Understanding the LexisNexis Data Breach
LexisNexis, a leading legal and risk management solution provider, has confirmed a major data breach in the recent past. This breach came to light when hackers made public disclosures claiming that data had been stolen from the company’s systems.
This is evidence of the ever-present threats facing businesses in the cyber world. Therefore, it is important to have a clear insight into the nature of the breach for both entities and individuals.
How Did the Attack Unfold?
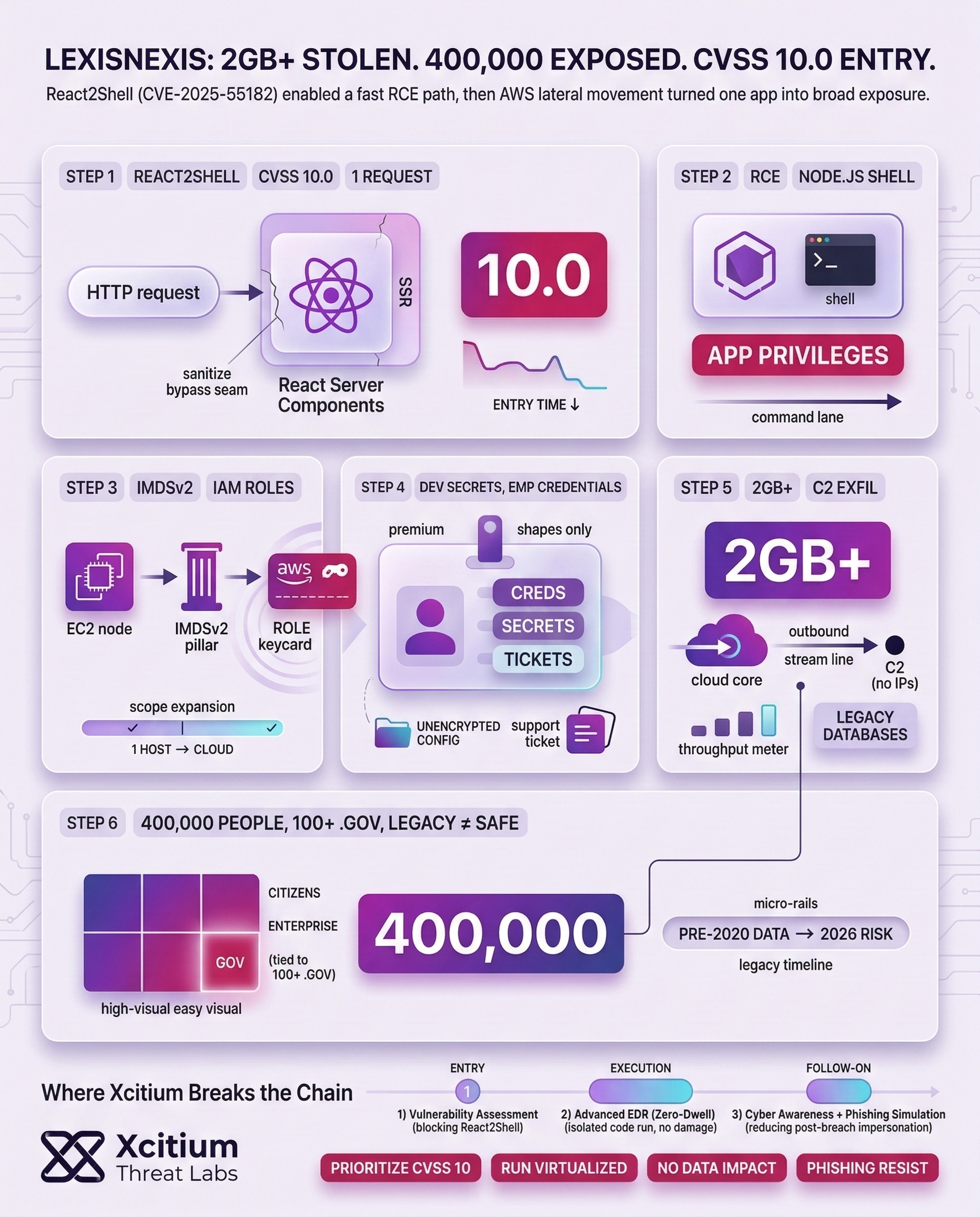
The actors involved in the intrusion revealed their activities on a cybercrime forum, which revealed the extortion plan against LexisNexis, though it did not come to pass. According to the actors, the extortion plan would involve the ‘React2Shell‘ vulnerability, also known as CVE-2025-55182, and AWS instances, which would allow the actors to access the system illegally. This critical vulnerability has a CVSS score of 10.0, allowing attackers to execute the code on the target system with a single, specially crafted HTTP request. Exploiting this vulnerability is a matter of high severity.
