
When Legitimate Notifications Become the Attack Surface Phishing has transitioned from spoofing...

Why This Campaign Matters Beyond the Headlines Recent reporting links the Iran-aligned group...

Recently, reports linked a major Mexico data theft to misuse of an AI coding assistant,...

Understanding the LexisNexis Data Breach LexisNexis, a leading legal and risk management solution...
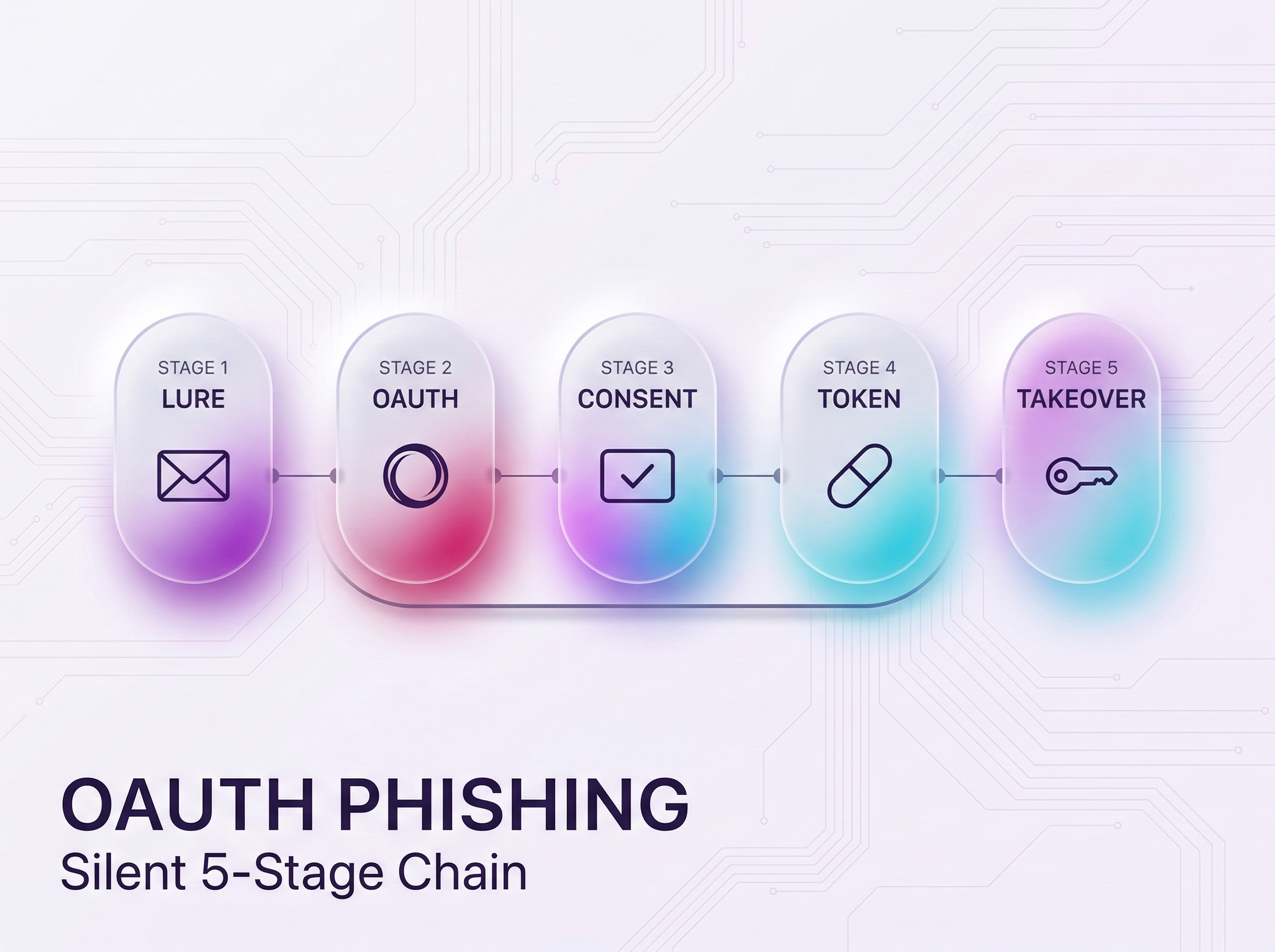
New OAuth Phishing Attack Exploits Authentication Trust A new sophisticated phishing attack has...

