerShell, WMI, or similar technologies operate in the environment.
- Minimized False Positives. Since Xcitium isolates rather than directly blocks unknown files, the likelihood of false positives is greatly diminished. The file in question will run within the sandbox and, if deemed safe, continue functioning as normal. This approach avoids the excessive heuristics often used to block files, which rarely have any false positive effects.
- Automated Verdict & Response. The entire process of isolation decision-making is fully automated. Right after the detection of an anomaly, Xcitium starts analyzing it in-depth using its multi-layer analysis approach and provides its verdict. There is no need for analysts to determine if the file can be trusted; all decisions about isolations are made instantly by Xcitium.
- Low Performance Impact. Even though the process of virtualizing code happens at the kernel level, the system designed by Xcitium is designed for lightness. The isolation agents are quick and efficient when deployed using cloud-based updates. There is seamless productivity, where unknown files operate simultaneously without affecting the performance of the endpoint. No virtual machines need to be created per endpoint.
- Resilience against AI-driven Threats. Xcitium’s model is inherently strong against advanced AI attacks. Since no unknown process ever runs untrusted, an AI-powered malware cannot simply launch freely or adapt in the background. Even if an AI-enabled attacker succeeds in finding a new attack vector or writing a sophisticated script to bypass detection, it is always confined within the protective environment of Xcitium.
In summary, Xcitium’s ZeroTrust design is a revolutionary approach to protecting endpoints. By treating unknown threats with the highest suspicion and using kernel-level virtualization to isolate them, Xcitium provides preemptive protection that other vendors lack. Critical data on network shares and shared drives is also protected, with write operations intercepted and validated in memory before reaching disk, ensuring that ransomware or other malicious activity cannot encrypt or corrupt business-critical files.
The advantages are obvious protection against any type of zero-day and fileless attacks, low number of alerts, and completely automatic security posture tailored to meet the challenges of the era. This is why, compared to traditional AV or even modern EDR solutions, Xcitium’s ZeroDwell platform offers uniquely robust security for the endpoints of 2026 and beyond.
Conclusion: Endpoint Security Had to Evolve, Because Attackers Did
Signature based antivirus was built for known malware, it worked by matching files to a database that always arrived late for anything new. EDR improved visibility by monitoring behavior and activity, but it is still reactive. The file has to misbehave first, and the alert storm forces heavy human intervention while attackers increasingly evade detection through fileless and living off the land tradecraft.
Why the Post EDR Era Is Here
The threat landscape now moves faster than response models can keep up.
- AI driven attacks automate the full chain and can adapt in real time.
- Fileless and memory only techniques are rising fast, with fileless malware techniques noted as growing by about 78% from 2024 to 2026.
- Zero day exploitation is operational, with 90 zero day vulnerabilities exploited in the wild in 2025.
- Hybrid and remote encryption scenarios can bypass the classic endpoint detection model entirely.
The New Standard
The future of endpoint security is not faster detection. It is architectural certainty that blocks damage before it starts. Move from detect and respond to prevent and protect, and make unknown execution safe by design.