A recent campaign exploited a simple habit: downloading “gaming helpers” in a hurry. Attackers disguised malicious files as familiar tools and pushed them through browsers and chat platforms. After execution, the infection ran in stages and ended with a Java-based remote access trojan (RAT).
A RAT can remotely control a device. It can also steal data and download more malware. Consequently, a personal gaming PC can become a path to account takeover.
Why Gaming Lures Spread Fast Through Browsers and Chat
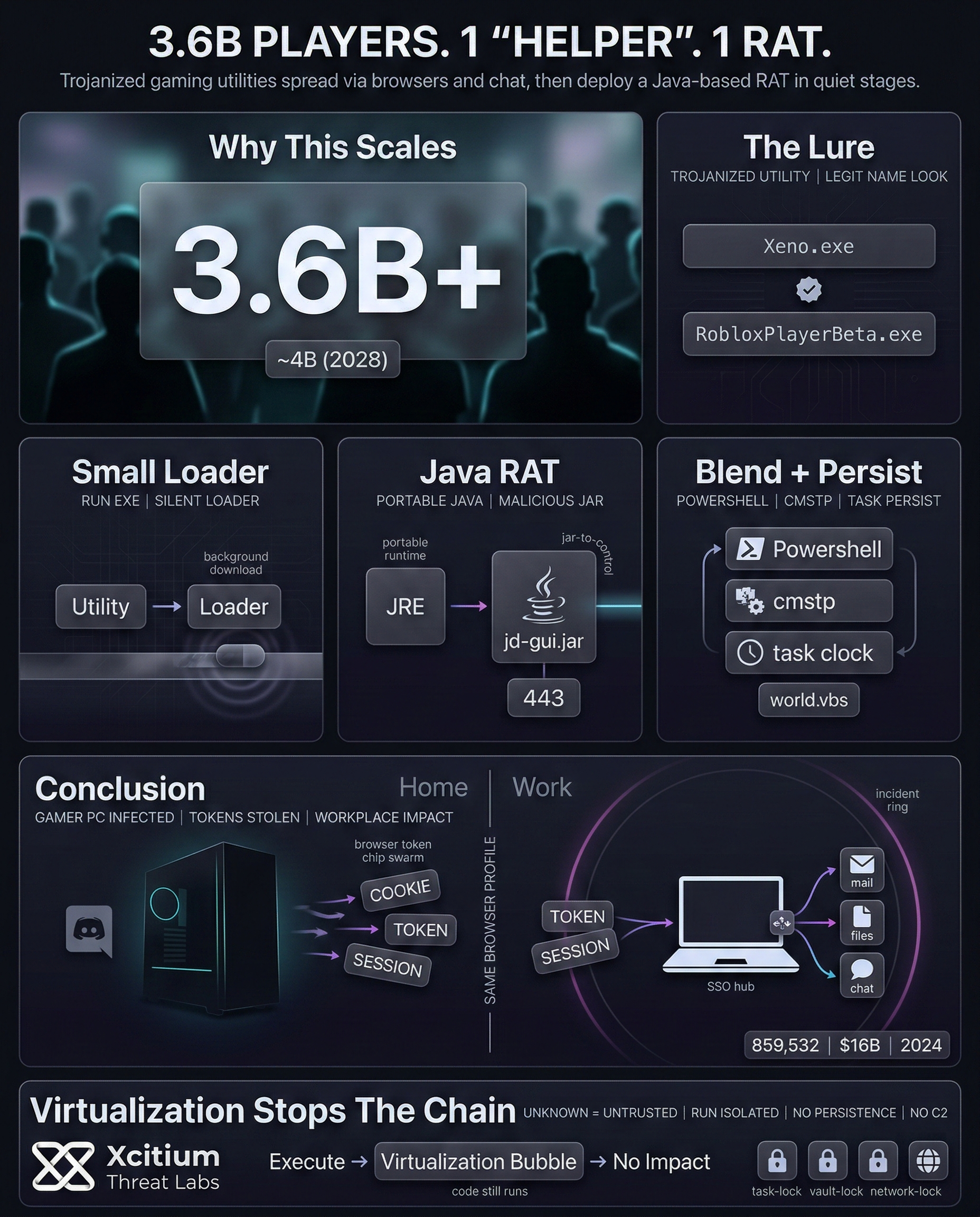
The gaming world has a huge following, so the scope for small campaigns is large. According to the forecasts, the gaming world has 3.6+ billion players, and it will reach almost 4 billion by 2028.
Sharing via Chat has the advantage of establishing trust immediately. If everyone wants the same mod or shortcut, the link appears legitimate. Many also come from outside the store.
In this activity, the lure had the following names, which seemed legitimate: “Xeno.exe,” “RobloxPlayerBeta.exe.”
The Attack Chain in Plain English: From Fake EXE to Full Control
This process is carried out by a “staged loader” designed for quiet operation and persistence.
- A trojanized “gaming utility” is executed and starts the “small downloader”.