In this ever-changing landscape of cyber security, the inclusion of artificial intelligence in our...
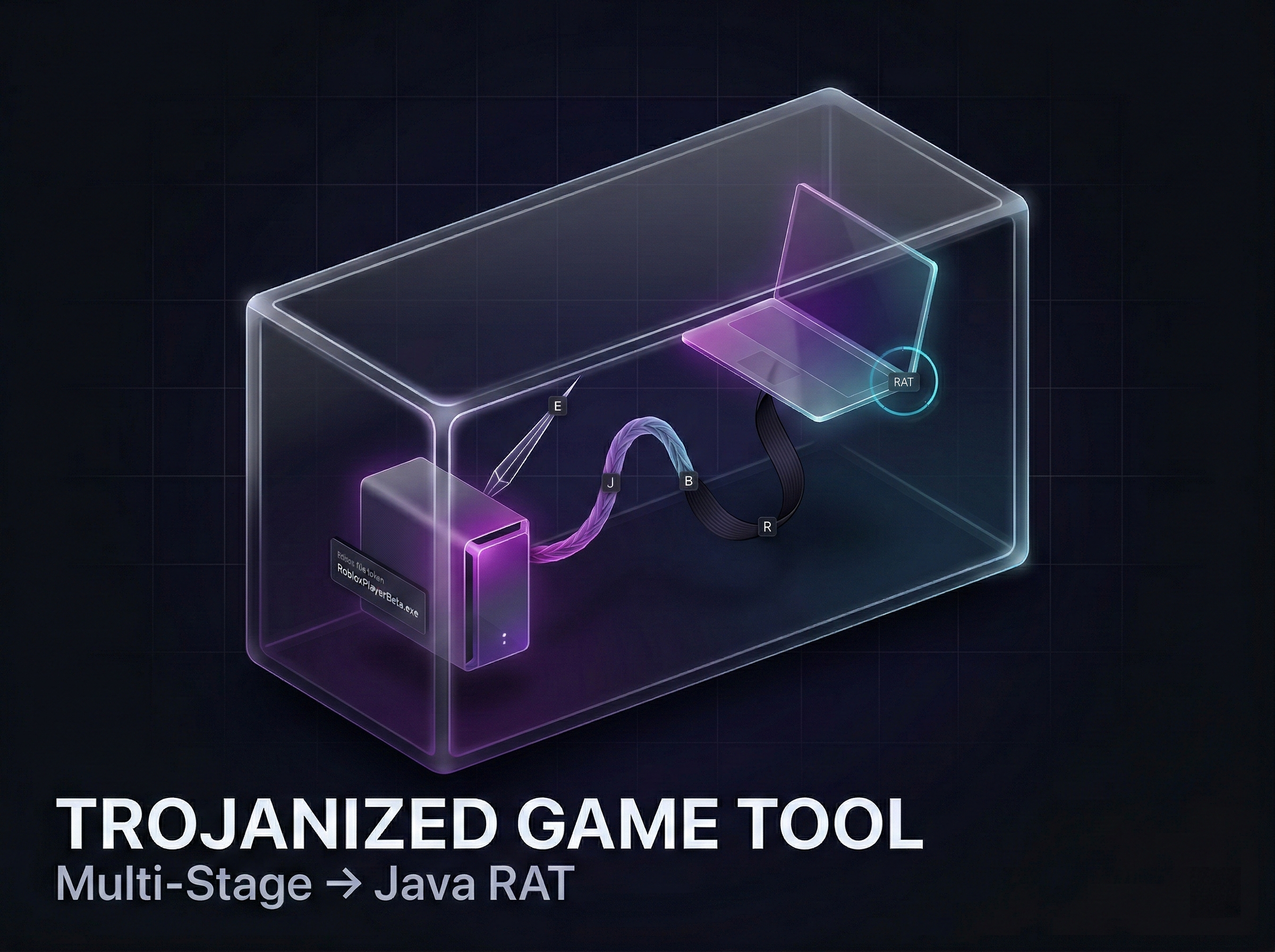
A recent campaign exploited a simple habit: downloading “gaming helpers” in a hurry. Attackers...
