A New Threat in Microsoft Defender
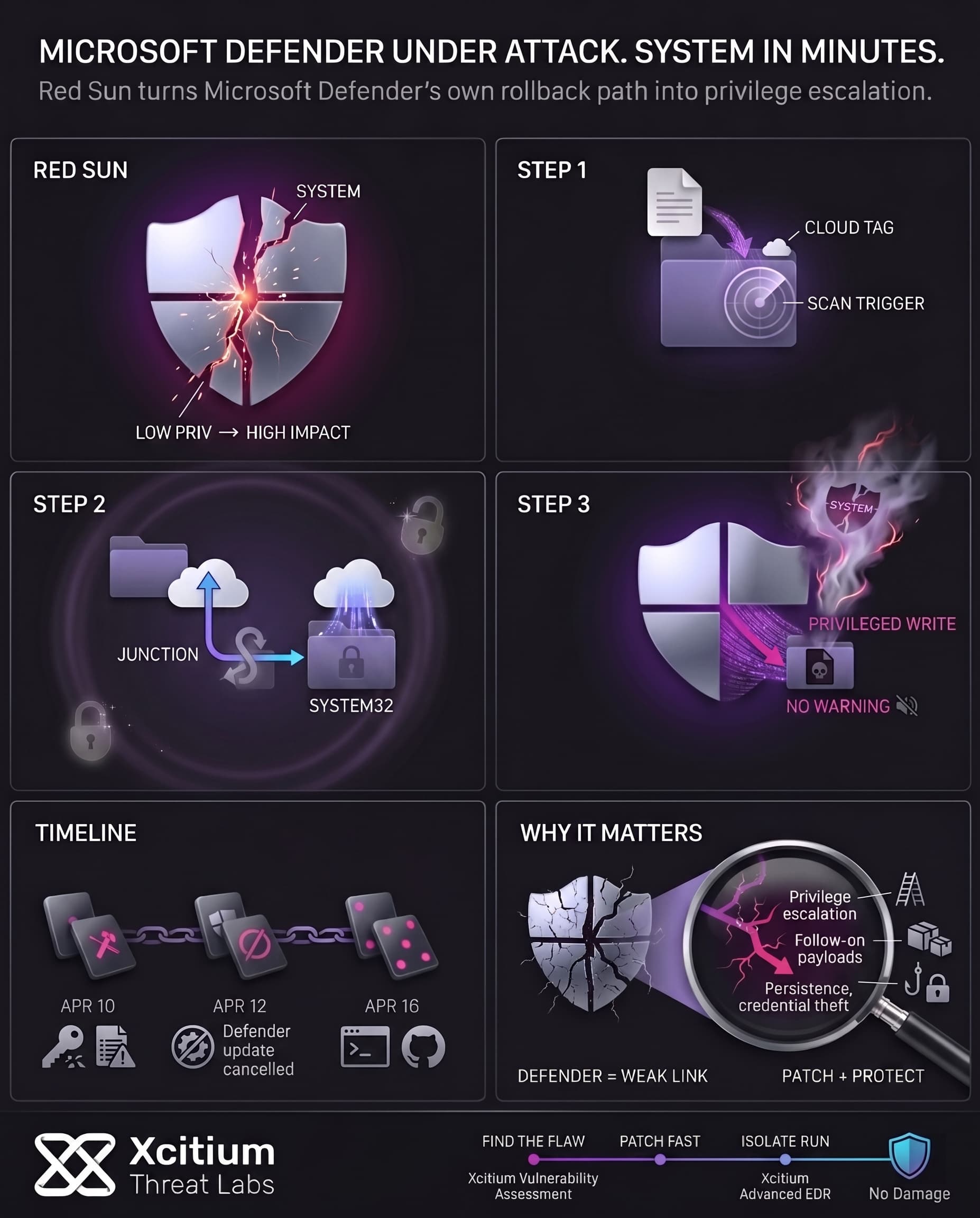
Windows Defender is the antivirus that comes pre-installed in any device using the latest versions of Microsoft’s Windows 10 and 11 operating system. Lately, a new flaw has come to light within Defender’s file handling mechanism. The bug, named “Red Sun,” allows a low-privilege attacker to gain SYSTEM level access through the cloud file rollback procedure of Defender.
Essentially, Defender can be manipulated to write malware back onto the system instead of isolating it from the computer’s protected paths. This will allow a hacker to overwrite system files and take control of a computer using Defender’s cloud rollback capabilities. Hackers are already trying to use the Red Sun exploit for their malicious activities.
How Red Sun Works: The Attack Chain
Red Sun exploits a quirk in Defender’s remediation routine. Here’s the simplified sequence of steps the attack takes:
- Trigger a scan: The attacker drops a harmless-looking file that invokes Defender’s real-time scanning. This file carries a special “cloud” marker so Defender treats it as a cloud-backed file.
