Breach Confirmed: Trellix Code Repository Accessed
Trellix recently announced that an unauthorized party accessed part of its source code repository. The company immediately engaged forensic experts and law enforcement after detecting the intrusion. Trellix acknowledged that the attackers obtained “a portion” of the repository, an event that raises serious concerns about security and trust.
Trellix has not disclosed when or how the breach was first detected. The company said it “recently identified” the unauthorized access and began an investigation immediately. Key details remain unclear. Trellix has not revealed whether any customer or corporate data were taken, nor if any ransom was demanded.
For now, Trellix says only that it will share more information “as appropriate” once the investigation concludes. In the meantime, analysts emphasize that even a partial code leak can carry risks for both Trellix and its clients.
Industry Trend: Other Security Firms Targeted
Attackers increasingly aiming at cybersecurity companies. In late April, Checkmarx confirmed that hackers gained access to its private GitHub repository and later posted stolen code on the dark web. Around the same time, Cisco disclosed a breach of its internal development environment attackers obtained parts of its source code by exploiting credentials stolen in a supply-chain attack on the Trivy open-source scanner.
In March, bug-bounty platform HackerOne notified employees that a breach at its benefits administrator (Navia) exposed personal data including Social Security numbers. Even the precursor to Trellix faced a major hack: in 2020, the FireEye network-security arm lost its internal red-team tools to suspected state-sponsored attackers.
- Checkmarx: In April 2026, application security vendor Checkmarx disclosed that hackers had stolen code (source) from their GitHub repo, which was later posted to the dark web.
- Cisco: Recently, networking vendor Cisco announced that cybercriminals were able to gain access to its internal development environment, stealing code via open-source vulnerability.
- HackerOne: Mid-March saw HackerOne report that hackers gained access to their benefits provider (Navia), and leaked employee personal data including Social Security numbers.
As can be seen from the examples above, it is not only the development processes themselves that are under threat but also the security vendors who have been targeted with malicious intent.
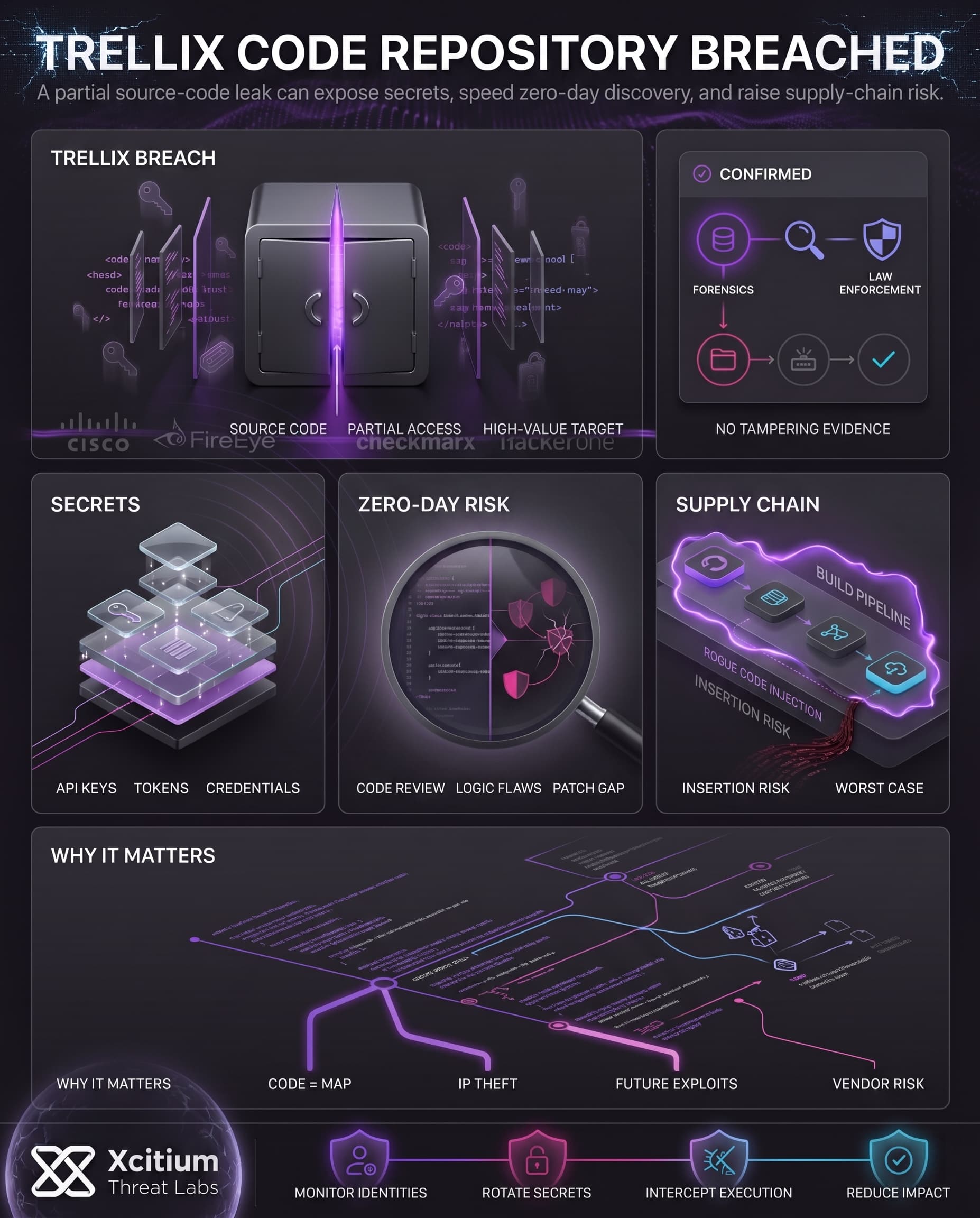
Technical Impact: Why Exposed Code Matters
Even though Trellix reports “no evidence” of code tampering, leaked source code can create serious long-term vulnerabilities. Repositories often contain sensitive data beyond mere code. Researchers note that code repositories can store API keys, authentication tokens, and other credentials that are effectively backdoors if discovered. If any such secrets were exposed, attackers could use them to infiltrate Trellix’s systems or its customers’ networks.
Moreover, exposed code allows adversaries to scrutinize the software for undiscovered flaws. With a copy of Trellix’s code, criminals might hunt for zero-day bugs or logic vulnerabilities before the company even knows they exist. Any new weaknesses found could then be exploited in the wild while patches are being prepared.