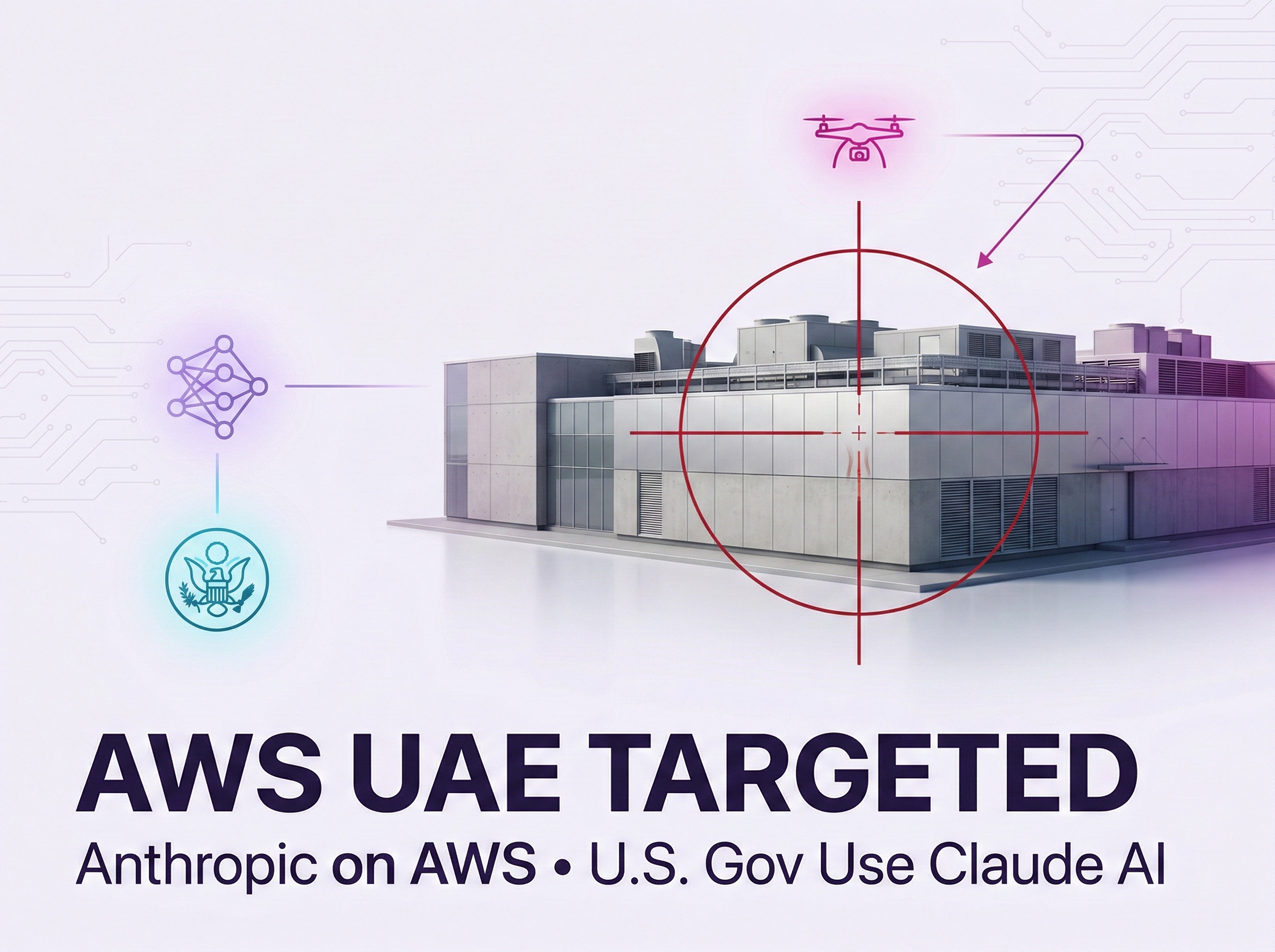
A New Era of Kinetic Warfare: Cloud as a Military Target For the first time, cloud infrastructure...

Generative AI is moving into operations. Recently, reporting around Operation Epic Fury said...