What Data Was Compromised?
LexisNexis Legal & Professional stated that the systems that the breach impacted contained legacy information that was deprecated prior to 2020. However, the compromised information included sensitive information, which included customer names, user identifiers, business contact information, IP addresses of survey respondents, and support tickets.
Moreover, the hackers claimed that they had obtained over 2 gigabytes of information, which included information such as enterprise account information, employee credentials, software development secrets, as well as information relating to 400,000 individuals. Notably, the information included over 100 individuals who had .gov email addresses.
The Broader Implications of Data Breaches
The consequences of data breaches may include reduced customer loyalty and financial loss.
In addition, the release of information may lead to a number of cyber threats, including phishing and identity theft. Thus, a number of steps must be taken to ensure the security of the organization.
A Recurring Challenge for LexisNexis
LexisNexis has previously faced data security breaches. In 2025, LexisNexis Risk Solutions acknowledged another data breach at a third party, which resulted in stolen data from over 360,000 people.
This is another indication that data security is always needed, and this is where we learn from past security breaches to improve security in the future.
The “React2Shell” Vulnerability: A Closer Look
The React2Shell vulnerability, officially denominated CVE-2025-55182, is a critical flaw in the React Server Components application. This vulnerability enables any unauthorized hacker to run arbitrary code on any server that has not been patched.
This vulnerability has been rapidly exploited by a number of cybercriminal groups, including the China-nexus cyber threat groups. Therefore, any organization using React Server Components must ensure timely patching and implement adequate security measures to avert this serious vulnerability.
Conclusion: When “Legacy Data” Becomes Fresh Risk
The LexisNexis breach is a reminder that old systems and deprecated datasets still create real exposure. LexisNexis stated the impacted systems contained legacy information deprecated prior to 2020, yet the compromised data still included customer names, user identifiers, business contact information, IP addresses, and support ticket content.
Attackers claimed more than 2 GB of data, including enterprise account information, employee credentials, and software development secrets, with potential exposure affecting roughly 400,000 individuals.
Why This Threat Matters
This event highlights the convergence of two high-impact realities.
- Critical RCE vulnerabilities like React2Shell, CVE-2025-55182, enable fast entry when systems are not patched.
- Once data is stolen, the real damage is often in the follow-on phase, phishing, identity theft, and targeted impersonation become easier and more convincing.
Why Organizations Stay Exposed
Most security programs still underestimate dormant risk.
- Legacy platforms remain reachable longer than expected
- Deprecated data is not always deleted, it is often just moved
- Patch gaps on internet-facing systems collapse the timeline to compromise
- Sensitive metadata like tickets and contact records fuels long-term social engineering
Where Xcitium Changes the Outcome
With Xcitium in place, this attack would NOT succeed as a business-impact event.
- Xcitium Vulnerability Assessment helps ensure exposures like CVE-2025-55182 should have been visible and prioritized before attackers arrive.
- Xcitium Advanced EDR, powered by the patented Zero-Dwell platform, ensures that even if exploitation is attempted, code can run without being able to cause damage to real systems or data.
- Xcitium Cyber Awareness Education and Phishing Simulation reduces successful follow-on phishing by training users to verify high-trust messages that leverage leaked information.
Reduce Risk Before the Leak Becomes the Attack
Treat legacy systems as active attack surface. Patch critical RCE paths immediately, minimize retained data, and harden users against post-breach social engineering. That is how you prevent a breach from turning into an extended campaign.