Continuous Malware Research delivering Early Warning, Actionable Intelligence, and Preemptive Protection against emerging cyber threats Worldwide.
Modern Workflows Halted by Exchange Online Disruptions Recently, Microsoft has faced a major...

Interpol organized Operation Synergia III, a worldwide crackdown (Jul 2025 – Jan 2026) that...
The campaign combines social engineering with evasion techniques. Victim is presented with normal...

Recently, independent research on McKinsey & Company’s internal AI platform, Lilli, found...

Massive Cyber Breach Strikes Medical Giant Stryker On March 11, 2026, Stryker, which is considered...

Salesforce recently issued a warning that attackers are targeting Experience Cloud (Aura)...
What the FBI is Warning About and Who Gets Targeted Recently, the Federal Bureau of...

When Legitimate Notifications Become the Attack Surface Phishing has transitioned from spoofing...

Why This Campaign Matters Beyond the Headlines Recent reporting links the Iran-aligned group...

Recently, reports linked a major Mexico data theft to misuse of an AI coding assistant,...

Understanding the LexisNexis Data Breach LexisNexis, a leading legal and risk management solution...
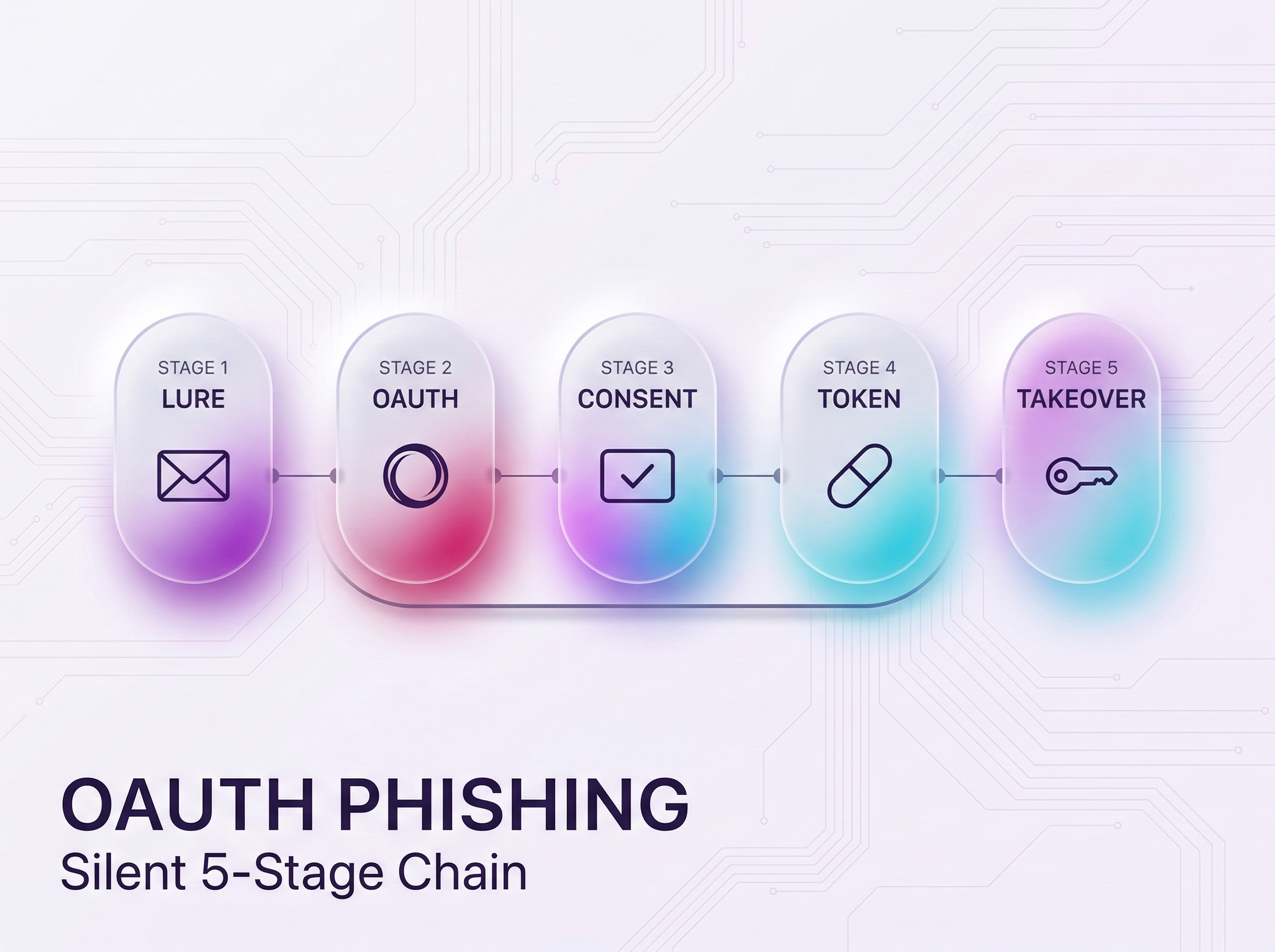
New OAuth Phishing Attack Exploits Authentication Trust A new sophisticated phishing attack has...
Xcitium exists to ensure that people can embrace technology fully, without the shadow of insecurity hanging over them. We’re here to give users the freedom to explore, create, and connect without fear. Whether it’s preventing unknown files from compromising systems or offering innovative approaches to endpoint protection solution, Xcitium’s technology is designed to foster confidence. We believe that by keeping the digital ecosystem secure, we’re directly contributing to human evolution—by enabling people to take full advantage of the tools that define our era.
Book a Demo