- The “small downloader” installs the “portable Java environment” before executing the “malicious JAR file” renamed “
jd-gui.jar.” - Next, it uses PowerShell and a legitimate Windows tool (cmstp.exe) to blend in.
- It deletes the initial downloader to remove an obvious trace.
- Persistence arrives via a scheduled task plus a startup script named “
world.vbs.” - Finally, the RAT contacts attacker infrastructure for commands, theft, and more payloads.
Portable Java is a good option too. If Java is not installed, the malware provides its own runtime environment. Hence, the JAR file can run on more systems.
The naming of the files is strategic too. The string ‘jd-gui.jar’ might not attract suspicion within a directory filled with downloads from the Internet. Additionally, the traffic from the command might blend in with general web surfing activity if the ports used are common ones, like port 443.
Why The Stealth Techniques Look “Normal” to Many Defenses
Instead, the chain relied on common system resources. PowerShell, for example, is frequently exploited for execution. In the same way, cmstp.exe can be used as a proxy for execution, which can look legitimate.
Settings changes were also part of the equation. This action adds antivirus exclusions for the main components, which can limit the number of interruptions later on.
Finally, the persistence mechanism was based on a common pattern. Scheduled tasks, for example, can be set up to run a program on logon or on a timer. Therefore, new tasks with random names should be reviewed promptly, especially after a suspicious install.
Why a “Gamer PC” Infection Can Become a Workplace Incident
This appears to be consumer-oriented. However, many people tend to blend their personal and professional activities on a particular device. For example, email sessions, cloud logon credentials, and saved passwords might be saved within the browser.
After a RAT attack, the following scenarios become possible:
- Theft of credentials saved within the browser
- Capture of keystroke input or clipboard input during the logon process
- Download of additional tools to extend the attack surface over time.
The numbers add up because social engineering attacks are profitable. For example, within the United States, a federal reporting center recorded 859,532 complaints with losses over $16 billion in 2024. As a result, “run this file” attacks remain profitable.
Case Study: Xcitium vs. Trojanized Gaming Utilities (RATs)
This demonstration shows how Xcitium protects endpoints against staged, gaming-themed malware campaigns that ultimately deploy a Java-based Remote Access Trojan (RAT).
In this test scenario, a trojanized “gaming helper” is executed to simulate a real-world user download from a browser or chat platform. The infection chain includes a staged loader, a portable Java runtime, a malicious JAR payload, use of legitimate Windows tools such as PowerShell and cmstp.exe, persistence mechanisms, and outbound command-and-control attempts.
Rather than relying on signatures or delayed detection, Xcitium’s ZeroDwell technology immediately classifies the unknown files as untrusted at launch and runs them in isolation.
As a result, persistence is never established, credentials are not exposed, and external communication does not succeed even though the malware chain is fully functional.
This video demonstrates how modern social engineering–driven RAT infections are neutralized instantly through continuous zero-trust execution and real-time isolation.
Indicators of Compromise (IOCs)
- worldview.db-wal/StandardName.exe (SHA-256: 4442ba4c60a6fc24a2b2dfd041a86f601e03b38deab0300a6116fea68042003f)
- jd-gui.jar (SHA-256: a33a96cbd92eef15116c0c1dcaa8feb6eee28a818046ac9576054183e920eeb5)
- decompiler.exe (SHA-256: 48cd5d1ef968bf024fc6a1a119083893b4191565dba59592c541eb77358a8cbb)
- world.vbs (SHA-256: 65f003998af7dd8103607c8e18ef418b131ba7d9962bd580759d90f4ac51da36)
- powercat[.]dog:443; remote IP 79.110.49[.]15
Conclusion: When “Helper Tools” Become a Multi-Stage Backdoor
This campaign shows how fast a harmless habit can become full remote access. Trojanized gaming utilities delivered a staged loader, installed a portable Java runtime, then executed an obfuscated JAR that ultimately deployed a Java-based RAT, all while blending into normal browser and chat driven downloads.
Why This Threat Scales So Easily
The lure spreads through trust, not exploits. Gaming communities share links quickly, and chat distribution makes malicious downloads feel legitimate. With billions of players globally, even small campaigns can reach huge numbers of endpoints.
Why This Becomes an Enterprise Problem
A personal gaming machine compromise can spill into work accounts the same day.
- Browser stored session cookies and cloud tokens can be stolen
- Keylogging and clipboard capture can intercept corporate logins
- The RAT can pull additional tools over time, expanding the attack surface
- Reported 2024 losses show “run this file” social engineering remains highly profitable
Where Xcitium Changes the Outcome
If you have Xcitium, this attack would NOT succeed.
With Xcitium Advanced EDR in place, unknown staged loaders and Java based payloads are isolated at execution. Persistence never establishes, credentials are not exposed, and outbound command and control does not succeed. Code can run without being able to cause damage.
Stop the First Stage, Stop the RAT
Modern RAT campaigns win by getting the first file executed. Reduce risky downloads, restrict execution of untrusted utilities, and enforce execution time control that prevents staged malware from becoming remote access.