- Replace with cloud placeholder: The original file is quickly deleted and replaced by a cloud-sync placeholder using Windows Cloud Files APIs. Meanwhile, the attacker sets up an NTFS junction pointing from the file’s normal folder to
C:\Windows\System32a protected system directory. - Pause and redirect: Defender spots the cloud-tagged file, decides it needs to “restore” it to its original location, and pauses its operation via an opportunistic lock. At that moment, the redirected junction silently reroutes the upcoming write.
- Privileged write: When Defender resumes, it writes the file (now attacker-controlled) into
System32instead of the original folder. Since Defender runs with SYSTEM privileges, the file is placed with full rights. - System takeover: The malicious file in
System32is then executed by a built-in Windows service. The exploit gains a SYSTEM shell, giving the attacker full control with no additional privileges needed.
“Cloud file rollback” in Defender does not validate the target path for recovery purposes and that becomes the core vulnerability leading to the problem. The attacker manages to manipulate the defender to serve his purpose of escalating privileges.
Red Sun attack does not require any administrator intervention, but only local access on the machine. Once launched, it runs until the SYSTEM shell pops up in the user session.
Exploits in the Wild: Timeline of Attacks
Several instances of live attacks using the discovered exploits have been reported.
- April 10, 2026: Attackers start using the previous “BlueHammer” exploit against patched systems. In one instance, an attacker used a malicious workstation running the BlueHammer exploit which then dumps a
FunnyApp.exestaging program and hashes. - April 12, 2026: The researcher publishes the UnDefend tool which denies the Defender from receiving patches, effectively keeping it from updating or even disabling its functions.
- April 16, 2026: The Red Sun exploit source code becomes available for download on GitHub. Analysts detect a live infection with RedSun exploit within several hours of the source code publication and observe that UnDefend was also used by the attacker in the process.
- April 16, 2026 (continued): An example of RedSun being used to escalate privileges on the infected machine proves that attackers took the published exploit and started using it right away.
All of the three exploits (BlueHammer, RedSun, and UnDefend) are actively tested in the environment after they were made public. In particular, it can be seen that the “hands-on-keyboard” operations are performed such as whoami /priv, net group, and other commands following the exploit.
An instance when a machine which was already compromised through a compromised VPN connection shows that the attacker uses both RedSun and UnDefend.
Why Red Sun Matters to Windows Users
Red Sun bypasses the default antivirus software on several machines and those which may already be considered “fully secured.” It even applies to patched versions of Windows 10/11 if Windows Defender is installed and itself not patched.
Once executed, the attack allows a person having only limited access to become SYSTEM privileged, thus opening doors for infection spreading, disabling security features, or information stealing without much hassle.
Important notes:
- Widespread use: With Windows Defender being default on more than one billion computers and remaining very popular, the vulnerability spreads far and wide.
- Minimal prerequisites: Red Sun does not require any administrator permissions to run and has no need for any kernel vulnerabilities.
- Critical level: The attack leads to gaining SYSTEM-level privileges, bypassing all possible defenses.
- Current patch status: An emergency patch for the related BlueHammer vulnerability (CVE-2026-33825) was issued by Microsoft in April 2026 Patch Tuesday. Until mid-April, however, there was no patch to address Red Sun or UnDefend.
Some note that even though this is a local exploit, the risk is real, if an attacker already has a toehold, they can use RedSun to instantly gain full control.
Conclusion: When the Security Tool Becomes the Weak Link, Defense Must Come From Outside It
Red Sun exposes a hard truth about endpoint security. If the protection layer itself can be abused to elevate privilege, then relying on that same layer to stop the attack is no longer enough. In this case, Microsoft Defender became part of the attack path, not the barrier to it.
Why This Threat Matters
This flaw is dangerous because it breaks trust at the exact point defenders expect safety.
- A low-privilege attacker can trigger a path toward SYSTEM-level control
- The exploit abuses Defender’s own rollback behavior
- Public exploit code lowers the barrier for rapid attacker adoption
- Once SYSTEM access is gained, persistence, credential theft, and follow-on malware all become easier
Why Visibility Alone Is Not Enough
This exposure should have been found before exploitation, but patching alone is not the whole story.
- Xcitium Vulnerability Assessment ensures the weakness is visible early
- Affected systems can be identified and prioritized for urgent remediation
- Gaps in coverage and patching become actionable before attackers move
But visibility only answers one question: where is the risk?
It does not answer the next one: what happens if the attacker gets there first?
Where Xcitium Changes the Outcome
This is where Xcitium Advanced EDR becomes the decisive control.
Windows Defender cannot reliably protect you from an attack chain that abuses Defender itself.
Xcitium can.
- The exploit may attempt to run, but code can run without being able to cause damage
- The attack chain breaks before SYSTEM-level abuse becomes business impact
- Follow-on payloads, persistence, and destructive actions never get the outcome the attacker needs
If you have Xcitium in place, this attack does not succeed.
Trust an Architecture the Attacker Cannot Turn Against You
Red Sun proves that security cannot depend on a control that can be repurposed as the exploit path. Find the weakness early. Patch it fast. Then enforce execution-time protection that keeps privilege escalation from becoming compromise.
Choose Xcitium Vulnerability Assessment and Xcitium Advanced EDR.