Trellix says its build-and-release processes were not compromised, but the very possibility of a supply-chain insertion remains a concern. In a worst-case scenario, a malicious actor with deep access could insert rogue code into a future software update, though Trellix reports no evidence of this having happened.
Risks that analysts point to include:
- Embedded secrets: Hackers usually discover API keys or passwords that are hard-coded in the code. This makes it possible for them to gain more access to the system.
- Discovery of vulnerabilities: Using full source code, hackers may be able to reverse-engineer their algorithms and identify any vulnerabilities that they can use before patches have been released.
- Supply chain attack: If the attack had penetrated the release process, the hackers would have been able to incorporate malicious code into updates. According to Trellix, this did not happen.
- IP theft: Encryption or proprietary algorithms used by Trellix in their products may have been disclosed to rivals.
These technical consequences show that Trellix should take the incident seriously even if it involves leaking only part of its source code.
Conclusion: When a Security Vendor’s Code Becomes the Target
The Trellix breach shows why source code is now one of the most valuable assets attackers can steal. Even when there is no confirmed tampering, unauthorized access to a security vendor’s repository creates long-term risk, because code reveals how products are built, where assumptions live, and where future weaknesses may be found.
Why This Threat Matters
A partial code leak can still create serious exposure.
- Repositories may contain API keys, tokens, credentials, and internal secrets that can act like persistent backdoors.
- Exposed source code gives adversaries time to search for zero-day flaws and logic weaknesses before defenders can patch them.
- If release processes are ever reached, supply-chain insertion becomes the worst-case scenario, even though Trellix reported no evidence of code tampering.
Why Security Vendors Stay Exposed
Attackers target cybersecurity companies because their repositories hold both intellectual property and operational leverage. The same industry pattern has affected Checkmarx, Cisco, HackerOne, and FireEye, showing that defenders themselves are now high-value supply-chain targets.
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed the same way.
With Xcitium Advanced EDR, malicious code, rogue tooling, and post-compromise payloads can run without being able to cause damage. With Xcitium Identity Threat Detection and Response, suspicious identity behavior around repositories, tokens, and developer access can be detected before theft turns into wider compromise.
- Source code access attempts become identity risk signals
- Follow-on malware and persistence attempts lose execution impact
- Stolen secrets are less likely to become real access when identity behavior is continuously monitored
Protect the Codebase Like Production
Source code is not just intellectual property. It is a map of how your defenses work. Secure developer identities, monitor repository access, rotate exposed secrets quickly, and enforce execution control before stolen code becomes tomorrow’s exploit path.