Continuous Malware Research delivering Early Warning, Actionable Intelligence, and Preemptive Protection against emerging cyber threats Worldwide.

In this ever-changing landscape of cyber security, the inclusion of artificial intelligence in our...
A recent campaign exploited a simple habit: downloading “gaming helpers” in a hurry. Attackers...
A New Era of Kinetic Warfare: Cloud as a Military Target For the first time, cloud infrastructure...

Generative AI is moving into operations. Recently, reporting around Operation Epic Fury said...

Fresh reporting links the Lazarus Group to Medusa ransomware activity aimed at healthcare...
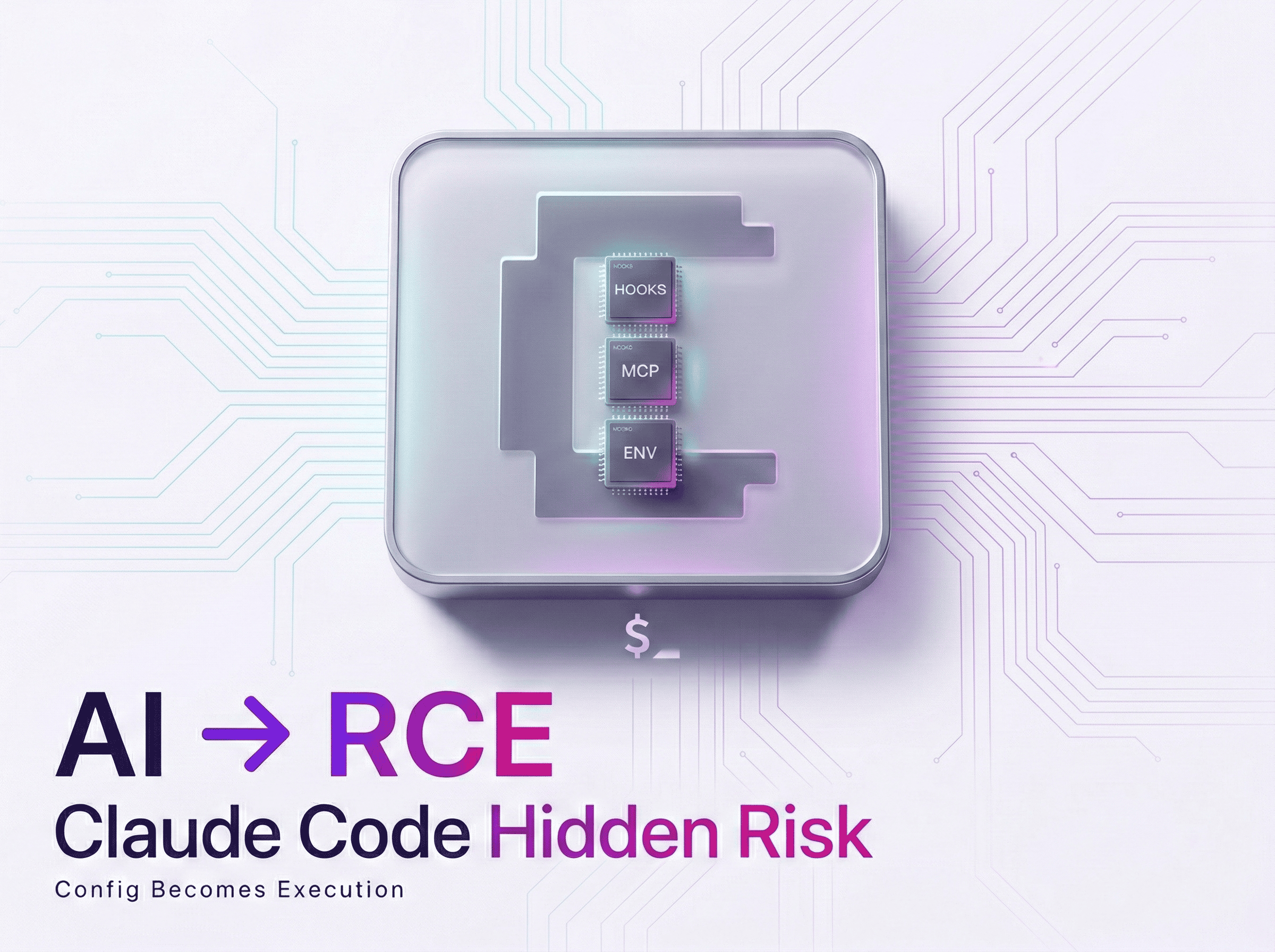
The Alarming Discovery: Claude Code’s Hidden Dangers Recently, there have been discoveries of...
Compromised VPN Access and EDR Killer Deployment Recently, it has been determined that the...
According to a recent FBI alert, U.S. banks saw an unprecedented increase in such attacks last...
The recent changes in the cybersecurity world came about due to a massive update in the Conduent...

What Are Reverse Phishing Attacks? In traditional phishing scams, attackers trick victims into...
Recently, a sophisticated operation known as Arkanix Stealer, which surfaced on various dark web...

A Silent Security Failure at PayPal Recently, PayPal confirmed its data breach and its impact on...
Xcitium exists to ensure that people can embrace technology fully, without the shadow of insecurity hanging over them. We’re here to give users the freedom to explore, create, and connect without fear. Whether it’s preventing unknown files from compromising systems or offering innovative approaches to endpoint protection solution, Xcitium’s technology is designed to foster confidence. We believe that by keeping the digital ecosystem secure, we’re directly contributing to human evolution—by enabling people to take full advantage of the tools that define our era.
Book a Demo